Day 9 of breaking web applications on purpose.
Let me ask you something:
What's the most powerful character in hacking?
Not <script>. Not ;.
Just this:
'
One single quote.
That's all it takes to start breaking databases.
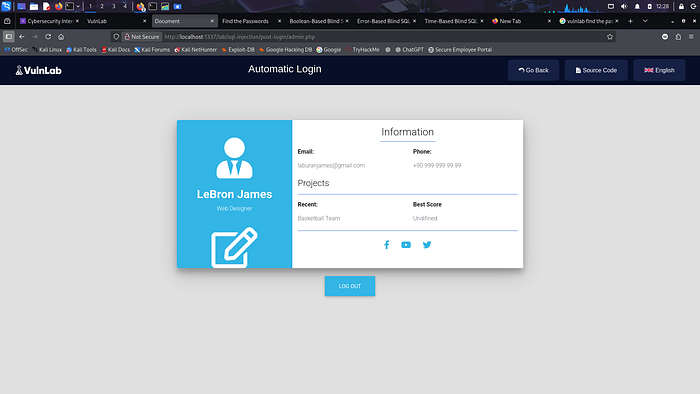
Welcome to Basic SQL Injection: Login Error Discovery.
🎯 The Setup
The application has a login form:
- Username
- Password
Simple. Classic. Everywhere.
Behind the scenes, the backend builds a query like this:
SELECT username, password FROM users WHERE username = 'INPUT' AND password = 'INPUT'
Looks normal.
But there's one fatal mistake.
User input is directly inserted into the query.
No parameterization. No prepared statements.
Just raw concatenation.
🧠 The First Test (Always Do This)
When testing login forms, ask yourself:
👉 What happens if I break the syntax?
So instead of a username, enter:
'
Password? Anything.
Submit.
💣 The Result
The application throws a database error.
Something like:
You have an error in your SQL syntax…
Pause.
That error tells you something powerful:
- The input is reaching the SQL query.
- It's not sanitized.
- The database engine is interpreting it.
- You have injection potential.
You didn't bypass login yet.
But you confirmed the vulnerability.
And confirmation is everything.
⚡ Why This Works
Because the backend is likely doing something like:
$sql = "SELECT username,password FROM users WHERE username='" . $usr . "' AND password='" . $pwd . "'";
So when you input:
'
The final query becomes:
WHERE username='''
That breaks SQL syntax.
The database crashes.
And reveals itself.
That's step one in SQLi methodology:
Break → Observe → Confirm → Exploit
🧠 Real-World Analogy
Imagine a receptionist writing your name on a guest list.
Instead of writing:
"John"
You say:
"John' DROP TABLE users; — "
She doesn't filter it.
She writes it exactly.
Now the guest list is corrupted.
That's SQL injection.
The system trusts your input as part of its instructions.
💥 Why Even an Error Is Dangerous
Many people think:
"It's just an error message."
No.
It reveals:
- Database type (MariaDB / MySQL)
- Query structure
- Backend logic
- Injection point confirmation
And once confirmed…
Attackers escalate.
🔥 The Bigger Question
When you test login forms, do you:
- Only try default passwords?
- Or test syntax-breaking payloads?
- Or test boolean conditions?
- Or test UNION injection?
- Or test blind techniques?
SQL Injection isn't about guessing passwords.
It's about manipulating logic.
🛡️ Proper Fix
Never build queries like this:
"… WHERE username='" . $usr . "'"
Instead use prepared statements:
$stmt = $pdo->prepare("SELECT username,password FROM users WHERE username=? AND password=?"); $stmt->execute([$usr, $pwd]);
Also:
- Disable detailed SQL error messages in production.
- Apply least-privilege database permissions.
- Validate input server-side.
Security rule:
Never trust input inside SQL queries.
Ever.
🎯 Day 9 Takeaway
You didn't bypass authentication.
You didn't extract data.
You just entered a single quote.
And the database responded.
That's how SQL Injection starts.
Small input.
Big impact.
Tomorrow?
We move from breaking syntax to extracting actual data from the database.
And that's where things get serious!
LESSGOOO 🔥