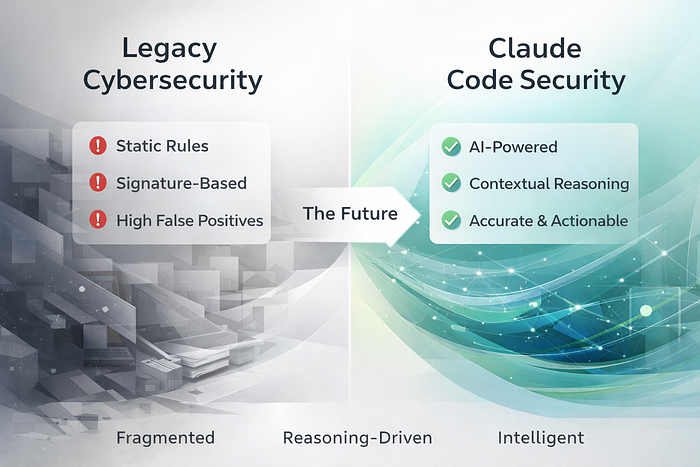
For over two decades, enterprise cybersecurity has relied on deterministic, rule-based tools to protect software systems. Static Application Security Testing (SAST), signature matching, and compliance-driven scanning engines have delivered broad coverage, but not deep understanding. As modern architectures have evolved into distributed, API-driven, microservices-based systems, the gap between pattern detection and contextual reasoning has widened.
Claude Code Security, released recently, represents a structural shift in how application security can operate. Rather than focusing solely on line-level pattern matching, it applies AI-driven contextual analysis across entire repositories. It traces data flows, evaluates cross-file dependencies, examines authorization boundaries, and reasons about system behavior — not just syntax. This enables it to identify vulnerabilities that emerge from logic interactions rather than isolated code smells.
The key differentiator is its structured workflow: Scan → Verify → Patch. It does not simply generate alerts. It attempts to validate findings to reduce false positives and proposes remediation changes, while preserving explicit human approval before any modification is applied. This design addresses two of the largest pain points in enterprise security: alert fatigue and remediation backlog.
Claude Code Security is not positioned as a replacement for legacy SAST or compliance scanners. Instead, it augments them with contextual reasoning capabilities that traditional rule engines cannot provide. The likely future state of DevSecOps is layered security: deterministic rule-based scanning for known risks, AI-powered contextual analysis for complex logic flaws, and human governance for final oversight.
For CTOs, CISOs, and engineering leaders, the strategic implication is clear: security effectiveness will increasingly depend on whether tools can understand system behavior, not merely match patterns. As attackers continue to exploit cross-service logic flaws and emergent vulnerabilities, contextual AI may become a critical layer in secure SDLC maturity.
Anthropic Claude Code Security signals the beginning of AI-native application security — where reasoning, not just detection, becomes central to defense.
For more than two decades, we have relied on rules.
Signatures. Patterns. Heuristics. Static analysis engines.
We built entire security ecosystems on the belief that if we could match known bad patterns, we could prevent breaches.
And for a time, that worked.
But software evolved. Architectures became distributed. Business logic became layered. Microservices started talking to each other in complex, stateful ways.
Attackers adapted.
Our tools largely did not.
The Fundamental Problem: Security Without Understanding
Legacy cybersecurity tools operate deterministically.
They look for:
- Known injection patterns
- Hardcoded secrets
- Misconfigured permissions
- Unsafe library versions
- Suspicious API calls
This is necessary — but insufficient.
Because modern vulnerabilities are often not pattern problems.
They are context problems.
A logic flaw across three services. An authorization gap exposed through an unusual execution path. A subtle misuse of a token across asynchronous flows.
No single file looks wrong.
But the system, as a whole, is exploitable.
Rule engines cannot reason across intent. They cannot understand why the code exists. They cannot infer how data flows in edge conditions.
They match patterns.
Attackers analyze systems.
The Illusion of Coverage
Many enterprises believe they are secure because:
- Their SAST tool shows green
- Their SCA scanner passes
- Their compliance checklist is complete
- Their dashboards are populated
But coverage does not equal comprehension.
You can scan every file in a repository and still miss:
- Business logic vulnerabilities
- Broken access controls triggered by specific workflows
- Multi-step exploit chains
- Race conditions in distributed systems
- Subtle privilege escalation paths
Legacy tools excel at finding known weaknesses.
They struggle with emergent ones.
And emergent weaknesses are what attackers specialize in.
Enter Claude Code Security: Contextual Reasoning Over Pattern Matching
Claude Code Security introduces a fundamentally different approach.
Instead of asking:
"Does this line match a risky pattern?"
It asks:
"How does this system behave?"
It evaluates:
- Cross-file dependencies
- Data propagation paths
- Authorization boundaries
- State transitions
- Logic assumptions
And it attempts to reason about exploitability, not just syntax.
This is the shift.
From static detection to contextual analysis.
From rule matching to system understanding.
Why Context Changes Everything
Consider a realistic enterprise scenario.
A payment API validates tokens correctly. An internal service trusts upstream validation. A caching layer bypasses a secondary authorization check for performance reasons.
Individually, every component appears secure.
- The payment API has proper token validation logic.
- The internal service does not expose public endpoints.
- The caching layer improves latency and reduces load.
Each module passes static analysis. Each codebase returns "no critical vulnerabilities." Each team signs off confidently.
Yet together, they form an exploitable chain.
Here's how.
An attacker discovers that the caching layer stores authorization decisions keyed only on user ID, not on token scope. A previously valid token — even one with narrower permissions — populates the cache. Subsequent requests leverage the cached authorization result without re-evaluating scope.
No single file contains an obvious flaw.
There is no SQL injection. No hardcoded secret. No unsafe deserialization.
The vulnerability emerges from interactions.
From assumptions.
From trust boundaries that were never revalidated downstream.
This is where legacy tools struggle.
Traditional SAST engines analyze files or limited call graphs. They flag risky patterns within defined contexts. They do not simulate real-world execution across distributed services with state persistence and caching behavior.
They detect symptoms.
They do not reason about systems.
Contextual AI, on the other hand, attempts to follow the flow:
- How is the token validated?
- Where is the authorization result stored?
- What assumptions are made downstream?
- Are there branches where checks are skipped?
- Can state persist beyond its intended lifecycle?
Instead of asking, "Is this line dangerous?" It asks, "Can this system be abused?"
That difference is not incremental. It is structural.
Because modern vulnerabilities are rarely isolated mistakes.
They are emergent properties of interconnected systems.
In distributed architectures, risk is not confined to a function. It lives in:
- Service-to-service trust
- Asynchronous messaging
- Shared caches
- State transitions
- Performance optimizations
- Implicit architectural assumptions
The attack surface is not a file.
It is the system's behavior over time.
Legacy cybersecurity was built for static code. Modern exploits target dynamic interactions.
When tools cannot reason across those interactions, they offer coverage without comprehension.
Context changes everything because software today is not a collection of files.
It is a living network of assumptions.
And vulnerabilities hide in those assumptions.
The False Positive Crisis
Another hidden issue in legacy cybersecurity is noise.
Security teams face:
- Thousands of alerts
- Low signal-to-noise ratio
- Manual triage fatigue
- Growing vulnerability backlogs
When everything looks urgent, nothing is urgent.
Claude Code Security attempts to address this through a verify layer — re-evaluating findings before surfacing them.
If this works at scale, it could reduce:
- Alert fatigue
- Wasted triage cycles
- Developer resistance to security tools
Security productivity matters as much as detection capability.
This is not about replacing SAST
It is tempting to frame this conversation as a battle: legacy tools versus AI-native security.
That would be a mistake.
Traditional SAST tools are deterministic. They are engineered around explicit rules, well-defined vulnerability classes, and repeatable detection logic.
For known risk categories — SQL injection patterns, unsafe deserialization, hardcoded credentials, insecure cryptographic usage — they remain reliable and necessary.
They are predictable. They are auditable. They are compliance-friendly.
And compliance still matters.
Claude Code Security, by contrast, operates probabilistically. It reasons across context. It evaluates interactions, intent, and data flow. It attempts to identify vulnerabilities that emerge from system behavior rather than isolated code constructs.
These are fundamentally different capabilities.
Deterministic engines excel at precision within defined boundaries. Reasoning systems excel at exploring relationships beyond rigid boundaries.
The future of application security is not either/or.
It is layered.
- Rules for known risks.
- AI for contextual reasoning.
- Humans for final authority and governance.
Think of it as security depth rather than security replacement.
SAST continues to act as a baseline enforcement layer — ensuring coding standards, known vulnerability classes, and regulatory alignment.
AI-driven contextual analysis becomes an intelligence layer — identifying exploit chains, cross-service logic flaws, and emergent weaknesses that static rules cannot easily model.
Humans remain the decision layer — validating exploitability, prioritizing risk, and enforcing architectural discipline.
Organizations that attempt to rely solely on rule-based scanning will increasingly struggle with blind spots.
Organizations that rely solely on AI without deterministic controls will introduce governance risks.
The strategic advantage lies in orchestration.
When deterministic scanning reduces noise, AI narrows focus, and human reviewers make final calls, security maturity accelerates.
The result is not just better detection.
It is faster remediation. Lower false positive fatigue. Improved developer trust in security tooling. And ultimately, stronger resilience against modern attack vectors.
The companies that understand this layering early will not only move faster.
They will move safer.
And in cybersecurity, speed without safety is just deferred risk.
The Strategic Question
For years, boardrooms have asked a simple question:
"Do we have security tooling?"
The answer is almost always yes.
There are dashboards. There are scanners. There are compliance reports. There are quarterly audits.
But that question is outdated.
The real question is far more uncomfortable:
Does our security tooling understand our system?
Modern software is not a static asset. It is a distributed organism — APIs calling APIs, services trusting services, caches persisting decisions, asynchronous events triggering state transitions.
Understanding security today requires understanding behavior.
Attackers do not scan code the way legacy tools do. They analyze flows. They test assumptions. They look for trust boundaries that can be bent, not just broken.
They reason about systems.
If your defenses cannot reason, they are limited to reacting after patterns emerge.
If they cannot model cross-service interactions, they miss exploit chains. If they cannot evaluate intent, they miss logic flaws. If they cannot prioritize based on real exploitability, they generate noise instead of insight.
Security that cannot reason is security that waits.
And in an AI-accelerated threat landscape, waiting is exposure.
The strategic conversation must evolve from tool inventory to system intelligence.
Because the future of defense will not be decided by how many alerts you generate.
It will be decided by how deeply your tools understand the system they are protecting.
Conclusion: The Security Industry is at a Crossroads
For decades, legacy cybersecurity firms have thrived on expanding rule libraries.
Every new vulnerability class meant a new signature. Every new exploit technique meant another detection pattern. Every new compliance mandate meant another scanning module.
It was scalable. It was profitable. It was defensible.
But it was never truly intelligent.
Claude Code Security signals something more disruptive than just another AI feature. It signals a shift from pattern detection to contextual reasoning.
And that shift is existential.
If AI systems can:
- Understand cross-service logic
- Trace real exploit paths
- Reduce false positives meaningfully
- Propose validated remediation
Then the core value proposition of legacy rule-based security firms begins to erode.
Because at that point, the differentiator is no longer coverage. It is comprehension.
Cybersecurity vendors now face a stark choice:
Evolve into AI-native reasoning platforms — or Gradually become commoditized scanning utilities.
The market will not wait.
Attackers are already using AI to analyze systems faster than humans can review them. Enterprises will not continue paying premium prices for tools that generate noise without insight.
Security is entering its most consequential transition since the rise of cloud computing.
Those who adapt will lead. Those who hesitate will survive — but shrink. Those who ignore the shift may become irrelevant.
This is not incremental innovation.
It is a structural rewrite of how defense works.
And for the first time in decades, cybersecurity firms themselves are the ones facing disruption.