In penetration testing, the reconnaissance phase is where security professionals quietly collect information about a target before attempting any attack. Surprisingly, experienced penetration testers often spend more time gathering information than actually exploiting vulnerabilities.
For cybersecurity students, understanding this phase is crucial because every successful security assessment starts with good reconnaissance.
Let's explore how it works.
The Big Picture: Penetration Testing Methodology
Penetration testing is not random hacking. It follows a structured process designed to evaluate how secure a system really is.
What is Information Gathering?
Information gathering (also called reconnaissance) is the process of collecting publicly available or technical information about a target system or organization.
The goal is simple:
Understand the target before interacting with it.
During this phase, security professionals try to answer questions such as:
- What domains belong to the organization?
- Which servers are publicly accessible?
- What technologies are being used?
- Who works at the company?
- What services are exposed to the internet?
All of this information helps identify potential entry points into the system, also known as the attack surface.
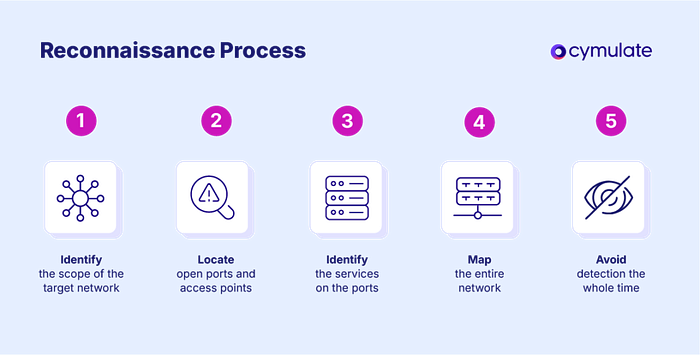
Steps in Information Gathering
Information gathering usually follows several structured steps.
1. Identifying the Target
The first step is defining the scope of the target.
This might include:
- domain names, IP addresses, network ranges, cloud services, web applications
For example:
company.com
portal.company.com
vpn.companyEach system could potentially expose different vulnerabilities.
2. DNS and Domain Enumeration
DNS records can reveal valuable information about infrastructure.
Important DNS records include:
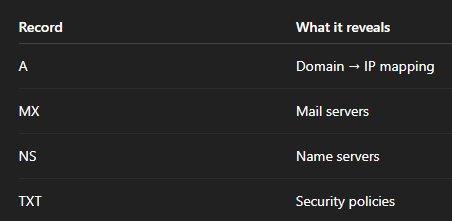
Using simple commands like:
dig company.comsecurity testers can uncover hidden infrastructure details.
3. Discovering Subdomains
Organizations rarely operate on a single domain. They often have multiple subdomains such as:
dev.company.com
api.company.com
mail.company.com
test.company.comThese environments sometimes have weaker security controls because they are used for development or testing. For attackers, these can become easy entry points.
4. Network Discovery
Once domains and systems are identified, the next step is discovering live hosts and services. One of the most widely used tools for this purpose is Nmap.
Example command:
nmap -sV target.comThis scan can reveal:
- open ports
- running services
- software versions
These details help testers identify outdated or vulnerable software.
Passive vs Active Reconnaissance
Information gathering is typically divided into two main approaches.
Passive Reconnaissance
Passive reconnaissance involves collecting information without directly interacting with the target system.
Because there is no direct contact with the system, these techniques are very difficult to detect.
Examples include:
- searching public websites
- analyzing social media
- reviewing company documents
- using OSINT tools
A common technique used by security researchers is Google Dorking.
Example:
site:company.com filetype:pdfThis may reveal internal reports, documents, or configuration files that were never meant to be publicly visible.
Passive reconnaissance is essentially digital investigation using publicly available information.
Active Reconnaissance
Active reconnaissance involves directly interacting with the target system.
Examples include:
- port scanning
- service enumeration
- vulnerability scanning
For example:
nmap -sS target.comWhile this approach provides accurate technical data, it can also trigger alerts in:
- Intrusion Detection Systems (IDS)
- Security monitoring tools
- SIEM platforms
Because of this, penetration testers must carefully follow legal scope and authorization before performing active reconnaissance.
What Kind of Information Can Be Collected?
During reconnaissance, attackers and security professionals collect a wide range of information.
Organizational Intelligence
Information about employees can be surprisingly valuable.
Examples include:
- employee names
- email formats
- internal departments
Example email pattern:
firstname.lastname@company.comThis information can later be used in phishing or password attacks.
Network Infrastructure
Reconnaissance may reveal:
- IP ranges
- DNS servers
- VPN gateways
- exposed services
Understanding network architecture helps map the organization's external attack surface.
Technical Stack
Identifying technologies used by a website can reveal potential vulnerabilities.
Examples include:
- Apache or Nginx web servers
- WordPress or Drupal CMS
- PHP, Python, or Node.js frameworks
Older software versions may contain known security flaws.
Tools Used for Information Gathering
Cybersecurity professionals rely on several tools during reconnaissance. Some of the most commonly used include:
Nmap A powerful network scanning tool used to identify hosts, open ports, and services.
theHarvester Collects emails, domains, and employee information from public sources.
Maltego Visualizes relationships between domains, people, organizations, and infrastructure.
Recon-ng A reconnaissance framework that automates OSINT collection.
Shodan A search engine that finds internet-connected devices such as servers, routers, and IoT devices.
These tools allow security professionals to map the digital footprint of an organization.
Why Information Gathering Matters
The reconnaissance phase determines how effective a penetration test will be.
Without proper information:
- vulnerabilities may be overlooked
- attacks may fail
- detection risk increases
In other words, reconnaissance turns guessing into strategy.
The more intelligence you gather about a system, the easier it becomes to identify weaknesses.
Final Thoughts
For cybersecurity students, learning reconnaissance techniques is essential.
It teaches how to:
- think like an attacker
- analyze system infrastructure
- understand attack surfaces
- identify security weaknesses
But most importantly, it shows that cybersecurity is not just about hacking tools. It is about understanding systems before interacting with them. And that process always begins with one critical step:
Information gathering.