A Bug Bounty Hunter's Guide to Finding Real-World Weaknesses
✍️ By Ghostyjoe
🎯 Why IoT Misconfigurations Matter
IoT devices are everywhere — and many are deployed with:
- default settings
- weak authentication
- exposed services
- outdated firmware
Unlike traditional web apps, IoT devices often lack proper security hardening.
For bug bounty hunters, this means:
👉 misconfigurations are often more common than complex vulnerabilities
🧠 What Is an IoT Misconfiguration?
An IoT misconfiguration happens when a device is:
- exposed unnecessarily
- using insecure defaults
- improperly secured
- leaking information
Examples include:
Open admin panel
Default credentials
Public SNMP access
Exposed debug endpoints
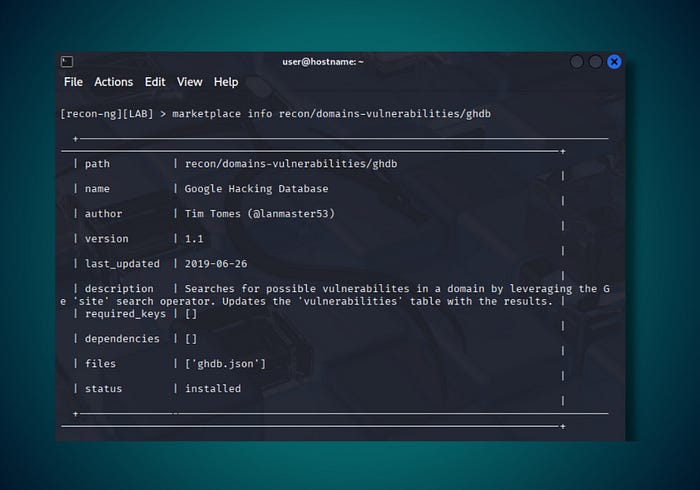
Unrestricted APIs🔎 Step 1 — Finding Misconfigured IoT Devices
Researchers often start with:
- subdomain enumeration
- device search engines
- port scanning (authorized only)
Look for assets like:
iot.company.com
device.company.com
camera.company.com
printer.company.com🖥️ Screenshot — IoT Recon Discovery

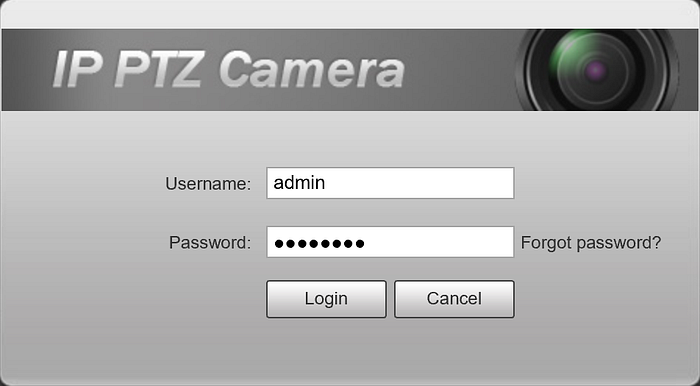
🔐 Step 2 — Identifying Open Admin Panels
Many IoT devices expose web interfaces.
Common findings:
- login pages
- dashboards
- status panels
🖥️ Screenshot — IoT Admin Panel


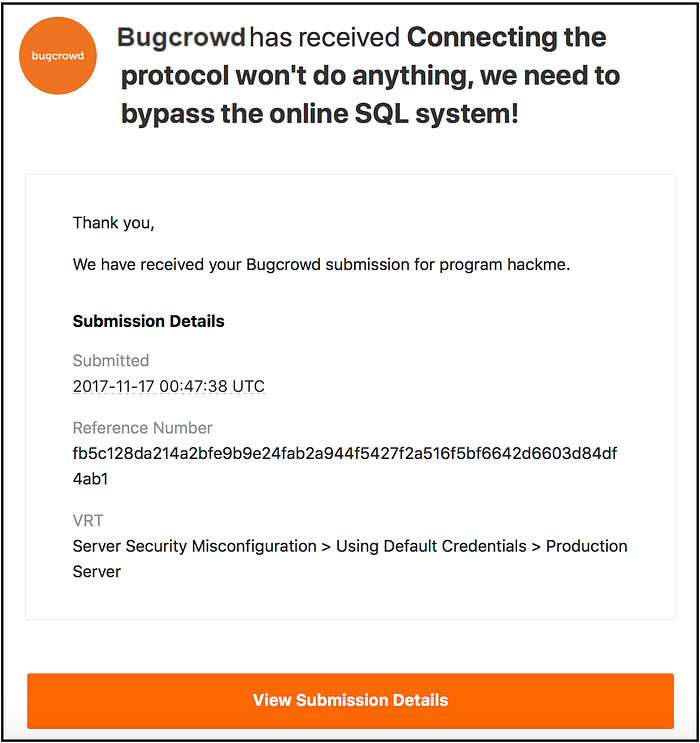
🔑 Step 3 — Default Credential Weakness
Some devices still use default credentials such as:
admin / admin
admin / password
root / 0000⚠️ In bug bounty:
- Only test credentials if allowed
- Avoid brute forcing
- Follow program policy
🖥️ Screenshot — Login Interface

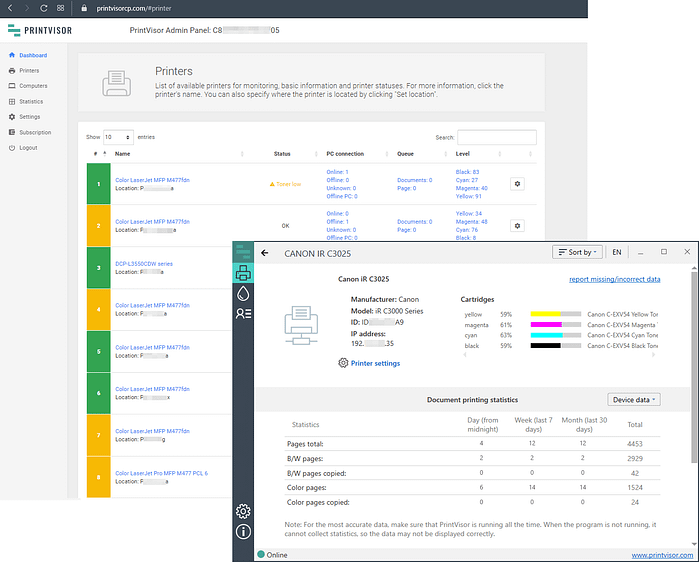
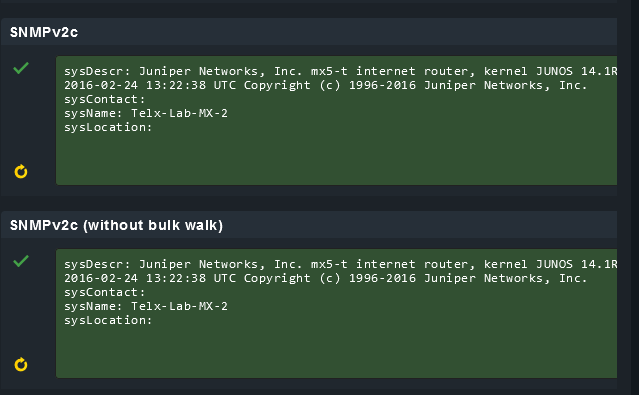
📡 Step 4 — SNMP Misconfiguration
SNMP is often left open with default community strings.
Example (lab only):
snmpwalk -v2c -c public target-ipPossible data exposure:
- device name
- firmware version
- network details
🖥️ Screenshot — SNMP Data Leak

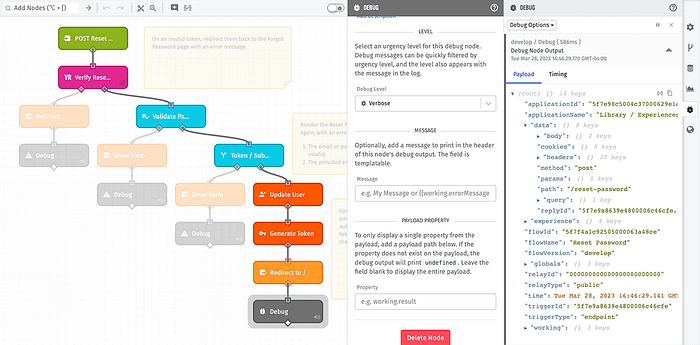
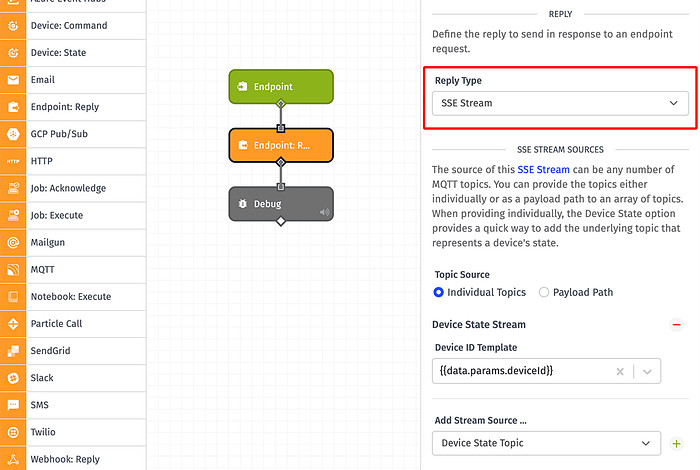
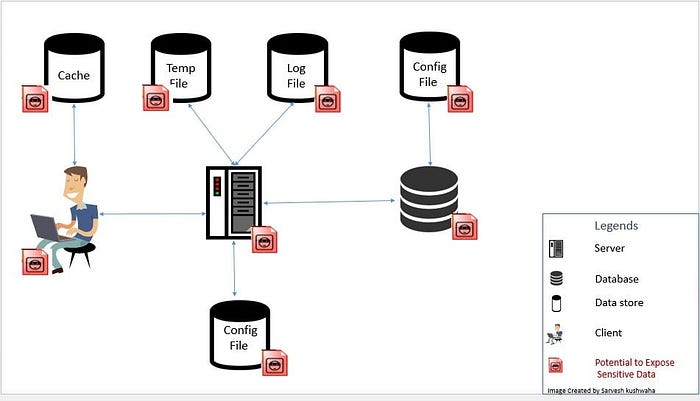
🌐 Step 5 — Exposed APIs & Debug Endpoints
Many IoT systems expose APIs such as:
/api/status
/api/device
/debug
/configThese endpoints may return:
- JSON device data
- configuration details
- internal identifiers
🖥️ Screenshot — API Response Data


🔌 Step 6 — Open Services & Ports
Common IoT ports:
23 → Telnet
80 → Web panel
554 → RTSP (cameras)
8080 → Alternate panel
9100 → PrintersOpen services may indicate:
- misconfiguration
- unnecessary exposure
- outdated services
🖥️ Screenshot — Port Scan Results


💥 What "Exploitation" Means in Bug Bounty
In a legal and ethical context, exploitation often means:
✔ proving access ✔ demonstrating data exposure ✔ showing misconfiguration impact ✔ documenting risk
NOT:
❌ taking control of devices ❌ causing disruption ❌ accessing private data
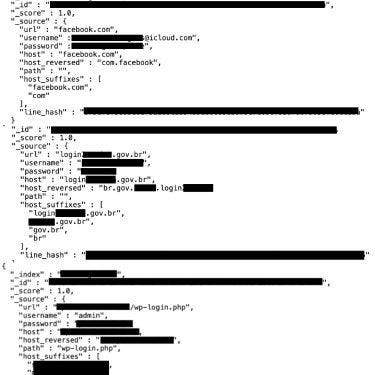
🧠 Example Safe Findings
Valid findings may include:
- exposed admin panel without auth
- sensitive info via API
- SNMP information leak
- version disclosure leading to known CVEs
🖥️ Screenshot — Example Finding Evidence

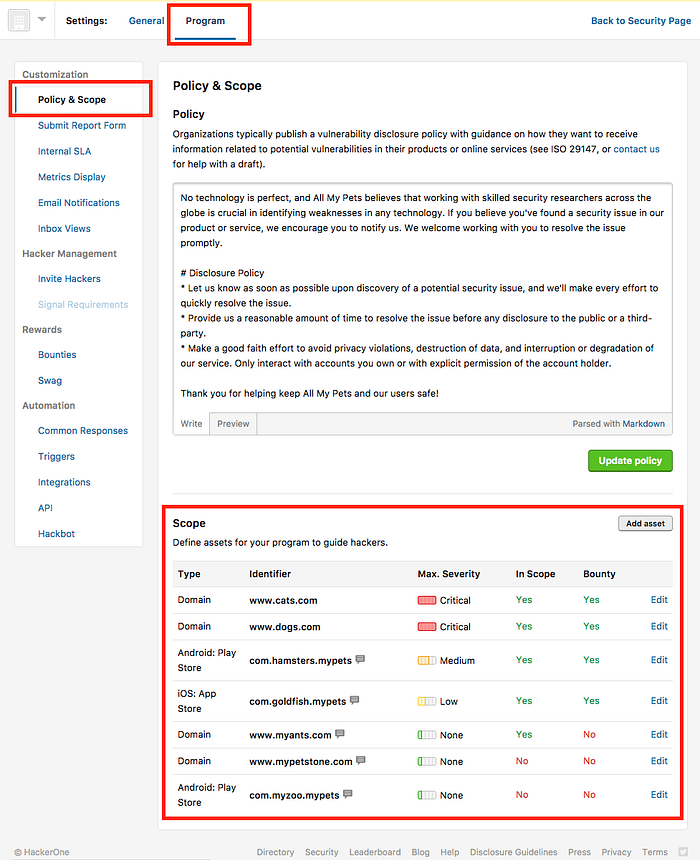
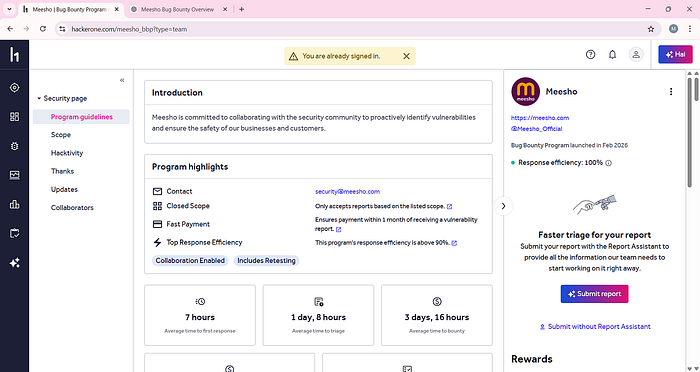
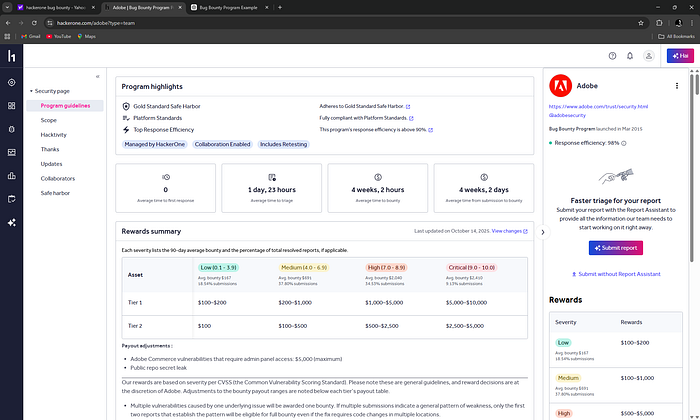
🎯 Bug Bounty Rules (Critical)
Before testing:
✔ check scope ✔ confirm asset ownership ✔ verify allowed techniques
🖥️ Screenshot — Scope Rules Example
🛡️ Defensive Takeaways
Organizations should:
- disable unused services
- update firmware
- restrict external access
- remove default credentials
- segment IoT networks
⚖️ Ethical Use & Disclaimer
This article is for educational and authorized testing purposes only.
Never test:
- systems without permission
- internal infrastructure
- sensitive environments
Always follow:
- bug bounty rules
- legal guidelines
- responsible disclosure
🚀 Final Thoughts
IoT misconfigurations are everywhere.
They are often:
👉 simple 👉 overlooked 👉 impactful
For bug bounty hunters, understanding how to identify them safely can lead to valuable and valid findings.
👏 If you found this useful, follow for more Ghostyjoe content.
☕ Support my work: https://buymeacoffee.com/ghostyjoe


