Day 19 of breaking web applications on purpose.
Let's imagine something weird.
You log into your account.
Everything looks normal.
But then you notice something strange.
Your profile bio has changed.
Different text. Different information.
You didn't edit it.
So who did?
Today I discovered how that could happen.
🎯 The Setup
The application allows users to edit their profile information.
Name Bio Personal details
Standard account settings.
You update your info → click save → the server updates your profile.
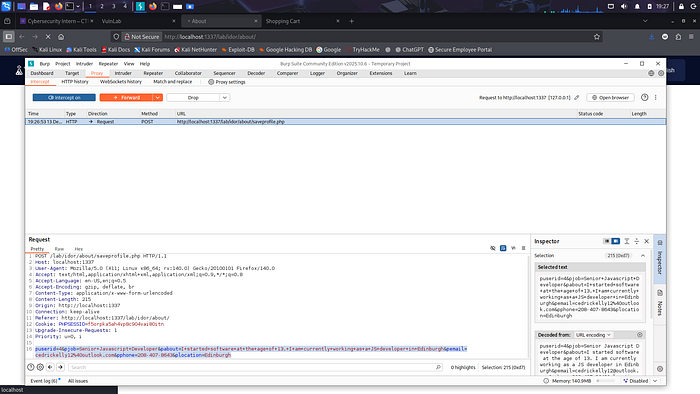
But before the request reached the server, I intercepted it.
Inside the request was this:
user_id=3
That parameter tells the server which user profile should be updated.
Now here's the real question.
What if we change it?
🧠 The Experiment
Instead of updating my own profile…
I modified the request.
From:
user_id=3
To:
user_id=4
Another user's account.
Then I sent the request.
No admin access. No special privileges. Just a normal user.
Click.
Send.
💣 The Result
Update successful.
The server accepted the request.
But the profile that got updated…
Was not mine.
It belonged to another user.
No permission check. No ownership validation. No security barrier.
Just one number changed.
⚡ Why This Happens
The application trusted client input.
It assumed:
"If the request says user_id = X, then the logged-in user must own that profile."
But the client is fully under user control.
Requests can be intercepted. Parameters can be edited. Identifiers can be changed.
And when servers trust those identifiers…
IDOR vulnerabilities appear.
🧠 Think About This
Imagine a social media platform where anyone could edit your bio.
Change your name.
Modify your personal details.
All without your knowledge.
That's the kind of damage a simple authorization mistake can cause.
🔥 Why This Matters
An attacker could:
• Deface user profiles • Spread malicious links • Impersonate users • Manipulate public information • Perform social engineering attacks
And again…
This wasn't a complicated hack.
It was editing one parameter.
🛡️ The Fix
Servers must enforce ownership checks.
Instead of trusting client IDs:
• Derive user identity from the session • Ignore client-supplied user_id values • Validate ownership before modifying data • Implement strict authorization checks
Security rule:
If the client chooses the user ID, the attacker chooses the victim.
🎯 Day 19 Takeaway
Today's exploit didn't require SQL injection.
It didn't require admin access.
It didn't require malware.
Just one modified request.
One number changed.
And suddenly…
I could edit someone else's profile.
Tomorrow?
We test what happens when attackers start manipulating shopping carts.
LESS GOOO 🔥
When the server trusts your user ID someone else's profile becomes editable.