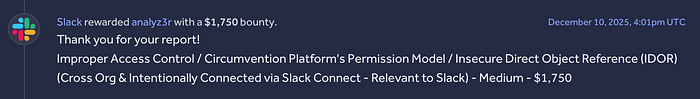
Hi Everyone. My name is Sirat, I'm 25 years old, from Kurdistan. I do bug bounty hunting on the HackerOne platform, and today I want to share something that made my day, finding an interesting vulnerability in Slack that earned me a $1,750 bounty.
My Experience With Slack
I have pretty solid experience with Slack, so I don't chase classic OWASP vulnerabilities, I focus on logical findings, and I'm good at them because I understand how the platform works and what causes vulnerability on this platform.
This particular finding required no exploitation at all, just a simple scenario from my mind, that could even cause other companies as well who use Slack to be hacked. It's one of the easiest bugs I've ever found, yet it paid more than many of my previous bounties.
Explaining "Approved Email Domains"
In Slack, there's a feature called "Allow people with approved email domains to join this workspace", it lets workspaces be shared with a specific email domain (like "medium.com"), so anyone on Slack using that domain's email can join the workspace.
Any vulnerability in this feature could be critical, since it controls who is authorized to join a workspace, and that's exactly what I found, by abusing this feature, I was able to join workspaces I was never supposed to have access to.
So What Was The Vulnerability?
When this feature "Allow people with approved email domains to join this workspace" is enabled without the admin's knowledge, anyone with access to the approved domain's email inbox could join that workspace unintentionally.
I noticed that when accepting a Slack Connect channel invite as a victim, either with no previous workspace or by joining with a new one, the "Allow people with approved email domains to join this workspace" feature was being automatically enabled without any prompt or consent, as the victim, I had no idea it was even turned on.
Steps to reproduce:
- As User A, invite User B to your Slack Connect channel.
- As User B, accept the invite by creating a new workspace.
After this, simply visiting https://<userBworkspace>.slack.com/signup reveals that the feature is now enabled on User B's workspace, allowing anyone sharing the same email domain as User B to join their workspace without their knowledge.
What Was The Impact?
At first glance, the vulnerability might seem low impact, after all the attacker would need access to the same email domain as the victim, but thinking deeper reveals a more serious picture.
Let me tell you that Slack workspace subdomains are created in order, not randomly — for example, medium-1, medium-2, medium-3, etc… Making it easy for an attacker to enumerate and discover all workspaces created by a target company.
The real threat here is the insider attacker. A low-privileged employee, sharing the same company email domain, could join workspaces unintentionally created by their CEO or other executives, gaining full access to private Slack Connect channels they were never meant to see.
So while this does require some level of insider access, the potential impact on companies targeted from within is still very serious.
At first I thought this is a misconfiguration that happens by Slack customers themself, I was actually had a plan to report it to all bug bounty programs but later I found out this is actually a Slack misconfiguration. Even though some companies might still have affected by this vulnerability, please notice that reports including this issue won't be accepted because it is Slack's vulnerability not customers, and it have already been resolved.
Hope you enjoyed the story! https://x.com/siratsami71