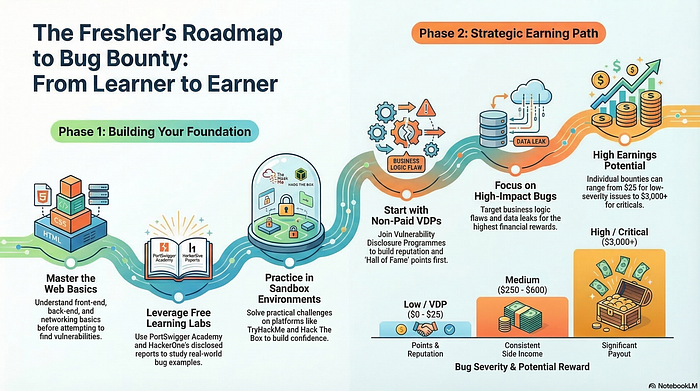
The counter-intuitive beginner's roadmap to bug bounty — from web hacking fundamentals and VDPs to your first real payout, without waiting until you feel ready
Here's a story that plays out constantly. Two people discover bug bounty on the same day. The first one spends four months building what they call a "proper foundation" — courses completed, notes organized, labs finished, methodology documented. The second one spends two weeks on a single concept, opens a beginner-friendly program the following Monday, and submits their first report by Friday.
Three months later, the second person has two accepted findings, one small payout, and a rejection that taught them more than any course module ever did. The first person is still refining their notes.
This is the bug bounty fresher's trap — and it doesn't discriminate based on intelligence, background, or technical ability. It catches the diligent ones most of all.
The myth driving this trap is almost universally believed among beginners: "I need to be fully prepared before I can contribute anything real."
The tension isn't a knowledge gap. It's a validation gap. The real issue isn't that freshers lack skills — it's that they've never had their partial skills tested against a real target, so they don't know what they actually know. No course can give you that. Only hunting can.
The Myth of the Complete Skillset
Ask any beginner what's stopping them from opening a live program today, and the answer follows a predictable pattern. They haven't finished the web application hacking module. They don't fully understand one particular vulnerability class yet. They feel like they're missing something foundational and can't quite name what it is.
This feeling is real. The conclusion drawn from it is wrong.
The belief that a complete skillset is a prerequisite for bug bounty participation assumes that finding valid bugs requires mastery across the full spectrum of web security. It doesn't. It requires sufficient depth in a narrow area, applied consistently against the right targets.
A fresher who understands how web applications handle authentication flows — what happens when session tokens are predictable, when password reset links don't expire, when account enumeration is possible through different error messages — has enough to start. Not enough to find everything. Enough to find something.
Consider a realistic example. A fresher studying web security for the first time focuses exclusively on how applications manage account recovery. They learn the common patterns, the frequent mistakes, the subtle differences between a secure and insecure implementation. They open a Vulnerability Disclosure Program with a broad scope and spend a weekend testing only account recovery flows across different subdomains. On a lesser-tested subdomain, they find a password reset link that remains valid after it has already been used. They report it clearly. It gets acknowledged.
That finding didn't require mastery of SQL injection, server-side vulnerabilities, or advanced exploitation chains. It required depth in one area and the decision to actually go look!
Intellectual insight: A complete skillset is a myth that moves with you. The horizon of "ready" shifts every time you learn something new. The only way to stop chasing it is to test what you already have against something real.
Why VDPs Are the Most Underused Resource for Freshers
Most beginners, when they think about getting paid for bug bounty, immediately think about programs with monetary rewards. This is understandable — the concept of earning from security research is part of what makes the field compelling.
But for a fresher whose primary goal should be building real-world experience and developing a functional research methodology, Vulnerability Disclosure Programs are a far more valuable starting point than paid bounty programs.
VDPs — programs where organizations invite security researchers to report vulnerabilities without offering monetary compensation — exist across a wide range of industries. Government agencies, nonprofits, educational institutions, and mid-sized companies run them specifically because they want security feedback but don't have formal bounty budgets.
The competitive pressure on VDPs is dramatically lower than on paid programs. Experienced hunters who depend on bug bounty income have little incentive to spend time on targets that don't pay. This means VDP targets are often significantly less picked-over, less documented, and more likely to contain the kinds of straightforward findings that are perfect for a fresher's first real submission.
More importantly, VDPs provide feedback without financial stakes. A rejected report on a VDP costs nothing except the time spent writing it — and the rejection itself, if the program provides any context, is one of the most efficient learning experiences available. It tells you exactly where your understanding of severity, impact, or reproduction quality needs to improve.
Intellectual insight: Freshers who start on VDPs are making an investment, not a compromise. The experience and methodology they build there transfers directly to paid programs — with the added advantage that they've already made their early mistakes where the cost was zero.
What a First Valid Bug Actually Looks Like
There's a romanticism around bug bounty findings that doesn't serve beginners well.
The findings that get written up extensively — the intricate exploit chains, the creative logic bypasses, the multi-step account takeovers — are genuinely impressive. They're also not representative of what first valid findings look like for most freshers.
First valid bugs are usually simple. Not simple in the sense of being easy to spot at a glance, but simple in the sense of being a single, clear, well-understood vulnerability class, found in a location where it wasn't expected to be.
An information disclosure on a forgotten API endpoint. An insecure direct object reference where changing a numeric ID in a URL reveals another user's data. A missing rate limit on a login endpoint that allows unlimited guessing attempts. A security-sensitive function accessible without verifying the user's current session status.
None of these require advanced technical knowledge. All of them require methodical observation, an understanding of what the application is supposed to do versus what it actually does, and the ability to communicate the finding in a way that makes the impact clear to someone who needs to prioritize a fix.
What separates freshers who find these bugs from those who don't isn't technical sophistication. It's the practice of actually opening programs and walking through applications with structured attention — feature by feature, endpoint by endpoint — rather than waiting until they feel equipped to find something impressive.
Intellectual insight: Your first valid bug will probably not be the one you imagined finding. It will be the one you stumbled across while looking for something else, on a target you almost didn't test, with a skill you thought wasn't quite ready yet.
Building the Habit That Produces Consistent Results
The freshers who transition from learner to earner aren't distinguished by a moment of breakthrough technical insight. They're distinguished by a habit — the consistent practice of showing up, opening programs, and spending structured time testing real targets.
This sounds unglamorous because it is. But it's also the actual mechanism behind every success story in this field.
The practical structure that works for most beginners looks something like this. Dedicate a fixed block of time — even two hours — exclusively to live target testing, not studying. During that block, pick one program, one feature area, and one vulnerability class. Test it methodically. Document what you find, even if you find nothing. Write a report, even if you don't submit it. Review it the next day with fresh eyes.
This practice builds three things simultaneously: a working methodology, a documentation habit, and the pattern recognition that only comes from repeated exposure to real applications.
Studying builds knowledge. Testing builds judgment. And in bug bounty, judgment is what gets findings paid.
The roadmap from fresher to earner isn't a curriculum. It's a commitment to treating real programs as classrooms — imperfect, unpredictable, occasionally frustrating classrooms that teach things no structured course ever could.
The freshers who get paid first aren't the most technically prepared. They're the ones who accepted early that preparation and participation aren't the same thing — and chose participation.
In 48 hours, I'll reveal a simple target-selection checklist most freshers completely skip — the five-question filter that tells you whether a program is worth your time before you spend a single hour inside it.
Found this useful? Follow for weekly breakdowns of beginner bug bounty strategy, web hacking fundamentals, and the mindset shifts that separate hunters who earn from those who only study. Share this with a fresher who's been "almost ready" for longer than they'd like to admit.
💬 Comment Magnet