Now it's time to explore something every SOC analyst, security engineer, bug bounty hunter, and penetration tester must know. If you are investigating web application alerts, there is one framework that appears everywhere: OWASP Almost every web attack alert, WAF rule, SIEM alert, penetration test report, or vulnerability scan is connected to it.
So in this article, we will deeply understand:
- What OWASP really is
- Why it matters for security investigations
- The OWASP ecosystem
- OWASP Top 10 vulnerabilities
- How attackers exploit them
- How SOC analysts detect them
- How defenders mitigate them
By the end of this blog, you will start recognizing web attacks in logs instantly.
1. What is OWASP?
OWASP stands for Open Worldwide Application Security Project. It is a non-profit global community focused on improving software and web application security.
OWASP provides:
- Security standards
- Vulnerability documentation
- Security tools
- Training resources
- Best practices for developers and security teams
Unlike many security frameworks, OWASP resources are completely open source and free. The project started in 2001 when security researcher Mark Curphey created a community focused on improving web security. Today OWASP is one of the most influential organizations in cybersecurity.
Thousands of organizations rely on it, including:
- Security teams
- Developers
- Bug bounty hunters
- Penetration testers
- SOC analysts
- Compliance auditors
2. Why OWASP Matters in Security Investigation
When a web attack alert triggers in a SOC, it usually maps to an OWASP category.
Examples:

The OWASP Top 10 acts as the blueprint for web attack detection.
Many security tools rely on it:
- WAF rules
- SIEM correlation rules
- Vulnerability scanners
- Pentesting frameworks
Security frameworks referencing OWASP include:
- MITRE
- PCI DSS
- SANS
- DISA STIG
That means: If you understand OWASP, you understand most web attacks.
3. OWASP Mission and Goals
OWASP's mission is simple:
Make software security visible so individuals and organizations can make informed decisions.
To achieve this, OWASP focuses on:
- Awareness: Educating developers and organizations about common vulnerabilities.
- Documentation: Providing open documentation for security best practices.
- Tools: Building open-source security testing tools.
- Standards: Creating security frameworks used globally.
4. The OWASP Ecosystem
OWASP is not just one document. It is an entire ecosystem of projects. Some of the most important ones include:

- OWASP Top 10: The 10 most critical web application vulnerabilities.
- OWASP ZAP: A popular web application penetration testing tool.
- OWASP WebGoat: An intentionally vulnerable web app used to learn hacking techniques.
- OWASP SAMM: A framework for secure software development lifecycle (SDLC).
- OWASP API Security Top 10: Focuses specifically on API vulnerabilities.
- OWASP Mobile Top 10: Focuses on mobile application security risks.
- OWASP Juice Shop: is an intentionally vulnerable web application created by the OWASP to help people learn, practice, and test web application security vulnerabilities in a safe environment.
Among all these projects, one document became legendary: OWASP Top 10
5. OWASP Top 10:2025 List
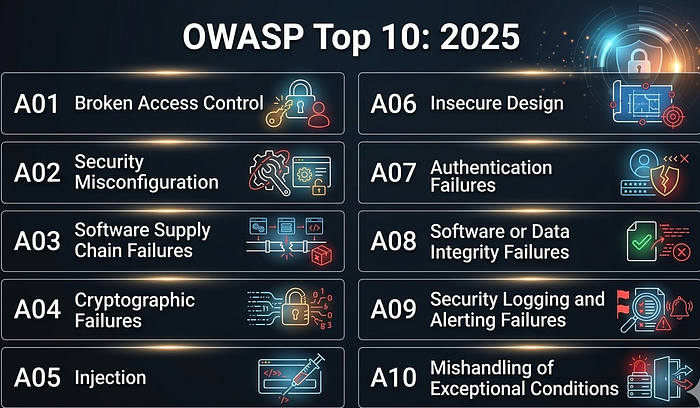
Let's explore each of these vulnerabilities in detail from a security investigation perspective.
A01: Broken Access Control
Access control ensures that users can only perform actions they are authorized to perform. When this control fails, attackers can access resources they should never see. This vulnerability remains the most critical risk in web applications.
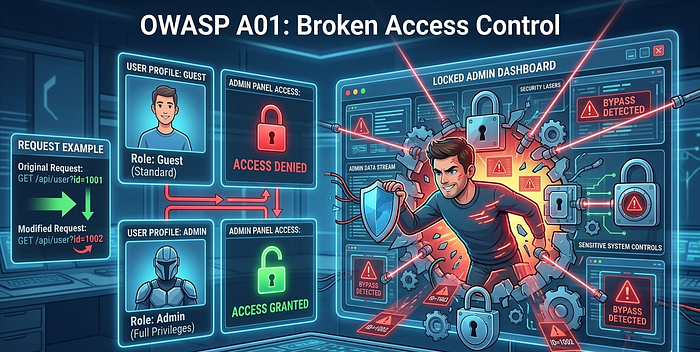
Common Attack Techniques
Attackers exploit broken access control using techniques such as:
- IDOR (Insecure Direct Object Reference)
- Privilege escalation
- Force browsing
- JWT token manipulation
- CORS misconfiguration
Example Attack
Changing a request parameter:
GET /api/user?id=1001to
GET /api/user?id=1002may allow attackers to access another user's account.
Investigation Indicators
SOC analysts should look for:
- Unauthorized API access attempts
- Requests accessing admin endpoints
- Access to other users' resources
- Parameter manipulation
Example suspicious log:
UserID=1032
Endpoint=/admin/dashboard
Role=guest
Response=200A02: Security Misconfiguration
Security misconfiguration occurs when applications, servers, or cloud environments are improperly configured, exposing systems to attackers. In 2025 this risk moved to #2 due to increasing reliance on configuration-driven infrastructure.

Common Examples
- Default credentials
- Open cloud storage buckets
- Debug mode enabled
- Directory listing enabled
- Unpatched servers
- Misconfigured CORS policies
Investigation Indicators
Attackers often scan for:
/admin
/.git
/.env
/config
/phpinfo.phpRepeated scanning for these endpoints often appears in web logs.
Example log:
GET /.env HTTP/1.1
User-Agent: masscanA03: Software Supply Chain Failures
Modern applications depend heavily on: third-party libraries, open-source packages, container images, build pipelines. If any component in this software supply chain is compromised, attackers can inject malicious code. This category expands the previous "Vulnerable Components" risk into a full ecosystem supply chain threat model.
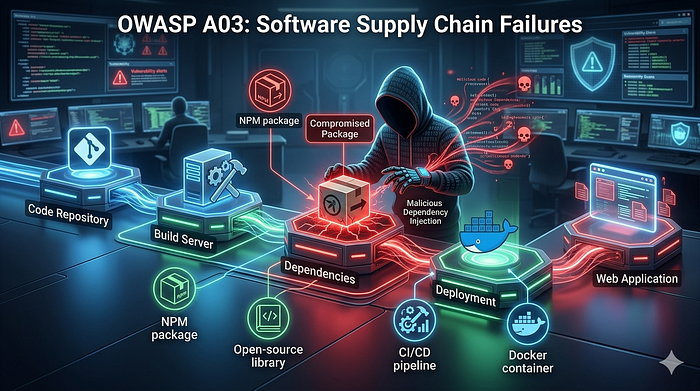
Real-World Examples
Major supply chain attacks include:
- SolarWinds attack
- Log4Shell vulnerability
- Malicious NPM packages
Investigation Indicators
SOC teams should monitor:
- unusual package downloads
- unauthorized CI/CD pipeline changes
- suspicious container images
- malicious dependency updates
A04: Cryptographic Failures
Cryptographic failures occur when sensitive data is not properly protected using encryption. Previously known as Sensitive Data Exposure.
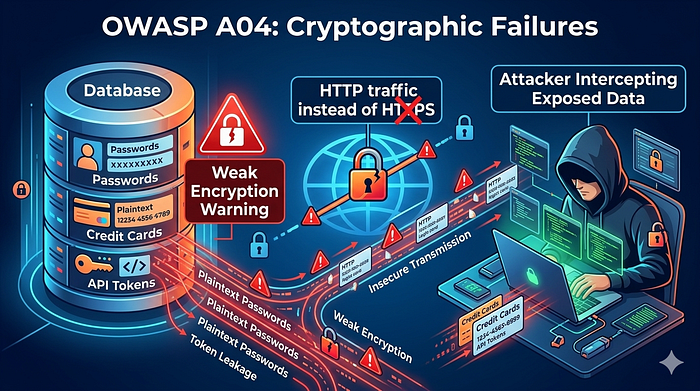
Examples
- Plaintext passwords
- Weak encryption algorithms
- Improper TLS configuration
- Hardcoded keys
- Exposed API tokens
Investigation Indicators
Look for:
- Sensitive information in logs
- Base64 encoded secrets
- Insecure HTTP traffic
- Token leakage
Example log indicator:
POST /login
password=admin123A05: Injection
Injection vulnerabilities occur when untrusted input is executed by an interpreter.

Common injection types include:
- SQL Injection
- OS Command Injection
- LDAP Injection
- NoSQL Injection
Example SQL Injection Payload
' OR '1'='1Attack Flow
- Attacker submits malicious input.
- Application inserts input into database query.
- Database executes malicious query.
Investigation Indicators
Look for:
UNION SELECT
OR 1=1
--
sleep(10)Example log:
GET /login?username=admin' OR 1=1--A06: Insecure Design
This vulnerability occurs when applications are designed without proper security considerations. Unlike coding bugs, insecure design reflects architectural weaknesses.

Examples
- No rate limiting
- Missing authorization workflows
- Business logic abuse
- Weak password reset flows
Investigation Indicators
Examples include:
- mass account creation
- scraping attacks
- inventory hoarding bots
- API abuse
These attacks often appear as normal traffic but at abnormal scale.
A07: Authentication Failures
Authentication failures occur when identity verification mechanisms are weak or improperly implemented.

Common Attack Types
- Credential stuffing
- Password spraying
- Brute force attacks
- Session fixation
- Weak session tokens
Example Investigation Logs
Failed Login Attempts: 120
IP Address: 185.220.x.x
Usernames Tried: 50This pattern often indicates automated credential stuffing attacks.
A08: Software or Data Integrity Failures
This category involves failures in verifying the integrity of software, updates, or serialized data.

Examples
- insecure deserialization
- unsigned software updates
- tampered code repositories
- malicious plugin installations
Attack Example
An attacker uploads a malicious serialized object that executes code during deserialization.
Example indicator:
Serialized payload detected
rO0ABXNy...A09: Security Logging and Alerting Failures
This category focuses on visibility gaps in detecting attacks. Even if an attack occurs, poor logging prevents detection.

Common Problems
- Missing logs
- Logs not centralized
- No alerting on suspicious events
- Delayed monitoring
Investigation Challenges
Breaches often go unnoticed for months because:
- authentication logs are missing
- privilege escalation is not logged
- SIEM alerts are misconfigured
This vulnerability highlights why SOC monitoring is critical.
A10: Mishandling of Exceptional Conditions
This is a new category introduced in OWASP Top 10:2025.

Exceptional conditions occur when applications encounter unexpected situations such as:
- invalid inputs
- memory failures
- network errors
- race conditions
If the application fails to handle these situations correctly, attackers can exploit them.
Examples
- application crashes revealing stack traces
- unhandled exceptions exposing system paths
- failing open instead of failing closed
- incomplete transactions
Attack Example
Sending malformed input:
AAAAAAAAAAAAAAAAAAAAAAAAAAAAmay trigger buffer overflows or crash the system.
Investigation Indicators
SOC analysts should monitor:
- repeated application errors
- stack traces in responses
- abnormal exception logs
- high error-rate spikes
6. OWASP Tools Every Security Analyst Should Know
- OWASP ZAP: An open-source web vulnerability scanner used for: Automated scanning, Fuzzing, Penetration testing.
- OWASP WebGoat: A vulnerable web application used to learn hacking techniques.
- OWASP Juice Shop: A modern intentionally vulnerable application. Many bug bounty beginners practice here.
7. Real-World Attacks Linked to OWASP
Many major breaches occurred due to OWASP vulnerabilities.
Examples:
- Equifax Breach -> Vulnerable Components
- Uber Breach -> Broken Access Control
- Yahoo Breach -> Authentication Failures
- Capital One Breach -> SSRF
Understanding OWASP means understanding real-world attacks.
8. Why Every SOC Analyst Must Learn OWASP
If you are investigating:
- Web attack alerts
- WAF alerts
- SIEM alerts
- API abuse
- Authentication anomalies
You will constantly see OWASP patterns.
Learning OWASP helps you:
- Detect attacks faster
- Understand attacker behavior
- Improve detection engineering
- Strengthen incident response
9. Final Thoughts
Web applications are the largest attack surface on the internet today.
Attackers constantly exploit vulnerabilities like:
- Injection
- Broken access control
- Misconfiguration
- Authentication flaws
The OWASP framework helps defenders stay ahead of attackers.
If you are working in: SOC, Threat detection, Web security, Penetration testing, Bug bounty.
Then mastering OWASP is non-negotiable.