But in modern cybersecurity, this strategy is dead. Attacks are now occurring from within the network.
So do not trust even if it is inside! (Zero Trust)
1. What is Zero Trust (NIST SP 800–207)?
Zero trust is a holistic approach to network security. It means that nothing is inherently trusted.
Even if you are the CEO of the organization and you are on the office Wi-Fi, the system will see you as a threat until proven otherwise.
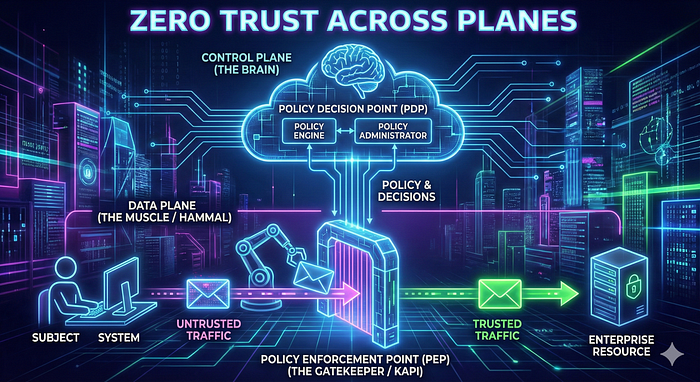
2. The Brain and The Muscle (Control Plane and Data Plane)
To implement zero trust, we split the network into two functional planes of operation.
- The Control Plane (The Brain): This is the thinking point. It manages the actions and defines the policies. It is the boss.
- The Data Plane (The Muscle): This is the "Porter". It processes the network data, encrypting, etc. It doesn't decide; it just moves the data based on what the Control Plane says.
3. Adaptive Identity
This is my favorite part of Zero Trust architecture. For a long time, security was binary: "Is your password correct? Yes? Okay, come in." Zero Trust uses Adaptive Identity. User behavior is also important in zero trust (Remember, a seemingly innocent chemistry teacher could be a drug dealer, so be aware of Walter Whites). Adaptive identity analyzes the risk level in real-time.
Imagine a gatekeeper. You show your ID.
- Old Security: "Your ID is valid. Enter."
- Zero Trust: "Your ID is valid… BUT why are you wearing a mask? Why are you trying to enter at 4 AM? And why are you sweating so much?"
This is exactly what Adaptive Identity does. It considers multiple risk indicators like your location, time, etc. It says: "Your password is correct, but I don't like your behavior. Prove yourself to me."
4. Security Zones
In zero trust, using the zones can be enough to deny access. But we do not use zones to trust and give access!
There are implicitly untrusted zones in zero trust, but we don't have implicitly trusted zones.
You can say "Deny any access from Russia," but you can't say "Accept all accesses from Russia."
Just because you are in a "safe" zone doesn't mean you are safe.
5. Architecture
So, what is the architecture behind this? What are the components?
1. Policy Enforcement Point (PEP): This is the Gatekeeper for us. It sits directly in front of the resource (like a server or file).
2. Policy Decision Point (PDP): This is the ultimate decision-maker. It evaluates the rules and decides to "Grant, Deny, or Revoke" access.
The PDP is actually split into two logical parts:
- Policy Engine: The "Judge." It looks at the rules and risk factors to make the decision.
- Policy Administrator: The "Executioner." If the Engine says yes, the Administrator communicates with the PEP and generates the necessary access tokens or credentials.
3. The flow (Step-by-Step):
- The user wants to access a Resource.
- They hit the PEP (Gatekeeper).
- The PEP asks the Policy Decision Point (PDP): "Can this guy come in?"
- If approved, the Policy Administrator instructs the PEP to open the gate (often by issuing a session token).
- The gate opens, and the user connects to the resource.
Conclusion: What Happens If We Don't Use Zero Trust?
You might ask, "What difficulties will we face if we ignore Zero Trust?" The answer is simple but scary: Lateral Movement.
Without Zero Trust, if an attacker (or ransomware) compromises a single laptop in your trusted network, they can move freely to your critical servers because there are no internal checkpoints. It's like a thief entering a hotel lobby and suddenly having keys to every single room. Zero Trust ensures that even if one room is breached, the rest of the building remains locked and secure.


