Modern applications rely on state transitions to control business workflows. In e-commerce and service platforms, an order typically moves through several states: created → pending payment → paid → completed Each transition represents a business decision. The system assumes that certain conditions have already been satisfied before moving to the next state. But when state transitions happen before those conditions are verified, a Business Logic Vulnerability can emerge. This article explains how incorrect timing in state management can lead to real financial impact.
— - ## The Intended Business Rule
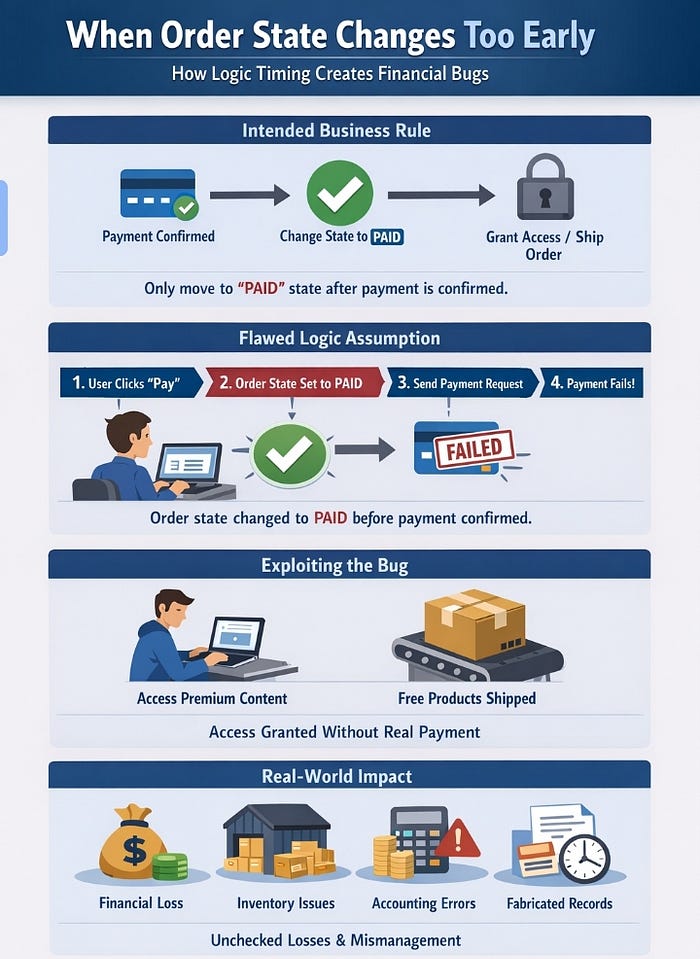
In a secure purchase flow, an order should only move to the **paid** state after payment confirmation is successfully received. This rule ensures: * Payment has actually been completed. * Users receive access only after payment succeeds. * Inventory and accounting remain consistent. The order state itself becomes a logical security boundary. — - ## The Developer Assumption
In many implementations, developers assume that: * Payment requests usually succeed. * Payment confirmation arrives immediately. * Users cannot interact with intermediate states. Because of this assumption, some systems update the order state immediately after the user initiates payment instead of waiting for confirmation from the payment provider. A simplified flow may look like this: 1. User clicks "Pay". 2. Order state changes to `paid`. 3. Payment request is sent to the payment gateway. 4. Confirmation arrives later. This creates a time window where the system believes payment has already succeeded. — - ## The Logic Flaw
If the payment fails, is cancelled, or interrupted, the order may remain marked as `paid`. At this point: * The system trusts an invalid state. * Business rules depending on the paid status are executed. * Access or services may be granted without real payment. The vulnerability exists not because of broken code, but because the system trusted process timing instead of enforcing business verification. — - ## Example Scenario
Consider the following simplified logic: POST /pay → update order state = paid → process payment If the payment request fails due to network interruption or gateway rejection, the state change may persist. From the system's perspective, the order is valid even though payment never completed. This mismatch between payment reality and system state creates an exploitable condition. — - ## Real-World Impact
When order states change prematurely, the consequences extend beyond incorrect application behavior. Depending on the platform logic, attackers may be able to: * Access digital products or premium services without paying. * Trigger shipment or service activation for unpaid orders. * Abuse refund mechanisms for transactions that never succeeded. * Reserve or consume inventory without financial cost. At scale, this can lead to: * Direct financial loss. * Inventory inconsistencies. * Accounting mismatches between internal systems and payment providers. * Long-term integrity issues in transaction records. Because the system internally considers the order valid, these issues may remain undetected for extended periods. — - ## Why Automated Tools Often Miss This
Automated security tools typically focus on technical patterns such as injection flaws or input validation issues. State timing vulnerabilities require understanding: * Business workflow sequencing. * Logical dependencies between actions. * Assumptions made during system design. As a result, these vulnerabilities are often discovered only through manual logic analysis. — - ## Secure Design Recommendation
To prevent this class of vulnerability: 1. Update order state only after verified payment confirmation. 2. Treat payment provider responses as the source of truth. 3. Introduce intermediate states such as `payment_pending`. 4. Validate state transitions strictly on the server side. State transitions should follow verified events, not assumptions. — - ## Final Thought
Business logic vulnerabilities rarely originate from complex technical flaws. They appear when systems assume that events will occur in the correct order. Security improves when assumptions are replaced with enforced business rules. — -