After hanging out with a bunch of professionals discussing GRC leadership, I have witnessed the maturation of cybersecurity from an IT afterthought to a board-level strategic imperative. The release of NIST CSF 2.0 represents the single most consequential shift in how organizations architect their cybersecurity governance in the past decade. This journal synthesizes my strategic perspective on what CSF 2.0 means for enterprises, how it restructures the relationship between executives, managers, and practitioners, and what GRC leaders must do to operationalize it effectively.
Part 1 focuses on what I consider the flagship transformation: the elevation of Governance from a buried subconcept to the strategic center of the entire framework.
Why CSF 2.0 Matters Now
NIST released CSF 2.0 on February 26, 2024, the first major revision in a decade. CSF 2.0 expanded its applicability to all organizations regardless of size, sector, or cybersecurity maturity. The title itself was changed. It was no longer called "Framework for Improving Critical Infrastructure Cybersecurity" but simply "The NIST Cybersecurity Framework (CSF) 2.0." This framework was intentionally written with international harmonization in mind, aligning with global standards to encourage worldwide adoption.
The Regulatory Catalyst
The threat landscape and regulatory environment shifted dramatically between CSF 1.1 and CSF 2.0. The SEC finalized its cybersecurity disclosure rules requiring public companies to report material cybersecurity incidents within four business days via Form 8-K and disclose risk management processes, board oversight, and governance structures in annual 10-K reports. The EU's NIS2 Directive imposed mandatory cybersecurity requirements with enforcement penalties on essential and important entities across member states. These regulatory mandates demanded a framework that placed governance at its core, not as an afterthought.
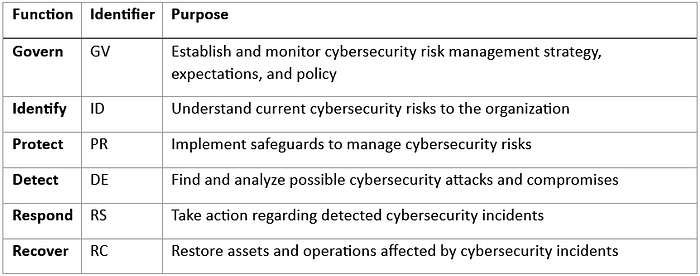
CSF 2.0 organizes its core around 6 Functions, 22 Categories, and 106 Subcategories — a refinement from CSF 1.1's 5 Functions, 23 Categories, and 108 Subcategories. This structural change may appear modest numerically, but the reorganization is architecturally significant. Categories and subcategories were reorganized and consolidated to streamline the framework and enhance clarity. The six core functions are:
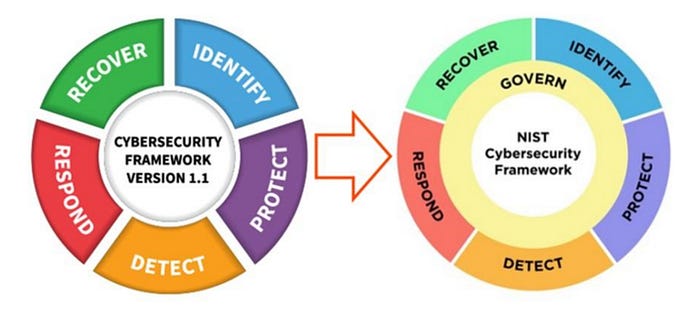
NIST visually represents these functions as a wheel, with Govern at the center that informs how all five other functions are implemented. This is a critical design choice. It communicates that governance is not a phase but a continuous operational posture.
The GOVERN Function
The Flagship change. Previously, governance activities were embedded within the Identify function, limiting visibility into how governance supports all aspects of a cybersecurity program. Now, it promotes clearer alignment between cybersecurity efforts, enterprise risk management, and legal obligations. It also brings CSF 2.0 in line with other NIST frameworks, like the AI Framework and Privacy Framework, which include similar governance-focused functions. The Govern function contains six categories and 31 subcategories.
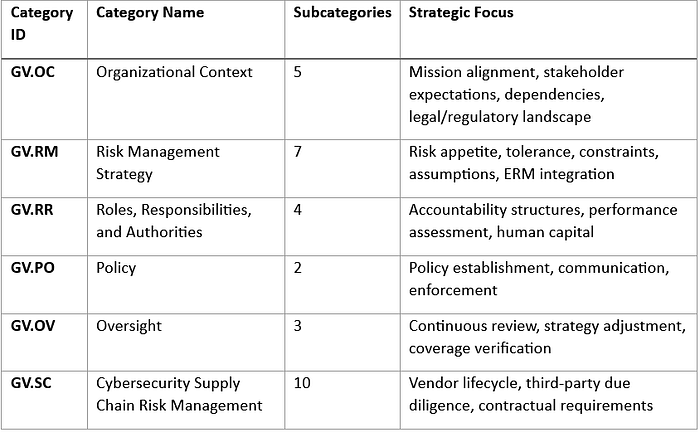
GV.OC—Organizational Context
This category requires organizations to define the circumstances surrounding their cybersecurity risk management decisions, like missions, stakeholder expectations, dependencies, and legal, regulatory, and contractual requirements. This is not asset identification (which resides under ID.AM in the Identify function). It is about contextualizing the organization's operating environment to make governance decisions more effective.
From my perspective, this means the GRC team must collaborate with business strategy, legal, compliance, and enterprise architecture to document:
- The organization's mission-critical services and their interdependencies
- All regulatory, contractual, and industry-specific requirements (HIPAA, PCI DSS, GDPR, NIS2, SOX, state privacy laws)
- Stakeholder expectations—from the board, customers, regulators, and business partners
- External dependencies that create risk exposure (cloud providers, SaaS platforms, managed service providers)
GV.RM—Risk Management Strategy
This is the most operationally consequential category in the entire framework. GV.RM establishes that the organization's priorities, constraints, risk tolerance, appetite statements, and assumptions are communicated and used to support operational risk decisions.
- GV.RM-02 specifically requires organizations to define and communicate risk appetite and translate it into specific, measurable risk tolerance statements. Risk appetite is a strategic, qualitative declaration, while Risk tolerance is the quantitative threshold at which action is triggered.
- GV.RM-03 mandates that cybersecurity risk management activities be integrated into enterprise risk management processes. NIST recently updated its entire IR 8286 publication series (all five documents) to align more closely with CSF 2.0, putting greater emphasis on governance to ensure cybersecurity capabilities support the broader mission through ERM. This integration is no longer optional; it is essential for organizations seeking to implement continuous risk management at scale.
GV.R—Roles, Responsibilities, and Authorities
This category ensures that cybersecurity roles, responsibilities, and authorities are established and communicated to foster accountability, performance assessment, and continuous improvement. The subsection outlines the manual play in cybersecurity and discourages reliance solely on technology investments to solve cybersecurity challenges.
For GRC people, this means formally defining:
- Board-level cybersecurity oversight responsibilities
- Executive-level risk ownership (CEO, CFO, CIO, CISO, General Counsel)
- Business unit risk ownership and escalation paths
- Technical team authorities for real-time risk decisions
- Internal audit's role in independent cybersecurity assurance
GV.PO—Policy
Covers the establishment, communication, and enforcement of cybersecurity policies. While only two subcategories exist here, the policy function is a linchpin. Policies translate risk appetite into actionable rules, standards, and procedures that flow down to every operational function.
GV.OV—Oversight
This category emphasizes continuous review and revision of risk management activities to inform and adjust strategy. It requires organizations to maintain not just static policies but dynamic governance loops that reflect evolving business objectives, threat landscapes, and regulatory requirements. Boards and executives must take active responsibility for oversight, including setting clear risk tolerance levels, approving security policies, and ensuring accountability across departments.
GV.SC—Cybersecurity Supply Chain Risk Management
With 10 subcategories (GV.SC-01 through GV.SC-10), this is the most detailed category in the Govern function. The primary objective is to extend appropriate first-party cybersecurity risk management considerations to third parties, supply chains, and products and services an organization acquires, based on supplier criticality and risk assessment.
The Govern function's placement of supply chain risk management under governance is architecturally significant. It signals that C-SCRM is a strategic governance decision, not merely a technical control. This maps directly to NIS2's Article 21 requirements on cyberrisk governance and supply chain due diligence.
The 10 C-SCRM subcategories require organizations to:
- Establish formal C-SCRM programs agreed to by organizational stakeholders
- Define clear roles and communication channels for managing suppliers
- Integrate supply chain risk into enterprise risk management processes
- Identify and prioritize suppliers by criticality
- Address cybersecurity requirements in all contracts and agreements
- Conduct due diligence before entering partnerships
- Continuously assess and monitor third-party risks
- Include third parties in incident planning and response
- Include supply chain risks in improvement activities
- Manage risks even after vendor relationships conclude
In Part 2, we continue to explore the Three-Tier Cybersecurity Hierarchy, explaining how it operates. It is followed up by Board-Level Reporting Under CSF 2.0, an overview of Microsoft's Integration Playbook, Regulatory Alignment, and Strategic Implementation Recommendations.
Subscribe to my newsletter to receive all the parts of this NIST 2.0 Journal. Each part ends with a preview of the next, creating a natural series flow in the technical document. Just to have an approximate idea, this journal may have 5–6 parts in total with deep dive analysis and findings. You can also visit my LinkedIn profile to explore more.