If you've started learning cybersecurity, you've probably come across the term OSI Model. At first glance, it might seem like a theoretical concept you only need to memorize for exams. But in reality, the OSI Model is one of the most practical tools for understanding how cyberattacks happen and how defenses work.
Instead of seeing it as a list of layers, think of the OSI Model as a map of how data travels across a network. Once you understand this map, cybersecurity concepts become much clearer and more logical.
What Is the OSI Model?
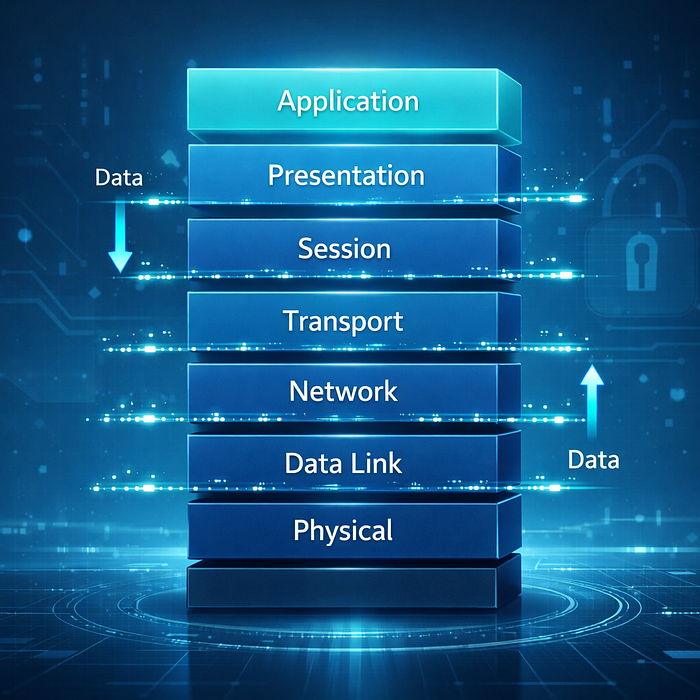
The OSI (Open Systems Interconnection) Model is a framework that divides network communication into seven layers. Each layer has a specific role in how data moves from one device to another.
These layers help professionals understand where problems occur, how attacks are carried out, and how security measures can be applied effectively.
The seven layers are:
- Physical
- Data Link
- Network
- Transport
- Session
- Presentation
- Application
At first, this may look complex. But when broken down simply, each layer represents a step in the journey of data.
A Simple Way to Understand the OSI Model
Imagine sending a message to a friend.
- You write the message (Application Layer)
- It gets formatted properly (Presentation Layer)
- A connection is established (Session Layer)
- The message is broken into pieces (Transport Layer)
- It is routed to the correct destination (Network Layer)
- It travels across local connections (Data Link Layer)
- Finally, it is transmitted physically (Physical Layer)
Each layer works together to ensure the message reaches its destination accurately.
Why the OSI Model Matters in Cybersecurity
Cybersecurity is not just about blocking attacks. It's about understanding where and how attacks happen.
The OSI Model helps professionals:
- identify which layer is being targeted
- apply the right security controls
- troubleshoot network issues
- analyze cyberattacks more effectively
Instead of guessing, the OSI Model provides structure and clarity.
Security Risks at Each Layer
Every layer in the OSI Model can be a target for attackers. Understanding these risks helps build stronger defenses.
Physical Layer
This layer involves hardware and physical connections. Risks: device theft, cable tampering
Data Link Layer
Handles communication within the same network. Risks: MAC spoofing, network sniffing
Network Layer
Responsible for routing data using IP addresses. Risks: IP spoofing, routing attacks
Transport Layer
Ensures reliable data transfer. Risks: port scanning, denial-of-service attacks
Session Layer
Manages communication sessions. Risks: session hijacking
Presentation Layer
Handles data formatting and encryption. Risks: weak encryption methods
Application Layer
Where users interact with services like websites and email. Risks: phishing, SQL injection, malware
By mapping threats to layers, cybersecurity professionals can respond more precisely.
How Security Tools Relate to the OSI Model
Many cybersecurity tools operate at specific layers.
For example:
- Firewalls often work at the Network and Transport layers
- Encryption operates at the Presentation layer
- Antivirus and web security tools function at the Application layer
Understanding this relationship helps professionals choose the right tools for the right problems.
OSI Model in Real-World Cybersecurity Roles
The OSI Model is used daily across different cybersecurity roles.
A SOC analyst might use it to identify where suspicious traffic originates.
An incident responder might analyze which layer was exploited during an attack.
A penetration tester might target specific layers to find vulnerabilities.
It's not just theory. It's a practical framework used in real-world scenarios.
Common Mistake: Memorizing Without Understanding
Many beginners try to memorize the OSI layers without understanding their purpose. This often leads to confusion later.
Instead of memorizing, focus on understanding:
- what each layer does
- how data flows through them
- where attacks can occur
Once you understand the logic, remembering the layers becomes much easier.
Final Thoughts
The OSI Model is more than a technical concept. It is a powerful way to understand how networks function and how cybersecurity defenses are built.
When you see cybersecurity through the lens of these layers, complex topics become simpler. Attacks become easier to analyze. Solutions become more structured.
If you're serious about learning cybersecurity, mastering the OSI Model is one of the smartest steps you can take.
OSI model explained, OSI model cybersecurity, network layers security, OSI layers functions, cybersecurity networking basics, OSI model for beginners