Welcome to Day 21 of our 30-Day Cybersecurity Mastery series.
Over the past week, we explored the vulnerabilities of modern applications (SQLi, XSS), the complexity of APIs, the ephemeral nature of containers, and the vastness of the public cloud.
Historically, security was a "gate" at the very end of the software development lifecycle. Developers would write code for six months, hand it to the security team, and the security team would inevitably find 500 critical vulnerabilities the day before launch. This caused immense friction.
Today, businesses must deploy software multiple times a day to survive. Security can no longer be a roadblock; it must be an invisible, automated engine. Today, we architect DevSecOps.
1. The Core Philosophy: "Shift Left"
Imagine a timeline of software development drawn from left to right. On the far left is the developer typing on their laptop. On the far right is the code running live in production for the customer.
- The Old Way (Right-Aligned): We only tested the code for vulnerabilities after it was fully built and pushed to the right. Fixing a flaw at this stage is incredibly expensive and time-consuming.
- The DevSecOps Way (Shift Left): We move security testing as far to the "left" of the timeline as possible. We want to catch the SQL injection (Day 15) the exact second the developer types it into their IDE (Integrated Development Environment), long before it ever reaches a server.
2. The Engine of Automation: The CI/CD Pipeline
To achieve this, architects do not rely on humans manually reviewing code. We build a CI/CD Pipeline (Continuous Integration / Continuous Deployment). This is a highly automated digital assembly line. Every time a developer clicks "commit," the code is automatically compiled, tested, and deployed.
As security architects, our job is to embed automated security scanners directly into this assembly line. If a scanner finds a critical vulnerability, the pipeline automatically "breaks" (halts), and the code is rejected back to the developer.
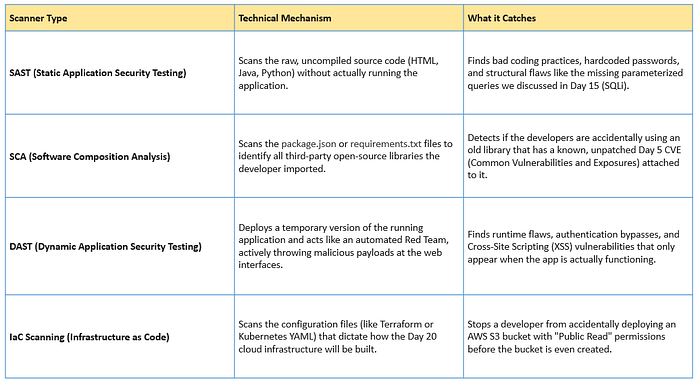
The Four Pillars of Pipeline Security
3. The Human Element: Security Champions
You can buy the most expensive SAST and DAST scanners in the world, but if the pipeline breaks 40 times a day, the developers will grow frustrated and find ways to bypass your tools.
A successful DevSecOps architecture requires cultural integration. Enter the Security Champion.
A Security Champion is not a member of the cybersecurity team; they are a senior software developer who has volunteered to receive advanced security training. They sit inside the development team, act as the local security expert, review code with a security mindset, and act as the vital bridge between the fast-paced coding world and the strict compliance world of the SOC.
The Architect's Summary
DevSecOps is the realization that in a cloud-native world, security cannot be a discrete phase; it must be an underlying fabric. By "shifting left" and injecting SAST, DAST, SCA, and IaC scanning directly into the CI/CD pipeline, an enterprise guarantees that every single line of code and every piece of infrastructure is rigorously interrogated by automated systems before it ever touches production.
