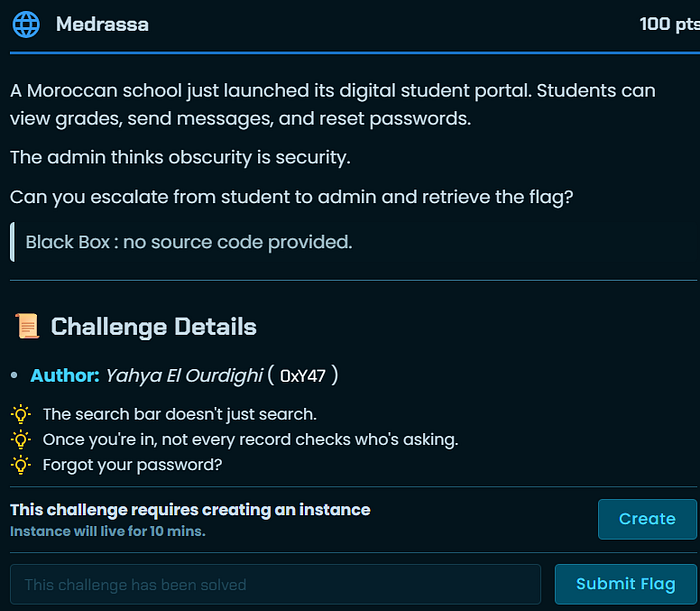
Category: Web Exploitation
Techniques Used: Directory Fuzzing · IDOR · Password Reset Hijacking · Broken Access Control
Introduction
This writeup covers the Medrassa web challenge from the ENSI CTF. The challenge required chaining multiple vulnerabilities together — IDOR, a broken password reset flow, and broken access control — to ultimately retrieve the flag. A classic example of how individually low-severity issues can combine into a full account takeover and data exfiltration.
Step 1 — Reconnaissance: Directory Fuzzing
The first step was to enumerate hidden directories and endpoints on the target web application
dirsearch -u http://192.200.14.57:30475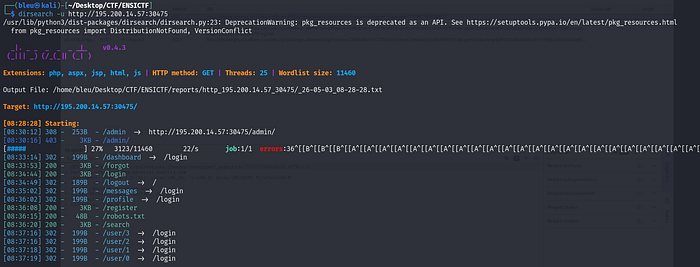
Two interesting findings immediately stood out:
/user/1— A user profile endpoint/robots.txt— Which disclosed a sensitive path:/api/
Step 2 — IDOR: Leaking the Admin Email
With the /api/ path in hand, the next move was to probe the API for user data. Navigating to:

returned the details of the first registered user — which turned out to be the admin account. This is a textbook Insecure Direct Object Reference (IDOR) vulnerability: the application exposes user objects by a sequential integer ID without any authorization check.
The response revealed the admin's real email address: admin@medrassa.local
Step 3 — Password Reset Hijacking
Armed with the admin email, the next step was to trigger a password reset for admin@medrassa.local and intercept the traffic using Burp Suite.
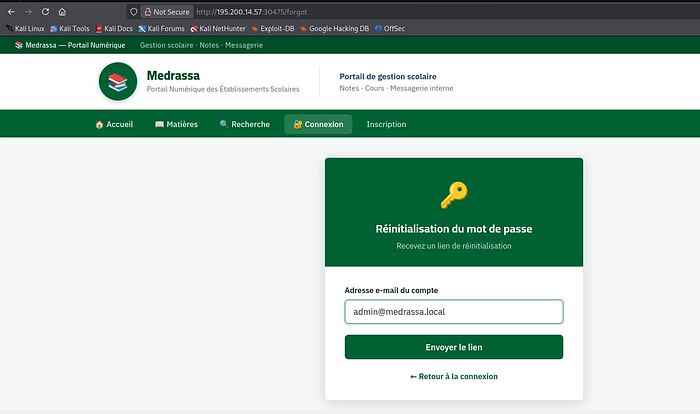
Intercepting the traffic with burp :
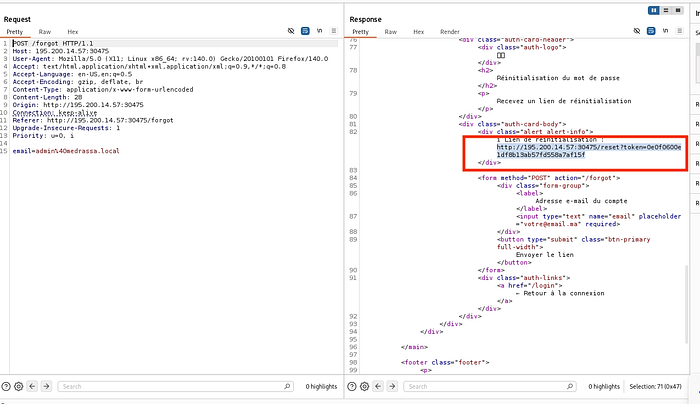
What happened:
- A password reset request was submitted for
admin@medrassa.local. - The HTTP response — rather than sending a reset link exclusively to the user's email — included the reset link directly in the response body.
- This meant the reset token was fully visible to whoever made the request, with no email verification required.
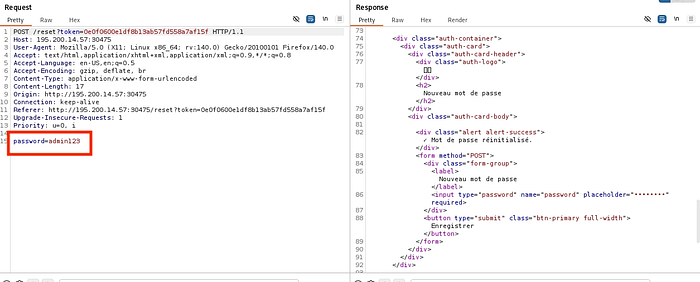
Following that link allowed setting a new password for the admin account, effectively a full account takeover without ever accessing the admin's inbox.
Step 4 — Accessing the Admin Panel and Exporting Grades
With admin credentials now in hand, logging in revealed a dashboard with a /grades endpoint — a page listing student grades, restricted to admin users only.
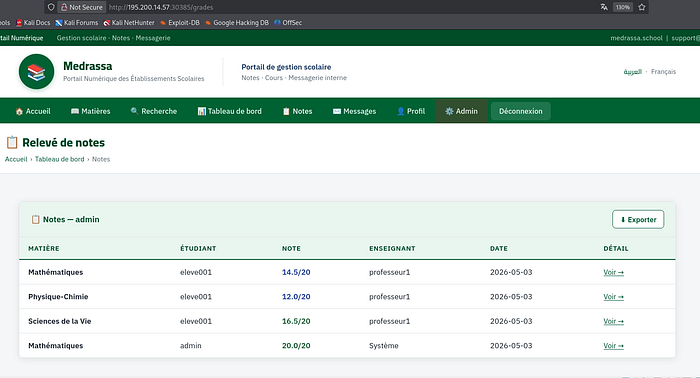
Clicking the "Export Grades" button was all it took. Since this feature was protected purely by authentication (only admins can access it), and we had already taken over the admin account in the previous step, there was nothing left to bypass. The export returned the flag directly:
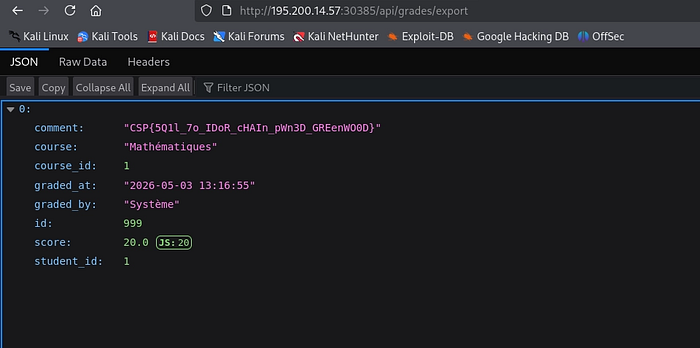
FLAG : CSP{5Q1l_7o_IDoR_cHAIn_pWn3D_GREenWO0D}
Vulnerability Chain Summary
Directory Fuzzing
│
▼
IDOR on /api/user/1 ──► Admin email leaked
│
▼
Password Reset Token in API Response ──► Admin account takeover
│
▼
Broken Access Control on /grades export ──► FLAG