1. Introduction
After working on OT labs such as HTB Alchemy, I wanted to deepen my understanding of industrial environments from both a theoretical and practical perspective.
To achieve this, I studied Industrial Network Security (2nd Edition) and started applying its concepts in a controlled lab environment.
This article reflects my journey toward understanding OT cybersecurity as a complete system from a penetration testing perspective.
2. Understanding Industrial Environments (Foundation)
One of the most important realizations early on is that OT is fundamentally different from IT.
In IT:
- Confidentiality
- Integrity
- Availability
In OT:
- Safety
- Operations
- Availability
In industrial environments, availability is often more critical than confidentiality.
3. Industrial Control Systems (ICS)
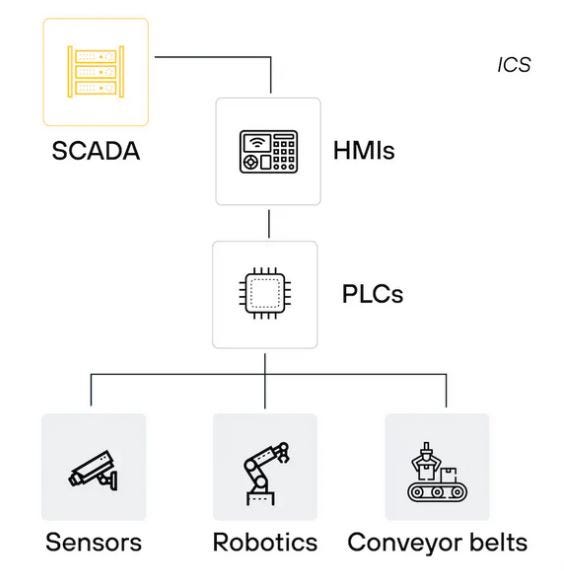
Industrial environments rely on:
- PLC (Programmable Logic Controllers) → executes control logic
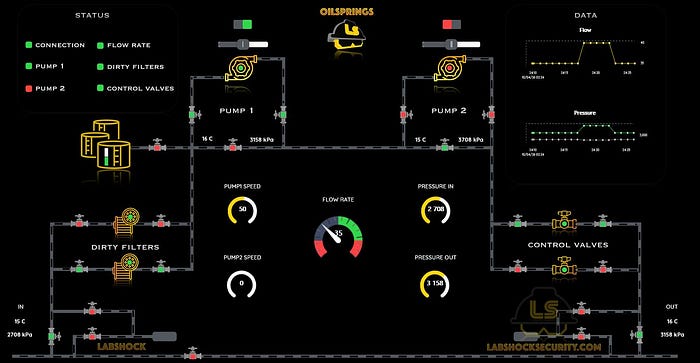
- HMI (Human Machine Interface) → operator interface
- SCADA (Supervisory Control and Data Acquisition) → monitoring and supervision
These systems control real-world variables such as temperature, pressure, and flow.

4. SCADA vs DCS
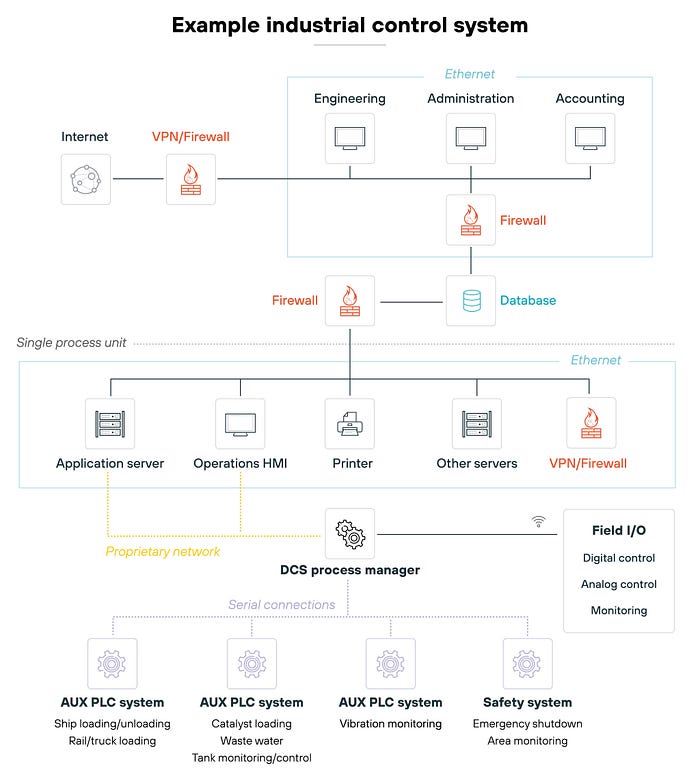
While studying ICS environments, I noticed that SCADA and DCS are often used interchangeably but they differ in architecture and use cases.

5. Control Loop
Industrial systems operate as a loop: Sensor → PLC → Actuator

The real target is the control process, not the device.
6. Understanding Communication (Protocols)
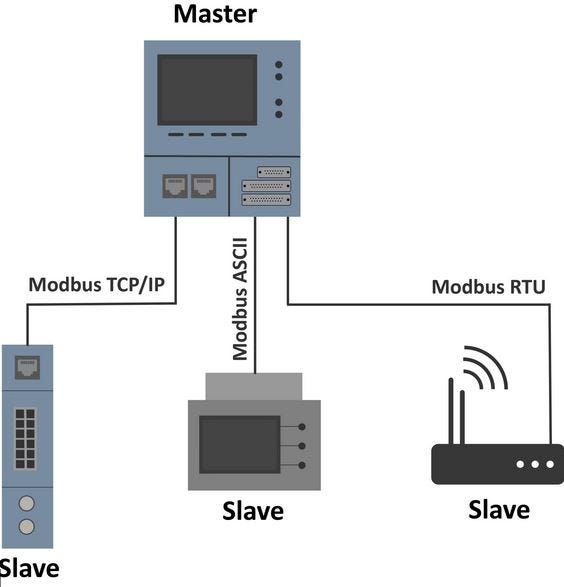
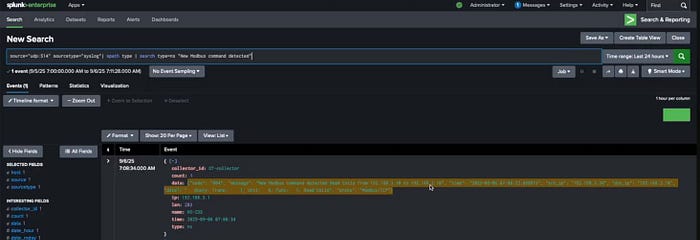
Industrial systems use specialized protocols such as Modbus.
- No encryption
- No authentication
- Plain-text communication
PenTester Perspective
- Traffic can be analyzed
- Commands can be understood
- Data can be manipulated
In many cases, network access = system access

7. Understanding the Attack Surface
Industrial environments face unique threats:
APT (Advanced Persistent Threat)
- Long-term, targeted attacks
Insider Threat
- Internal access = High impact
IT → OT Pivot
- One of the most realistic scenarios
The most dangerous attack path: IT Network → Pivot → OT Environment
Common Attack Techniques
- Man-in-the-Middle
- Replay attacks
- Denial of Service (DoS)
- HMI exploitation
- Engineering Workstation compromise
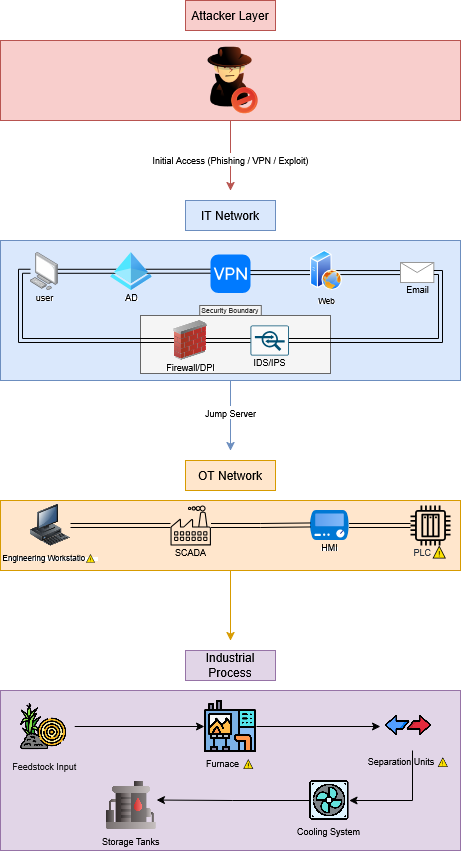
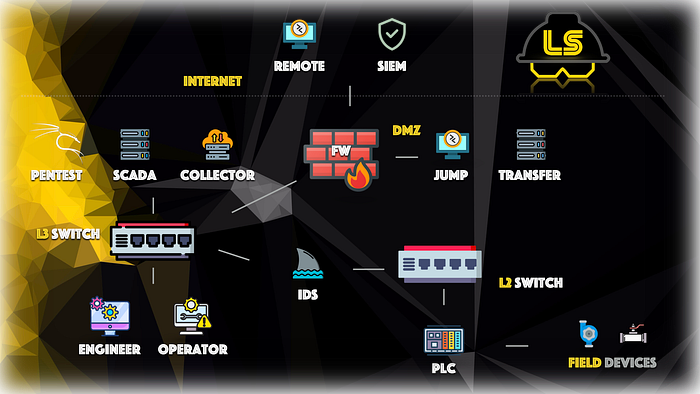
This diagram was designed to map real-world attack paths in industrial environments.
The most valuable target: Engineering Workstation
8. From Attacks to Full Security Architecture
At this stage, the perspective shifts: From how to attack → To how the entire system is secured
Risk and Vulnerability Assessment
Risk in OT is not about data it is about:
- Safety
- Availability
- Operations

High-impact systems must always be prioritized.
Zones and Conduits (Segmentation)
Industrial networks are divided into zones. Communication is controlled through conduits.
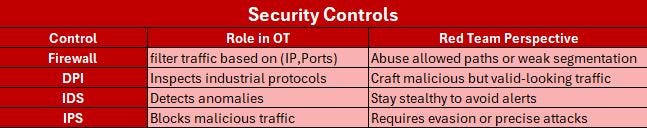
9. Security Controls in ICS
After understanding the architecture, I started analyzing how these systems are protected. Industrial environments rely heavily on network-based security controls.
10. Detection and Monitoring
Industrial systems rely on:
- Anomaly detection
- Behavior monitoring
- Logging
Final Thought
This journey is about understanding how industrial systems operate, how they are attacked, and how they are secured as a whole. In industrial environments, cybersecurity is directly tied to production continuity, operational safety, and financial impact making OT security a critical business requirement.
In a follow-up article, I will be exploring a practical OT scenario, applying these concepts in a controlled lab environment to demonstrate how industrial systems can be analyzed and interacted with.
I am actively developing my expertise in OT cybersecurity, focusing on real-world industrial environments, and I am open to opportunities, collaboration, and discussions in this field.
🔗 X(Twitter): @levi_cys 🔗 Linkedin: Murtadha Al Abbas

