In this article, I'll be sharing a short story from one of my recon sessions where directory bruteforcing led me to an exposed /phpmyadmin panel. A small misconfiguration ended up exposing a sensitive database interface to the public internet. Let's take a look at how it all happened.

How It All Started
When I visited the main domain, the first thing I did was check it with Wappalyzer to see what technologies were being used. I noticed that the application was running on PHP. Since the backend was built on PHP, I used dirsearch to find some PHP endpoints, and that's where things started getting interesting.
The Discovery
I opened my terminal, typed this basic command, and started scanning for the hidden directories ..
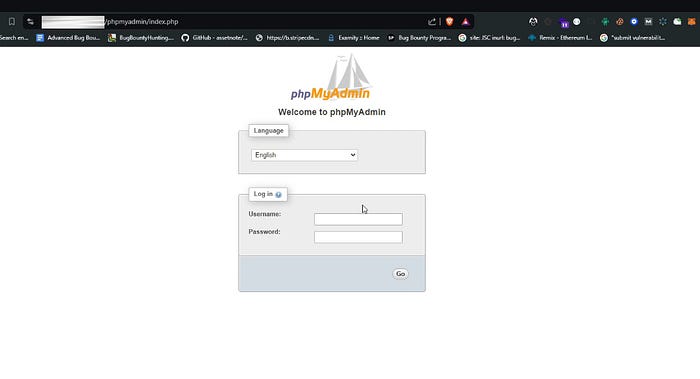
dirsearch -u https://example.com/One of the results that caught my attention was /phpmyadmin/index.php which returned a 200 OK response. Seeing that it was accessible, I immediately opened it in the browser to take a closer look.
When I opened it, I was presented with a standard PhpMyAdmin login page.
Out of curiosity, I tried logging in with random credentials just to observe the server's response.
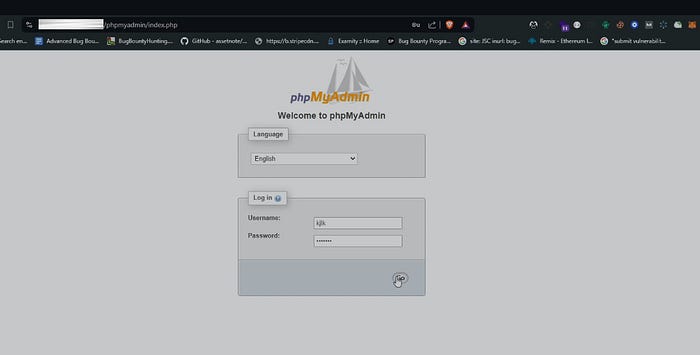
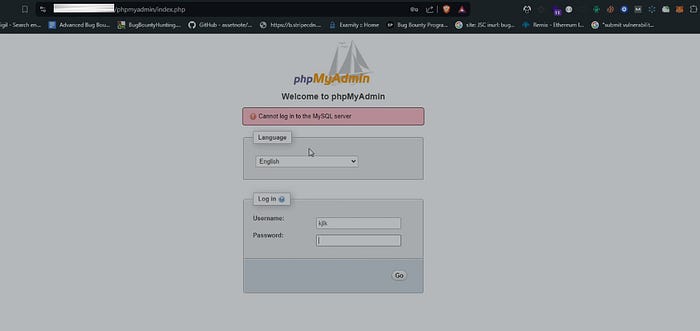
As expected, the login failed and returned an error saying:
"Cannot log in to the MySQL server."
Instead of stopping there, I decided to dig a little deeper. I performed directory Bruteforcing again, this time specifically on the /phpmyadmin/ path to see if any additional endpoints were exposed.
That's when I discovered another endpoint /phpmyadmin/setup/ with 200 OK response code.
When I accessed it, I wasn't prompted for any credentials. Instead, I was taken directly to the PhpMyAdmin setup interface without any authentication or authorization checks.
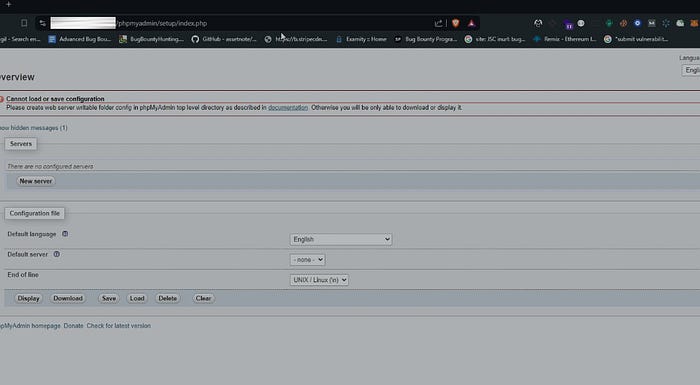
This wasn't just about a visible login page, the setup endpoint was basically letting anyone in without going through authentication.
Impact of the Exposure
Leaving the PhpMyAdmin interface accessible without authentication creates a high-risk situation.

The panel included options like navigation, SQL queries, and import & export functionality, which means direct interaction with the database was possible. With this level of access, an attacker could potentially view data, modify records, or export sensitive information.
Disclosure & Reward
After confirming the issue, I reported it through the CyberBay platform. The team reviewed my submission, validated the finding, and rewarded me with a $420 bounty.

That's all for this write-up. I hope you learned something from this experience.
If you found this helpful, feel free to give it a clap and follow for more security write-ups like this. You can also connect with me on LinkedIn , I'd be happy to connect.
Stay curious, keep hunting, and I'll catch you in the next one. ✌️ Happy Hunting! 🐞