This write-up is based on a training scenario from LetsDefend and is shared for educational purposes only.
Hello everyone, I'm Fir (find me on LinkedIn). In this article, I'll continue the investigation focusing on threat intelligence correlation and suspicious remote access activity.
In this lab, I analyzed IDS alerts and CTI data to identify potential misuse of remote access software linked to an APT group.
🧠 Hypothesis
Attackers could leverage legitimate remote access tools to maintain persistence and control compromised systems.
Step 1 : Threat Intelligence Identification
I started by identifying indicators associated with a known threat actor. Indicates known infrastructure linked to attacker activity.
APT Group: APT-BN42
Malicious IP : 23.11.98.133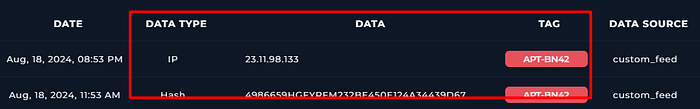
Step 2 : IDS Alert Analysis (Remote Access Activity)
Next, I analyzed IDS alerts related to remote access software (AnyDesk). Suggests external communication targeting an internal system using remote access tools
Destination IP : 172.16.5.16
Source IP : 19.68.100.23
Step 3 : Hash & Endpoint Correlation
I pivoted into CTI data to investigate malware indicators. Indicates suspicious process likely linked to unauthorized remote access or persistence mechanism.
Hash Value : 4986659HGFYRFM232BE450E124A34439D67
Affected system IP : 172.16.5.16
Process name : anyupdate.exe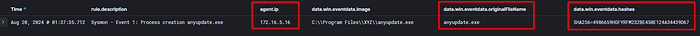
Conclusion
This investigation demonstrates how attackers can abuse legitimate remote access tools to maintain persistence and control over compromised systems. The activity was linked to APT-BN42, with indicators showing suspicious communication involving an internal system and external IP addresses. Further correlation revealed a malicious hash associated with the process anyupdate.exe, suggesting unauthorized or disguised remote access activity. This case highlights the importance of combining threat intelligence, IDS alerts, and endpoint visibility to detect threats that rely on legitimate tools rather than obvious malware.
Thanks for reading! If you're learning threat hunting or SOC analysis, feel free to share your thoughts in the comments 👋 What kind of attack scenario are you exploring next? 🔥

