Executive Summary
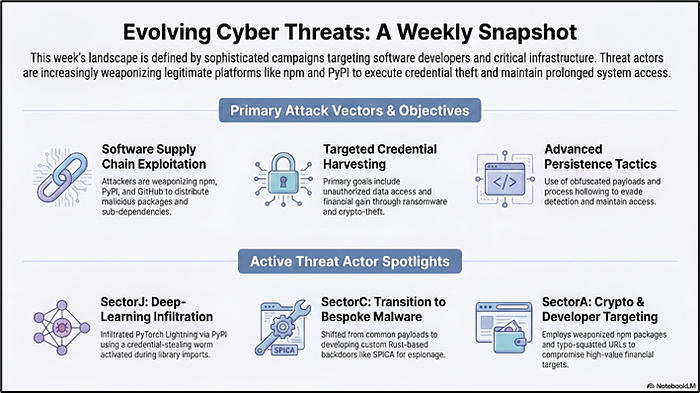
This week, the cybersecurity landscape has been marked by a series of sophisticated cyber threat campaigns targeting a diverse array of sectors, primarily focusing on software developers, cryptocurrency ecosystems, and critical infrastructure. The attackers have employed advanced tactics, techniques, and procedures (TTPs) to exploit vulnerabilities in software supply chains, leveraging platforms like npm, PyPI, and GitHub to distribute malicious packages and execute credential theft operations. These campaigns have demonstrated a high level of technical acumen, utilizing obfuscated payloads, dynamic domain registration, and advanced persistence mechanisms to evade detection and maintain prolonged access to compromised systems. The primary objectives of these threat actors appear to be credential harvesting, unauthorized access to sensitive data, and financial gain through ransomware and data exfiltration. The malware utilized in these attacks exhibits complex functionalities, including remote access trojans (RATs) with capabilities for screen capture, keylogging, and clipboard monitoring, as well as sophisticated data exfiltration techniques using encrypted communications and cloud-based services. Additionally, the campaigns have targeted cryptocurrency wallets and financial sectors, employing phishing tactics and social engineering to deceive victims into divulging sensitive information. The attackers have also demonstrated a keen ability to exploit cloud infrastructure and trusted platforms, such as AI distribution channels and legitimate software repositories, to stage their operations. This week's activities highlight the persistent and evolving nature of cyber threats, with attackers continuously adapting their strategies to exploit emerging technologies and vulnerabilities. The use of advanced obfuscation techniques, such as process hollowing and memory injection, further underscores the sophistication of these campaigns, posing significant challenges for cybersecurity professionals tasked with defending against such threats.
Hacking activities associated with the SectorA Group focus on highly sophisticated operations targeting software development environments and the cryptocurrency sector. The group uses various tactics, techniques, and procedures (TTPs) that demonstrate its technical capabilities and strategic targeting. One notable method is the weaponization of NPM packages. In this attack, legitimate-looking packages such as "es6-runtimejs" and "ether-bn.js" were manipulated to initiate an infection chain. These packages were designed to deceive developers into integrating them into their projects, leading to the installation of malicious sub-dependencies and the deployment of heavily encrypted malware such as "PylangGhost." This campaign highlights the group's capability to abuse cloud infrastructure for malicious purposes. Another tactic involves the deployment of a remote access trojan (RAT) through malicious NPM packages such as "node-env-resolve." This package masquerades as a legitimate tool but actually installs a persistent agent for remote control. The package aligns with the OtterCookie RAT toolkit, which is known for capabilities such as live screen streaming and audio capture, indicating a focus on comprehensive surveillance and control of infected systems. In a separate incident involving a malicious batch script, the use of obfuscated PowerShell commands further demonstrates the group's capability to evade detection and maintain persistence on compromised systems. SectorA Group also targets the cryptocurrency sector through sophisticated phishing attacks, as shown in incidents involving Zoom lookalike domains and manipulated Calendly invites. These attacks are characterized by advanced social engineering techniques, process injection, and the use of cloud-based services. Infrastructure analysis of the group reveals a globally distributed operational pattern, with significant overlap in tactics across multiple campaigns. Its focus on high-value targets in the cryptocurrency and financial sectors, together with media manipulation using AI-generated assets, underscores its persistent and financially motivated objectives. Overall, the activities of SectorA Group reflect a well-coordinated and technically advanced approach to cyber threats, leveraging a diverse range of tools and techniques to achieve its objectives.
SectorB Group demonstrated a sophisticated and evolving approach to cyber threats, primarily targeting government and military entities within the APAC region. Their tactics, techniques, and procedures (TTPs) were characterized by a blend of social engineering and technical exploitation. Initial access was frequently gained through spear-phishing emails and SMS messages, which were meticulously crafted to deceive recipients into executing malicious payloads. The group also employed physical network penetration methods, such as Evil Twin attacks and Wi-Fi exploitation, to gain unauthorized access to sensitive environments. A hallmark of their operations was the deployment of malware variants like Xiangoop, EntryShell, and Cobalt Strike Beacon, often delivered under the guise of legitimate app updates. These malware strains were integral to their strategy, enabling data exfiltration and command-and-control operations. In 2024, SectorB Group expanded their arsenal with DNS hijacking techniques, targeting home routers to redirect traffic to malicious update servers, thereby broadening their attack surface. By 2025, the introduction of Mythic Agents such as APOLLO and MERLIN marked a significant advancement in their capabilities, utilizing backdoor techniques with Cobalt Strike Beacon scripts to enhance stealth and persistence. The group's infrastructure was robust, relying on compromised servers and the reuse of IP addresses, which underscored their commitment to maintaining a persistent presence within targeted networks. Overall, the SectorB Group's activities during this period reflected a dynamic and adaptive threat landscape, with a clear emphasis on leveraging both traditional and innovative cyber attack methodologies to achieve their objectives.
SectorC Group has demonstrated a sophisticated evolution in their cyber attack methodologies, primarily focusing on state-driven espionage. Initially, their operations in 2017 were characterized by a less mature approach, utilizing credential harvesting domains and common payloads. However, over time, they have significantly advanced their capabilities, transitioning from using commercially available malware like RCS Galileo Scout to developing bespoke malware such as the Rust-based SPICA backdoor. This evolution marks a shift from simple credential theft to enabling comprehensive remote system access. The SPICA malware is deployed through a cleverly crafted phishing campaign, where emails masquerade as encrypted PDFs requiring a fake decryptor, which is actually the malware. Upon execution, SPICA establishes a WebSocket-based command and control (C2) communication channel, ensuring persistence via a scheduled task that is designed to blend seamlessly with legitimate tasks. This level of sophistication in their attack chain highlights their capability to craft believable phishing emails, which are a critical component of their strategy. SectorC Group's consistent use of phishing infrastructure over the years has been pivotal in aiding attribution efforts. Their operations have been extensively mapped to MITRE ATT&CK techniques, particularly spear phishing and masquerading, underscoring their reliance on social engineering tactics. The group's focus on creating well-crafted phishing emails over direct malware attacks emphasizes the importance of understanding attacker behavior and adapting threat intelligence strategies accordingly. This approach not only enhances their operational success but also poses significant challenges for targeted entities, necessitating robust defenses against such advanced persistent threats.
SectorM Group has demonstrated a sophisticated and evolving approach to cyber-attacks, characterized by their use of advanced techniques and a diverse malware arsenal. Their operations, as observed in the recent incidents, involve the deployment of a Rust-based loader that is adept at bypassing security measures through encryption and obfuscation. This loader is used to deliver the ValleyRAT backdoor, a tool that has been previously associated with various threat actors, indicating a possible reuse or adaptation of known malicious tools. The group's phishing campaigns are highly targeted, leveraging social engineering tactics by impersonating legitimate entities such as tax services to deceive recipients into downloading malicious archives. These archives are cleverly disguised, often using icons of common file types like PDFs or Excel documents, to avoid raising suspicion. SectorM Group's ability to maintain persistence is notable, employing innovative techniques such as shutdown interception to ensure their presence on compromised systems. The introduction of a Python-based backdoor, ABCDoor, as a new ValleyRAT plugin, highlights their capability to adapt and expand their toolset to enhance their operational effectiveness. The group's activities have impacted a wide range of sectors, including industrial, consulting, retail, and transportation, indicating a broad targeting strategy. Furthermore, their geographical reach is expanding, with recent attacks affecting countries beyond their initial focus, including Russia, India, and Japan. This expansion suggests a strategic intent to widen their influence and impact across different regions. Overall, SectorM Group's operations reflect a high level of technical proficiency and adaptability, utilizing a combination of social engineering, sophisticated malware, and persistence techniques to achieve their objectives.
The SectorJ Group has demonstrated a sophisticated approach to cyber attacks, particularly through their recent campaign targeting the PyPI repository. Their tactics, techniques, and procedures (TTPs) reveal a high level of technical acumen and strategic planning. The group successfully infiltrated the PyTorch Lightning deep-learning framework by embedding a credential-stealing worm within compromised versions 2.6.2 and 2.6.3. This attack was notable for its unique vector, as the payloads were activated during library imports rather than installations, circumventing traditional security measures like sandboxed installations. The two-stage payload initiated a Bun JavaScript runtime and deployed an obfuscated JavaScript worm, a method reminiscent of previous npm compromises, indicating a pattern in their operational methods. The malware was designed to execute in silent modes to avoid detection, and it employed geofencing techniques to bypass Russian locales, showcasing their ability to tailor attacks based on geographic considerations. The payload was adept at credential theft, capturing tokens and environment variables, and conducting AWS account fingerprinting. Furthermore, it established persistence by altering up to 50 branches per GitHub repository, ensuring a long-term presence within compromised environments. The campaign's impact was amplified by the republishing of npm packages with the embedded worm, facilitating cross-platform compromises and demonstrating the group's capability to affect a wide ecosystem. Overall, SectorJ Group's activities highlight their proficiency in leveraging advanced malware techniques and their strategic use of supply chain attacks to maximize disruption and data exfiltration.
Key Characteristics of This Week's Cyber Threats
This week, a series of sophisticated cyber threat campaigns have been identified, showcasing a range of technical and tactical characteristics that highlight the evolving landscape of cyber threats. These campaigns have targeted various sectors, including software developers, cryptocurrency companies, government entities, and more, employing a variety of malware, attack vectors, and infection pathways. One notable campaign weaponized NPM packages to target developers through manipulated packages such as "es6-runtimejs," "winston-js-express," and "ether-bn.js." These packages initiated an infection chain that led to the deployment of malware called "PylangGhost," which is heavily encrypted and large in size. The attack used cloud infrastructure, particularly Cloudflare Pages, to host the initial payload, demonstrating the group's capability to abuse cloud services for malicious purposes. Another significant campaign targeted the PyPI repository, compromising versions 2.6.2 and 2.6.3 of the PyTorch Lightning framework. The attack vector involved a credential-stealing worm activated during library imports, bypassing traditional sandboxed installations. This campaign mirrored previous NPM compromises, emphasizing the cross-platform nature of modern supply chain attacks. In the realm of phishing, a campaign targeting a North American Web3/cryptocurrency company utilized spear-phishing emails with manipulated Calendly invites, leading victims to a typo-squatted Zoom URL. This sophisticated social engineering attack captured camera feeds and executed clipboard injection attacks, highlighting the threat actors' focus on high-value targets within the cryptocurrency sector. The exploitation of a critical authentication bypass vulnerability, CVE-2026–41940, in cPanel/WHM servers was another key incident. Attackers utilized session manipulation tactics to gain unauthorized access, deploying webshells and a PAM-based credential harvester to maintain persistence. This attack demonstrated advanced techniques in server manipulation and highlighted the importance of timely patching. Additionally, a campaign involving the "ClickFix" malware targeted both macOS and Windows systems through compromised websites. This campaign employed the "PHANTOMPULSE" malware and utilized Cloudflare for infrastructure, indicating a well-organized operation with significant automation. The use of AI platforms for malicious purposes was also observed, with attackers exploiting Hugging Face and ClawHub to distribute trojans, cryptominers, and the AMOS Stealer. This shift towards AI distribution channels underscores the potential large-scale impact due to the widespread adoption of AI platforms. A cyber threat campaign targeting developers through fake job interview processes was identified, leveraging platforms like GitHub and LinkedIn to distribute repositories with embedded payloads. These payloads were designed to steal credentials and session tokens, enabling rapid access to enterprise systems. The campaign abused VS Code task automation, highlighting the attackers' focus on the developer ecosystem and software supply chain. In the realm of ransomware, the VECT 2.0 ransomware was identified, behaving more like a data wiper due to a critical flaw in its encryption. This flaw resulted in irreversible file destruction, marking a significant risk to affected systems. Overall, these campaigns demonstrate a range of technical and tactical characteristics, including the use of sophisticated malware, advanced social engineering techniques, exploitation of vulnerabilities, and abuse of trusted platforms. The evolving nature of these threats highlights the need for continuous vigilance and adaptation in cybersecurity practices.
Key Takeaways from This Week's Cyber Threat Landscape
This week, the cybersecurity landscape has been marked by a series of sophisticated cyber threats that underscore the evolving tactics and techniques employed by threat actors. The implications of these attacks are profound, highlighting vulnerabilities in software supply chains, the exploitation of trusted platforms, and the persistent targeting of high-value sectors such as cryptocurrency, AI, and cloud services. Organizations must recognize that the threat landscape is not static; it is characterized by dynamic and adaptive adversaries who leverage advanced techniques such as supply chain attacks, phishing-as-a-service platforms, and the exploitation of cloud infrastructure. The weaponization of npm packages demonstrates the potential for widespread compromise within developer environments. By targeting seemingly legitimate packages, attackers can initiate infection chains that lead to the deployment of sophisticated malware such as "PylangGhost." This underscores the need for organizations to implement robust supply chain security measures, including the verification of third-party code and the use of tools that can detect anomalous behavior in software dependencies.
The exploitation of vulnerabilities such as CVE-2026–41940 in cPanel/WHM servers further highlights the importance of timely patch management and the need for organizations to maintain a proactive security posture. The ability of threat actors to exploit authentication bypass vulnerabilities to gain unauthorized access and establish persistent footholds within networks demonstrates the critical need for comprehensive vulnerability management programs that prioritize the remediation of known security flaws. The use of phishing campaigns, such as those targeting cryptocurrency and Web3 companies, reveals the ongoing threat posed by social engineering tactics. These campaigns often employ sophisticated techniques, including the use of AI-generated assets and typo-squatted domains, to deceive victims and extract sensitive information. Organizations must invest in security awareness training for employees to recognize and respond to phishing attempts effectively. Additionally, implementing multi-factor authentication and monitoring for anomalous access patterns can help mitigate the risk of credential theft and unauthorized access. The targeting of AI platforms like Hugging Face and ClawHub for malware distribution highlights the growing threat to AI ecosystems. As AI becomes increasingly integrated into business operations, the potential for exploitation by threat actors rises. Organizations must ensure that AI platforms are subject to the same rigorous security assessments as other critical systems, with a focus on detecting and mitigating the risks associated with malicious code execution and data exfiltration. The analysis of the "Phoenix System" phishing-as-a-service platform reveals the industrialization of phishing campaigns, with threat actors leveraging automated tools to manage large-scale operations. This highlights the need for organizations to adopt advanced threat detection and response capabilities that can identify and neutralize phishing threats in real-time. The use of geofencing and real-time victim monitoring by threat actors underscores the importance of implementing security measures that can adapt to evolving threat tactics. In conclusion, the security implications of this week's cyber threats are significant, with organizations facing a complex and rapidly evolving threat landscape. To effectively respond to these challenges, enterprises must adopt a strategic approach to cybersecurity that encompasses robust supply chain security, proactive vulnerability management, comprehensive security awareness training, and advanced threat detection and response capabilities. By doing so, organizations can enhance their resilience against sophisticated cyber threats and protect their critical assets from compromise.