Authentication mechanisms are a critical component of web application security. However, weak credential management and insufficient protections against login attempts can expose systems to targeted credential attacks.
In this write-up, I demonstrate how valid login credentials can be discovered through a targeted credential attack using two different approaches:
- Burp Suite Intruder (Cluster Bomb attack)
- ffuf (Command-line fuzzing tool)
This lab highlights how attackers can efficiently test combinations of usernames and passwords when login attempts are limited by rate-limiting or account lockout mechanisms.
This article is part of my Web Security Series, where I document practical web security labs and explain common authentication and authorization vulnerabilities.
Understanding Targeted Credential Attacks
A targeted credential attack (sometimes referred to as credential stuffing or constrained brute-force) attempts combinations of usernames and passwords against an authentication endpoint when valid credentials are unknown.
Unlike traditional brute-force attacks that test thousands of combinations, targeted attacks are designed to operate within strict attempt limits.
When an application enforces protections such as:
- Login rate limiting
- Account lockouts
- Attempt thresholds
attackers may use a clustered approach, testing a small curated list of usernames against a small curated list of passwords.
This approach maximizes the probability of discovering valid credentials while remaining within the allowed attempt budget.
When This Attack Technique Is Used
This attack method is typically used during the exploitation phase of a penetration test when:
- No valid credentials are available.
- The application limits the number of login attempts (for example, 5 attempts).
- A small list of high-probability usernames and passwords is available.
- Attempts must be carefully managed to avoid triggering account lockouts or security alerts.
Lab Objective
The objective of this lab is to:
Discover valid login credentials by testing combinations of usernames and passwords within a strict attempt limit using both Burp Suite Intruder and the ffuf fuzzing tool.
Lab Environment
This challenge lab provides a login page where credentials must be discovered through controlled attack techniques.

The lab allows only five login attempts, requiring a carefully planned credential testing strategy.
Method 1 — Credential Discovery Using Burp Suite Intruder
Burp Suite provides a powerful feature called Intruder, which allows testers to automate parameter manipulation and test multiple input combinations.
In this lab, the Cluster Bomb attack type is used to test combinations of usernames and passwords.
Step 1 — Generate a Sample Login Request
First, submit any credentials on the login page to generate a request.
Example:
username = jeremy
password = letmein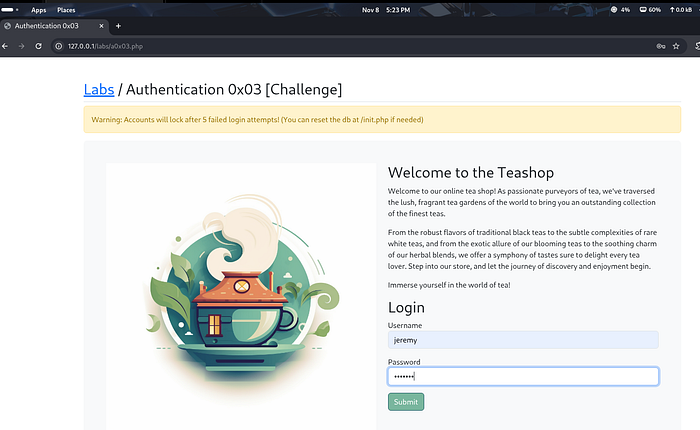
With Burp Proxy enabled, navigate to:
Proxy → HTTP HistoryLocate the captured POST request to the authentication endpoint.

Right-click the request and select:
Send to IntruderStep 2 — Configure Intruder Positions
Inside Burp Intruder, mark the username and password parameters as payload positions.
Navigate to:
Intruder → PositionsAdd markers to both parameters and select the attack type:
Cluster Bomb
The cluster bomb attack will test all combinations of the selected username and password lists.
Step 3 — Load Username Wordlist
A username list can be obtained from the SecLists collection.
Example command to locate username lists:
find /usr/share/seclists -name '*user*'For this lab, the following list is used:
/usr/share/seclists/Usernames/top-usernames-shortlist.txtLoad this list into the username payload slot in Burp Intruder.
Step 4 — Prepare a Small Password List
Because the application limits login attempts, only a small set of high-probability passwords should be used.
Using SecLists:
head /usr/share/seclists/Passwords/xato-net-10-million-passwords-10.txtExample selected passwords:
123456
password
password123
letmeinLoad these passwords into the password payload slot.
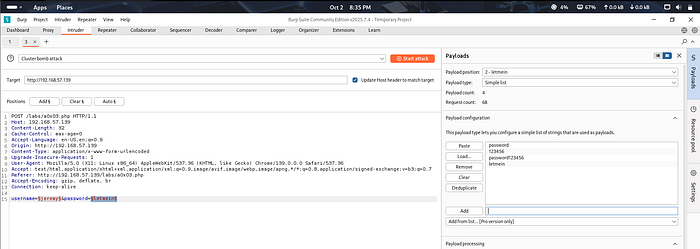
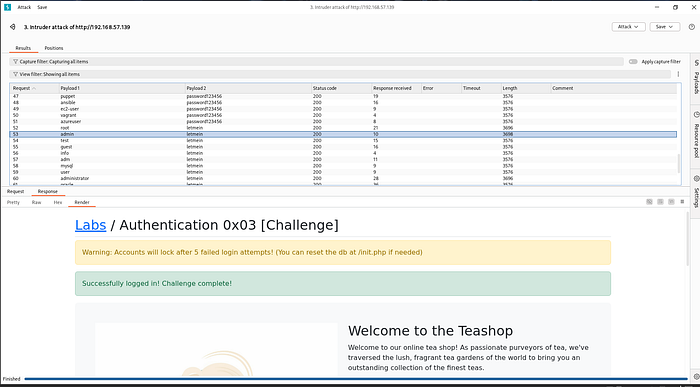
Step 5 — Launch the Cluster Bomb Attack
Start the attack by clicking:
Start AttackBurp Intruder will automatically test all username and password combinations.
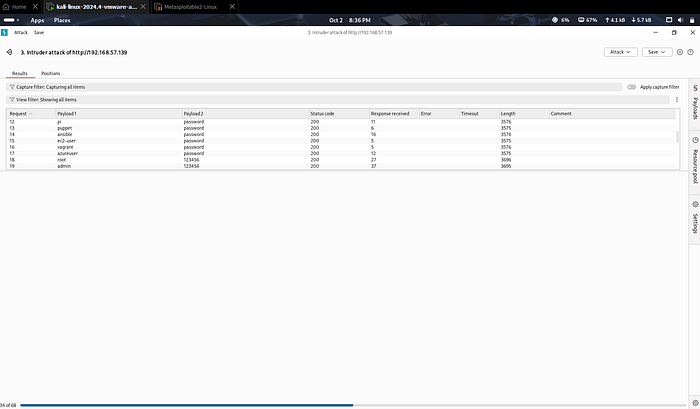
Step 6 — Analyze the Results
After the attack completes, analyze the responses by examining:
- Response status codes
- Response length
- Content differences
In this lab, the successful credential pair was discovered as:
username = admin
password = letmeinEntering these credentials into the login page confirms successful authentication.
Method 2 — Credential Discovery Using ffuf
While Burp Intruder provides a graphical interface for attacks, similar techniques can also be performed using command-line tools such as ffuf.
ffuf is a fast web fuzzing tool commonly used for automated testing of parameters and endpoints.
Step 1 — Capture the Authentication Request
As before, generate a login request and capture it using Burp Proxy.
Navigate to:
Proxy → HTTP HistoryCopy the raw request and save it to a file:
request2.txtStep 2 — Modify the Request with Fuzz Markers
Open the request file in a text editor:
mousepad request2.txtReplace the username and password values with fuzz markers:
username=FUZZUSER&password=FUZZPASS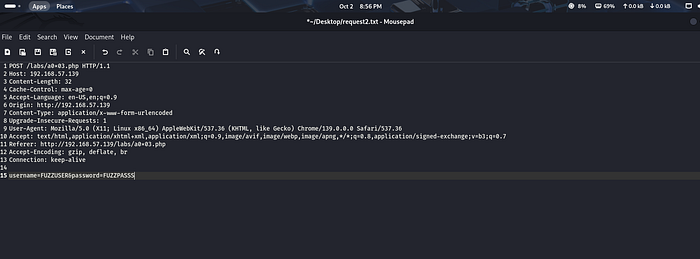
Step 3 — Create a Small Password File
Create a local password file named pass.txt containing common passwords:
123456
password
password123
letmeinStep 4 — Run ffuf in Cluster Bomb Mode
Execute the following command:
ffuf -request request2.txt -request-proto http -mode clusterbomb \
-w /usr/share/seclists/Usernames/top-usernames-shortlist.txt:FUZZUSER \
-w pass.txt:FUZZPASSExplanation:
-requestloads the raw HTTP request-mode clusterbombtests all combinations-w <file>:<marker>maps wordlists to parameters
Step 5 — Identify Valid Credentials
During execution, ffuf highlights responses that differ from the baseline.
By analyzing these responses, the correct credentials were again identified as:
admin : letmein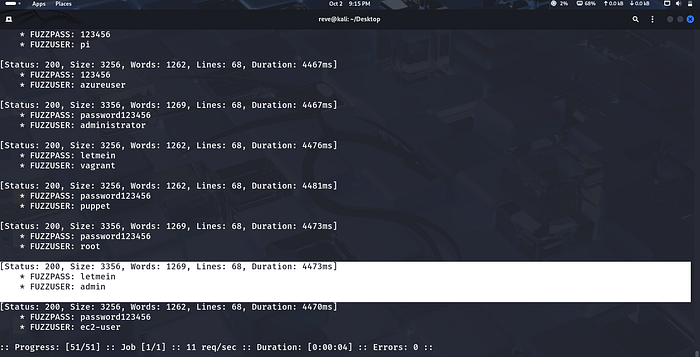
Why This Vulnerability Occurs
This vulnerability occurs because the application lacks sufficient protection mechanisms such as:
- Strong password policies
- Account lockout enforcement
- Login attempt rate limiting
- Multi-factor authentication
Without these controls, attackers can systematically test credential combinations until a valid pair is discovered.
Security Impact
Weak authentication protections may lead to:
- Unauthorized account access
- Privilege escalation
- Exposure of sensitive user data
- System compromise
Credential attacks remain one of the most common techniques used in real-world breaches.
How to Prevent Credential Attacks
Developers should implement several protective mechanisms, including:
- Account lockouts after multiple failed login attempts
- Rate limiting on authentication endpoints
- CAPTCHA or bot detection systems
- Multi-factor authentication
- Monitoring suspicious login behavior
These controls significantly reduce the effectiveness of automated credential attacks.
Conclusion
This lab demonstrated how targeted credential attacks can be performed using both Burp Suite Intruder and ffuf.
By carefully selecting a small set of usernames and passwords and applying a cluster bomb attack strategy, it was possible to discover valid login credentials within a strict attempt limit.
Understanding these attack techniques helps security professionals identify weaknesses in authentication systems and design more secure login mechanisms.
Connect With Me
If you found this write-up helpful, feel free to follow my cybersecurity learning journey.
🔗 LinkedIn: www.linkedin.com/in/laibakashif0011