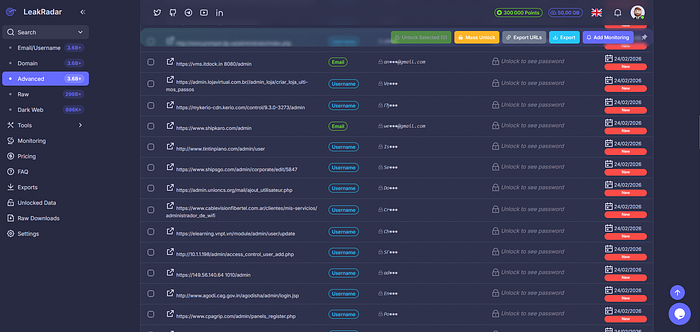
Here is what showed up.
The obvious stuff
Main app login. Corporate email. Expected.
Then it got interesting
vpn.company.com — remote access portal jira.internal.company.com — project management gitlab.company.com — source code admin.company.com/dashboard — backend panel staging.company.com — pre-production environment hr.internal.company.com — employee portal
None of these appeared in subdomain scans. No recon tool found them.
Why stealer logs reveal what scans miss
Employees log into these tools daily. They save passwords in browsers. Their machines get infected. Stealers capture the exact URLs.
Internal tools that are not indexed anywhere else. Subdomains with random strings. Paths behind authentication.
All sitting in LeakRadar results.
The credentials were still valid
Fresh timestamps. Some from last week. The company had no idea these were exposed.
One search gave me more internal reconnaissance than hours of active scanning would.
The takeaway
Your internal infrastructure is probably mapped in stealer logs already. The question is whether you find it first.