Q1. Identify one strong phishing indicator from the email subject line that reflects attacker intent. What is the exact subject?
A: [ACTION REQUEST] You have been red flagged for violating our terms

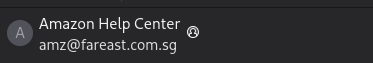
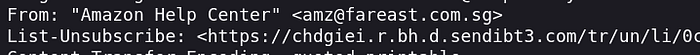
Q2. The attacker attempts to impersonate a trusted brand. What email identity is presented to the user?
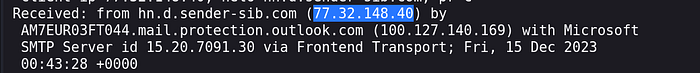
Q3. While analyzing the email path, determine the origin of the message. What IP should be considered the true sending source?
A:77.32.148.40
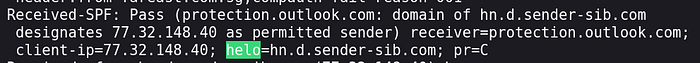
Q4. During transmission, attackers often rely on third-party infrastructure. What domain was used during the SMTP handshake (HELO/EHLO)? ""SMTP HELO/EHLO is the first massage was sent between two servers before transfer an email""
A: hn.d.sender-sib.com
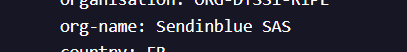
Q5. Based on infrastructure indicators, identify the country name that generates this attack.
A:France
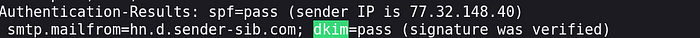
Q6. Despite appearing legitimate, analyze whether the sending server is authorized. What is the SPF verdict?
A: pass
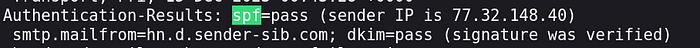
Q7. Verify message integrity using cryptographic signatures. What is the DKIM result?
A:pass
Q8. Evaluate domain alignment policy. What is the DMARC result
A: fail

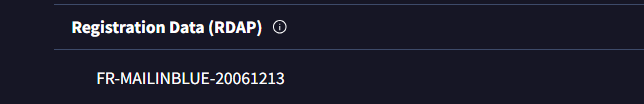
Q9. Using threat intelligence, determine the network name typically associated with this infrastructure.
A:FR-MAILINBLUE-20061213
Q10. When tracing bounce handling, what return domain reveals the actual sending infrastructure?
A: hn.d.sender-sib.com
Q11. Using ASN/IP intelligence, determine the organization name (ISN) typically associated with this infrastructure.
A: Sendinblue SAS
Q12. During email analysis, identifying the exact time a message was processed by security infrastructure can help in timeline reconstruction. Extract the original arrival timestamp of this email based on 12 hour system.
A: 2023/12/15 12:43:28

Q13. Instead of directly embedding malicious domains, attackers often use tracking/redirection layers. Identify the main domain used for this purpose.
A: chdgiei.r.bh.d.sendibt3.com
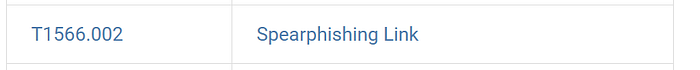
Q14. What phishing sub-technique name?
A: Spearphishing Link
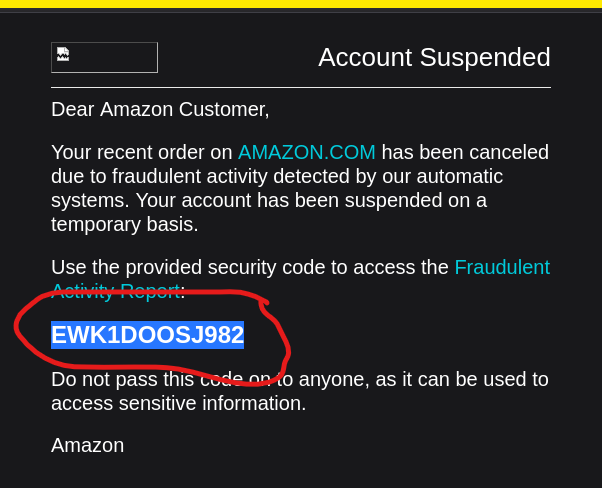
Q15. From content and branding, which organization is being impersonated?
A:Amazon
Q16. Identify the value (code) used to simulate legitimacy and urgency within the email body.
A:EWK1DOOSJ982
Q17. According to MITRE ATT&CK, Which software name associated with this sub-technique there contributors are Arie Olshtein, Check Point; Kobi Eisenkraft, Check Point ?
A: By searching, the result is (Pony) .
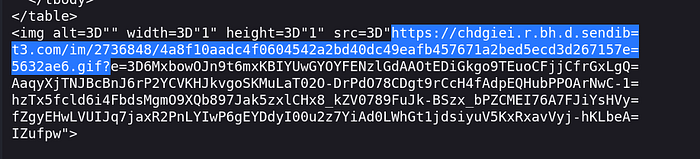
Q18. Identify a hidden image used by attackers to track user interaction with the email, type the path of this image.
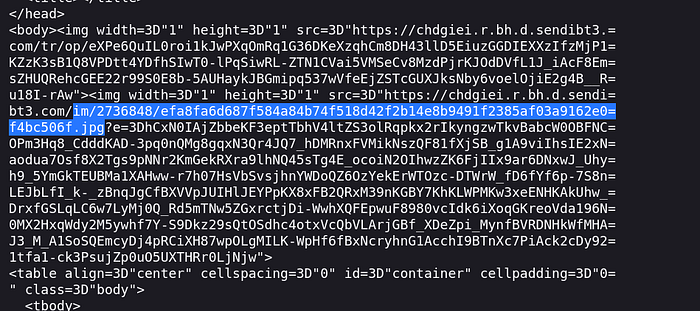
Q19. Identify a hidden gif used by attackers to track user interaction with the email, type the path of this gif.
Q22. Map this attack to MITRE ATT&CK. What is the main technique ID?
A:T1566

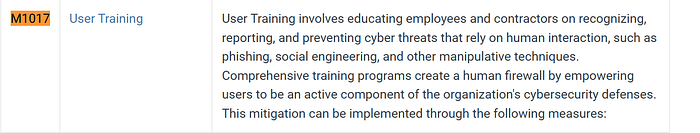
Q23. Identify a mitigation strategy focused on increase awareness level
A:M1017