Overview
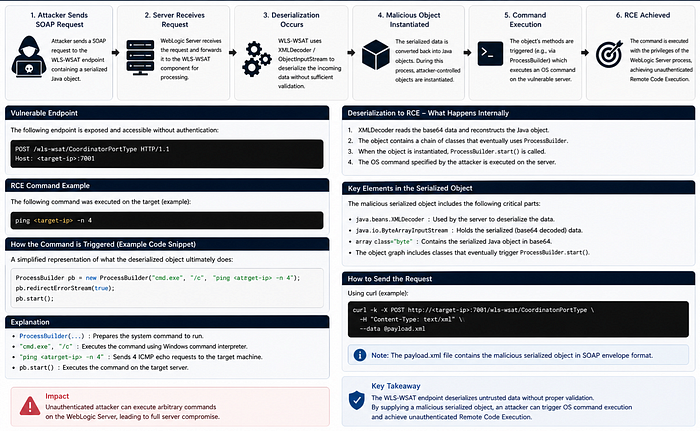
While testing a target running Oracle WebLogic Server, I identified an exposed WLS-WSAT endpoint that allowed unauthenticated interaction. Further analysis showed that this endpoint was vulnerable to a deserialization issue (CVE-2019–2725), which could be leveraged to achieve remote code execution.
The issue was validated by crafting a SOAP request and confirming controlled command execution on the server.
A custom validation approach was used to safely confirm the exploitability.
Discovery
During enumeration, the target was identified as running Oracle WebLogic Server 10.3.5.0 and the following endpoint was identified:
/wls-wsat/CoordinatorPortType
This endpoint was accessible without authentication and accepted SOAP-based requests, making it a viable attack surface.
Root Cause
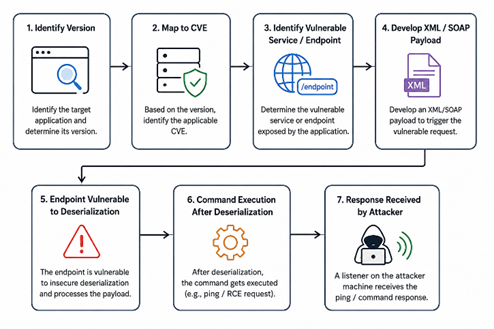
The vulnerability exists due to insecure handling of serialized objects within the WLS-WSAT component.
- The endpoint processes SOAP requests containing serialized Java objects.
- These objects are deserialized without sufficient validation.
- This allows attacker-controlled data to be interpreted and executed.
By abusing this behaviour, it is possible to trigger arbitrary command execution on the underlying system.
Serialization is the process of converting an in-memory object into a format suitable for storage or transmission.
Deserialization is the process of reconstructing the serialized data back into an executable object in memory.
The presence of java.beans.XMLDecoder indicated that XML input was being reconstructed into Java objects without sufficient validation. Unsafe object reconstruction can allow execution of attacker-controlled logic during deserialization.
Remote Code Execution (RCE) refers to the ability of an attacker to execute system-level commands remotely on a vulnerable server.
To validate the issue safely, a controlled SOAP/XML payload was crafted to invoke Java ProcessBuilder execution using a non-destructive ping command.
Background
Oracle WebLogic Server is an enterprise middleware and Java application server used to deploy and manage enterprise applications, SOAP/REST services, transaction handling, and backend integrations. It is an application server middleware component.
WLS-WSAT is a component of Oracle WebLogic Server (WLS — WebLogic Server, WS-AT — Web Services Atomic Transaction). It is a SOAP-based protocol used to support distributed transaction coordination between enterprise systems and services.
The /wls-wsat/CoordinatorPortType endpoint is used to process WS-AtomicTransaction requests between enterprise systems. In many environments, this service is exposed internally or externally depending on deployment configuration.
Exploitation Approach
A custom SOAP payload was crafted to:
- Interact with the exposed endpoint.
- Embed a malicious serialized object.
- Trigger execution via Java runtime mechanisms.
Validation
To safely confirm impact, a controlled command execution was performed.
A SOAP request was sent using curl, embedding a command to initiate an ICMP request (ping) from the target server to a controlled system.
Observed behaviour:
- The server initiated outbound ICMP traffic.
- This confirmed successful remote code execution.
This approach ensured validation without modifying system state or affecting availability.
Impact
Successful exploitation allows:
- Unauthenticated remote code execution
- Full compromise of the WebLogic server
- Data theft: Access to sensitive data and configurations
- Potential lateral movement within the internal network
- Application/server takeover and compromise of backend systems.
- Lead to ransomware deployment.
Due to the lack of authentication and the ability to achieve remote code execution, the issue is classified as Critical severity.
Remediation
- Apply Oracle security patches.
- Upgrade to supported WebLogic version.
- Restrict access to WLS-WSAT endpoints.
- Disable unused SOAP services.
- Use network segmentation/WAF rules.
- Monitor suspicious SOAP/XML requests.
Note: This write-up is shared for educational and knowledge-sharing purposes only.
