The Rise of Autonomous AI Hackers in Modern Application Security
As software development accelerates, security testing often struggles to keep up. Many organizations deploy new code daily or even hourly, yet traditional penetration testing typically happens only once or twice a year. This gap creates a dangerous window where vulnerabilities may remain unnoticed.
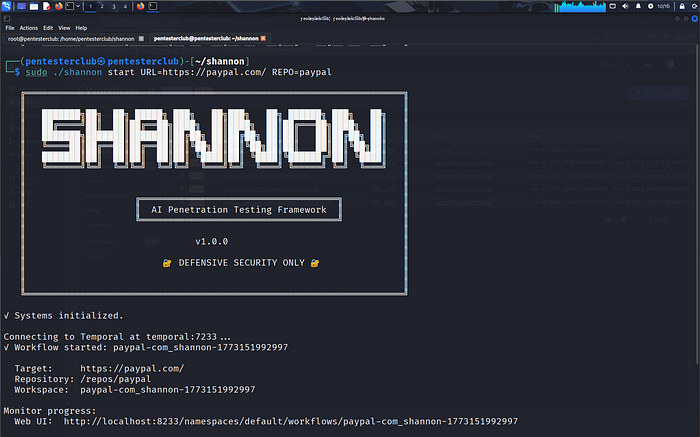
Enter Shannon AI Penetration Testing Framework — an autonomous AI pentesting system designed to continuously test web applications and discover real, exploitable vulnerabilities before attackers do.
In this article, we explore what Shannon is, how it works, and why it represents a major step forward in AI-driven cybersecurity.
What is Shannon?
Shannon is a fully autonomous AI penetration tester designed to discover real vulnerabilities in web applications. Unlike traditional scanners that simply report potential issues, Shannon attempts to actively exploit vulnerabilities to prove they are real.
Its core mission is simple:
Break your application before attackers do.
The system analyzes application source code, explores the running application using browser automation, and attempts real attack techniques such as injection attacks or authentication bypasses to validate vulnerabilities.
This approach dramatically reduces false positives, a common problem in automated vulnerability scanners.
The Problem Shannon Solves
Modern development tools such as AI coding assistants and rapid CI/CD pipelines allow developers to ship code at unprecedented speed.
However, security testing often lags behind.
Typical workflow:
- Developers release code daily
- Security teams run pentests once or twice a year
- Vulnerabilities remain unnoticed for months
Shannon addresses this by acting as an on-demand AI penetration tester that can run security testing whenever needed.
Instead of waiting for a manual pentest, developers can continuously validate their applications before deployment.
Key Features of Shannon
Fully Autonomous Pentesting
Shannon can run a penetration test with a single command. The AI handles tasks such as:
- authentication workflows
- browser navigation
- reconnaissance
- vulnerability analysis
- exploitation attempts
- final reporting
This allows security teams to automate repetitive tasks while focusing on complex analysis.
Proof-Based Vulnerability Detection
Traditional scanners often generate thousands of alerts that may not be exploitable.
Shannon follows a strict rule:
No exploit → No report
It only reports vulnerabilities if it can successfully exploit them and demonstrate the impact using a proof-of-concept.
This dramatically improves the quality of security findings.
Code-Aware Security Testing
Shannon performs white-box analysis, meaning it has access to the application's source code.
By analyzing the codebase, it can:
- trace user input flows
- identify dangerous functions
- detect vulnerable endpoints
- guide its exploitation strategy
This allows the AI to perform more intelligent attacks compared to purely black-box scanners.
Integrated Security Tooling
To enhance reconnaissance and testing, Shannon integrates well-known security tools including:
- Nmap
- Subfinder
- WhatWeb
- Schemathesis
These tools help the AI understand infrastructure, services, and APIs during the discovery phase.
Shannon's Four-Phase Pentesting Architecture
Shannon mimics how a professional penetration tester approaches security testing.
Its workflow consists of four main phases.
1. Reconnaissance
The system first builds a complete attack surface map of the application.
During this stage Shannon:
- analyzes the source code
- scans infrastructure
- explores the web application via automated browsing
- identifies endpoints and authentication mechanisms
This produces a detailed map of possible entry points.
2. Vulnerability Analysis
Next, specialized AI agents analyze the application for vulnerabilities.
Each agent focuses on a specific vulnerability category such as:
- injection attacks
- cross-site scripting (XSS)
- authentication flaws
- server-side request forgery (SSRF)
The agents generate hypotheses about potential attack paths.
3. Exploitation
This phase attempts to turn vulnerability hypotheses into real attacks.
Shannon uses:
- browser automation
- command-line exploitation tools
- custom scripts
If the AI successfully executes the exploit, it records the vulnerability. Otherwise, the hypothesis is discarded.
4. Reporting
Finally, Shannon generates a professional penetration testing report containing:
- verified vulnerabilities
- attack steps
- reproducible proof-of-concept exploits
- technical impact analysis
Only validated vulnerabilities appear in the final report.
Real-World Performance
In benchmark testing, Shannon demonstrated impressive results.
For example, when tested against intentionally vulnerable applications like OWASP Juice Shop, Shannon discovered more than 20 critical vulnerabilities, including authentication bypass and database data extraction.
The framework has also achieved 96.15% success rate on the XBOW benchmark, highlighting its effectiveness in automated vulnerability discovery.
Shannon Lite vs Shannon Pro
The project currently offers two versions.
Shannon Lite
- Open source (AGPL-3.0)
- Designed for researchers and security teams
- Supports white-box application testing
Shannon Pro
- Enterprise version
- Advanced data-flow analysis
- CI/CD pipeline integration
- deeper vulnerability detection
The open-source version allows developers to experiment with AI-driven pentesting locally.
Ethical and Security Considerations
Because Shannon actively executes exploits, it must be used responsibly.
The developers emphasize several guidelines:
- Only test systems you own or have permission to test
- Run tests in staging or development environments
- Avoid production systems because exploitation may modify data
Unauthorized scanning or exploitation may violate computer crime laws.
The Future of AI-Driven Pentesting
Tools like Shannon represent a new direction in cybersecurity.
Instead of relying solely on human pentesters or basic scanners, organizations can now deploy AI-powered security agents that continuously test applications.
Benefits include:
- faster vulnerability detection
- fewer false positives
- continuous security testing
- improved DevSecOps integration
As AI models continue to improve, autonomous security systems like Shannon may become a standard part of modern development pipelines.
Final Thoughts
The Shannon AI Penetration Testing Framework demonstrates how AI can transform application security.
By combining source-code analysis, browser automation, and real exploitation techniques, Shannon moves beyond traditional vulnerability scanning and delivers verified, actionable security findings.
While human expertise remains essential, AI-powered pentesting tools will increasingly act as powerful assistants — helping developers secure their applications before attackers can exploit them.