I fired it off through one of the big platforms and immediately felt that familiar itch: "Is some LLM somewhere slurping this up right now? Is my email provider quietly reading the thread? Did I just hand my findings to a company that might sell the data later?"
I'm not paranoid. I'm just a security researcher who's seen enough leaks and shady terms of service.
That was the final straw.
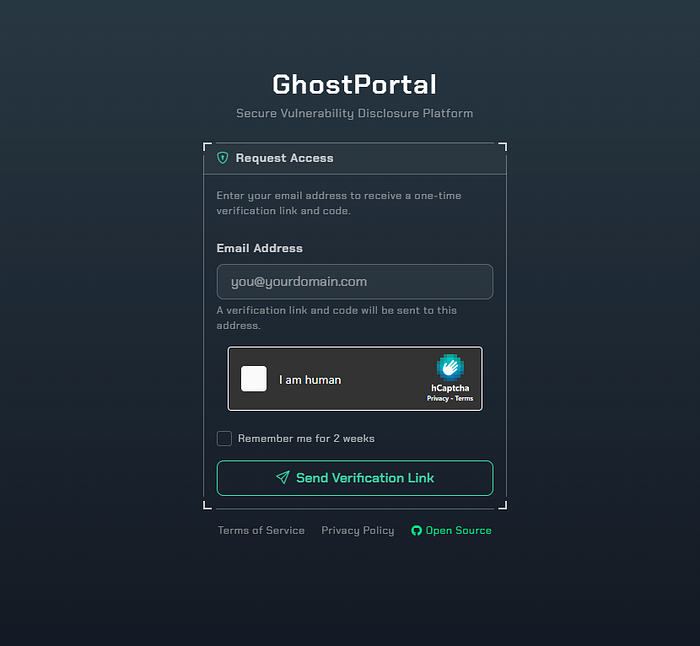
So instead of complaining on Twitter like usual, I sat down and built GhostPortal — a fully self-hosted vulnerability disclosure platform that puts the researcher (and the program) back in the driver's seat.
Why most platforms suck for privacy
Big bug bounty platforms are convenient, sure. But they come with baggage:
- Your reports get fed into their AI models (or at least the terms allow it).
- Email threads live on Gmail/Outlook — good luck if you care about scanning.
- Sequential report IDs make enumeration trivial.
- Passwords. Everywhere. Ready for credential stuffing.
- You have zero control over where your data actually lives.
I wanted none of that.
What GhostPortal actually is
GhostPortal is a self-hosted platform for submitting, tracking, and managing vulnerability reports — built from the ground up with paranoia in mind.
You run it on your own server (Docker makes it stupidly easy). Everything stays on your hardware unless you decide otherwise.
Key things that actually matter:
- Completely passwordless auth. Magic link + a 20-character OTP with ridiculous entropy. No passwords stored. Not even hashed. Gone.
- UUIDs everywhere. No sequential IDs you can guess. Good luck enumerating reports.
- Local AI only. Want help drafting or summarizing the report? Point it at your own Ollama instance. Nothing leaves your box. (Cloud APIs are optional and off by default.)
- Real retest workflow. Fix deployed? Team requests retest. You confirm fixed / partial / not fixed. Bonus bounty tracked separately if they feel generous.
- Bounty tracking that doesn't suck — PayPal Payouts integration plus manual crypto and bank options.
- Immutable audit logs so nobody can pretend they didn't see something.
- Encrypted backups (AES-256-GCM). Because losing your report history would be embarrassing.
The UI is dark, tactical, HUD style — because if I'm going to stare at this thing for hours, it might as well look cool.
Who is this actually for?
- Independent researchers who run their own mini-programs or just want a clean private submission portal.
- Small teams or companies that don't want to pay HackerOne/Bugcrowd fees and don't trust SaaS with their vuln data.
- Anyone who's ever thought "I wish I could just host this myself and not worry about their terms changing next quarter."
It's licensed AGPL-3.0, so you can use it, modify it, and host it — but you can't turn it into a closed-source SaaS and sell access. Fair is fair. Not every hero wear capes :))
Quick start (yes, it's actually quick)
Bash
git clone https://github.com/0xspade/ghostportal
cd ghostportal
cp docker/.env.docker.example .env
# edit the obvious stuff (secret key, owner email, passwords)
docker compose up -dThen run the migrations and seed script. Boom — you're live. First login hits your OWNER_EMAIL with a magic link.
Full docs are in the repo if you want to go deeper (production hardening, custom payment flows, etc.).
The privacy part I actually care about
- No cloud AI ever sees your report unless you explicitly enable it.
- Emails are only for notifications — nothing gets scanned or profiled by Google/Microsoft.
- All sensitive config stays in env vars, never leaked in responses.
- Open redirect protection so attackers can't abuse your domain for phishing.
If that sounds like basic hygiene to you… welcome to the club. Most platforms don't even do this.
What's next?
The repo is live: https://github.com/0xspade/ghostportal
It's still early — alpha stage, rough edges exist. But the core (auth, report flow, retests, bounties) already works.
If you're a researcher tired of the same old platforms, star it, try it locally, and tell me what sucks. PRs are very welcome, especially for UI polish, new payment methods, or report templates.
I built this because I was annoyed. Maybe you're annoyed too.
Drop a comment if you want to self-host your own vuln portal or if you have ideas on what a privacy-first disclosure tool should actually do in 2026.
Let's stop feeding our bugs to other people's models.
**flies away mofos ;)**