Introduction
Password security relies on one-way cryptographic functions. When a system stores passwords in plain text, it creates a massive security risk. Instead, systems should store hashes. This lab simulates a scenario where an analyst must recover original passwords from different hash types. The objective involves identifying the algorithm and applying the correct recovery method.
Reconnaissance
The process begins with data collection. In this stage, the analyst gathers all provided hash strings. Physical characteristics like string length and character set (hexadecimal, base64) provide the first clues about the underlying algorithm.
Enumeration
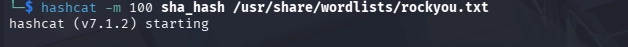
Enumeration involves specific identification. Tools like hash-identifier or hashid analyze the strings. These tools compare the hash format against a database of known signatures.
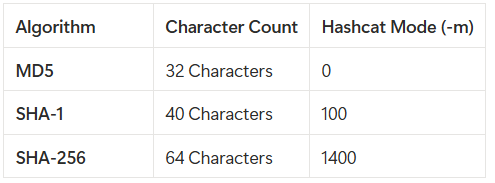
MD5: 32-character hexadecimal string.
SHA-1: 40-character hexadecimal string.
Bcrypt: Starts with $2a$ or $2y$.
Exploitation
The exploitation phase recovers the original password by comparing the target hash against generated hashes. This process uses two main methods: Online Lookups and Offline Cracking. Online Lookups check pre-computed databases for a match. Offline Cracking uses local hardware to hash words from a list until a match occurs.
Post-Exploitation
Once the plaintext password is clear, the analyst documents the result. In a real-world test, this password would grant access to protected services or administrative panels.
Tools Used
Hash-Identifier: A python script to detect different hash types.
John the Ripper: A versatile offline password cracker.
Hashcat: A GPU-accelerated tool for high-speed cracking.
Rockyou.txt: A standard wordlist containing millions of common passwords.
Task 1
Answer the questions below
Question 1
The first step in the cryptographic analysis is to identify the algorithm used to generate the hash. The target string is:
48bb6e862e54f2a795ffc4e541caed4d

We determine the hash type, the Hash-Identifier tool was utilized. As shown in the image, the tool analyzes the structure and character length of the string. The output provides the following results:
Primary Match: MD5 (Message Digest Algorithm 5)
Secondary Possibility: Domain Cached Credentials(MD4)
The 32-character hexadecimal format strongly suggests the MD5 algorithm. While the tool lists other "Least Possible" types like NTLM or MD4, the primary result serves as the starting point for the cracking process. Identifying the hash correctly is vital because it determines which parameters will be used in tools like John the Ripper or Hashcat.
Hash Cracking with Hashcat
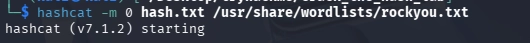
-m 0: This flag specifies the hash type. In Hashcat, the code 0 represents the MD5 algorithm.
hash.txt: This file contains the target hash string identified in the previous step.
/usr/share/wordlists/rockyou.txt: This is a widely used wordlist in cybersecurity that contains millions of common passwords.
The process utilizes a dictionary attack methodology. Hashcat hashes each word from the rockyou.txt list using the MD5 algorithm and compares it to the target hash. If the two hashes match, the tool successfully recovers the original password. This approach is significantly faster than a pure brute-force attack because it relies on human-generated password patterns.
The Hashcat execution concluded successfully. As shown in the image, the tool matched the target hash against the wordlist and recovered the plaintext password.
Recovered Credentials:
Target Hash: 48bb6e862e54f2a795ffc4e541caed4d
Plaintext Password: easy
Status: Cracked
The output confirms the efficiency of the dictionary attack. The "Status: Cracked" indicator signifies that the cryptographic challenge for this task is complete. The identification of the hash as MD5 was correct, allowing the tool to operate under Mode 0. This result proves that simple, non-salted passwords even when hashed provide minimal security against modern recovery techniques.
Correct Answer: Easy
Question 2
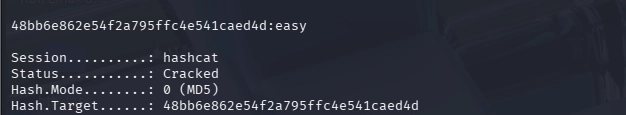
The target string is:
CBFDAC6008F9CAB4083784CBD1874F76618D2A97
The Hash-Identifier tool analyzed the string and returned SHA-1 as the primary match. Unlike the previous MD5 hash, this string contains 40 characters. This increase in length corresponds to the SHA-1 (Secure Hash Algorithm 1) standard.
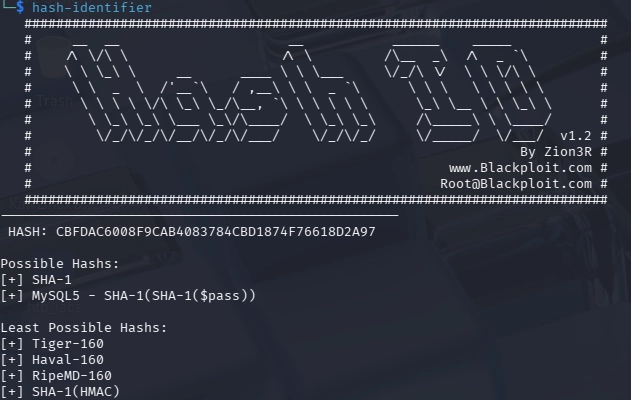
Let's crack this hash, Hashcat requires a specific mode. According to the reference table provided in the lab documentation, SHA-1 corresponds to Mode 100. The following command was executed to initiate the dictionary attack:
hashcat -m 100 sha_hash /usr/share/wordlists/rockyou.txt
The attack was successful. Hashcat recovered the plaintext password by matching the SHA-1 signature against the rockyou.txt wordlist.
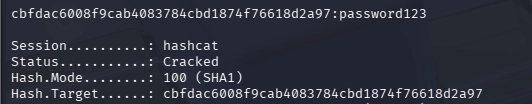
Identified Type: SHA-1 (Mode 100)
Recovered Password: password123
Status: Cracked
This systematic approach ensures that the correct cracking parameters are applied based on the hash's physical properties. The recovery of password123 further demonstrates that even slightly longer passwords remain vulnerable if they are common enough to exist in standard wordlists.
Correct Answer: password123
Question 3
The target hash string provided was:
1C8BFE8F801D79745C4631D09FFF36C82AA37FC4CCE4FC946683D7B336B63032
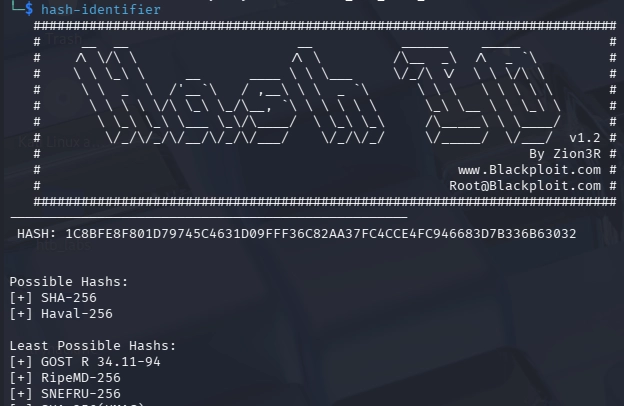
We determine the underlying cryptographic algorithm, the hash-identifier tool was utilized. The analysis confirmed that the string matches the SHA-256 hashing standard.
Following the identification, the Hashcat utility was employed for the password recovery process. A dictionary attack was performed by comparing the hash against the widely recognized rockyou.txt wordlist.
Attack Mode: Dictionary Attack
Hash Mode (-m 1400): SHA-256
Wordlist: /usr/share/wordlists/rockyou.txt
The command executed was:
hashcat -m 1400 sha256_hash.txt /usr/share/wordlists/rockyou.txt
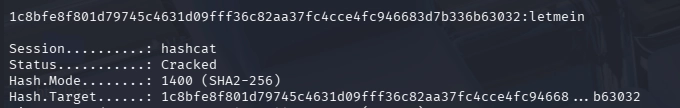
The decryption process successfully matched the target hash against a entry in the provided wordlist. The status was confirmed as "Cracked," and the original plaintext password was recovered.
Target Hash: 1c8bfe8f801d79745c4631d09fff36c82aa37fc4cce4fc946683d7b336b63032
Recovered Plaintext: letmein
Correct Answer: letmein
Question 4
The target hash string provided was:
$2y$12$Dwt1BZj6pcyc3Dy1FWZ5ieeUznr71EeNkJkUlypTsgbX1H68wsRom
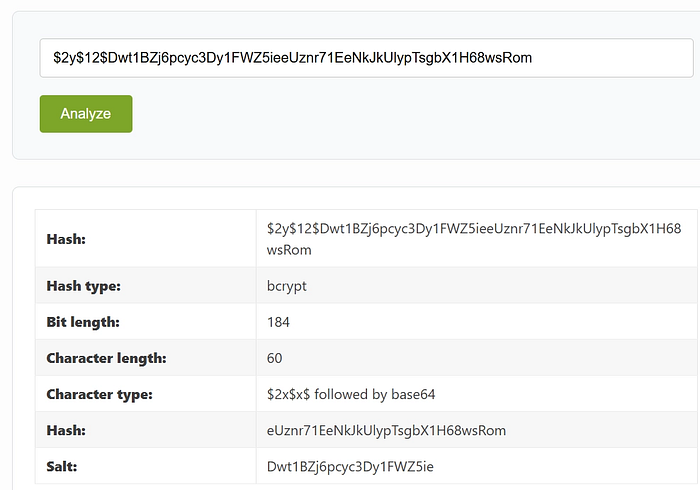
We used hash identification tools and structural analysis, the following components were identified:
Hash Type: bcrypt (based on the $2y$ prefix).
Cost Factor: 12 (indicating $2^{12}$ iterations, making it computationally expensive).
Salt: Dwt1BZj6pcyc3Dy1FWZ5ie (extracted from the encoded string).
Hash Length: 60 characters.
Two different industry-standard tools were prepared for the cracking process to ensure reliability:
Hashcat: The hash was targeted using the specific mode for bcrypt.

hashcat -m 3200 bcrypt_hash.txt /usr/share/wordlists/rockyou.txt
John the Ripper: As an alternative, John was utilized with its auto-detection capability for bcrypt formats.
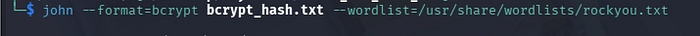
john --format=bcrypt bcrypt_hash.txt --wordlist=/usr/share/wordlists/rockyou.txt

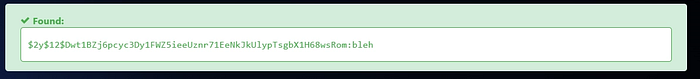
This task highlights the importance of the Bcrypt algorithm in modern security. Unlike simple hashes, bcrypt incorporates a "cost factor" and an integrated "salt," which significantly increases the time required for an attacker to crack passwords, even when using high-performance hardware. The successful recovery of the password bleh again confirms that even strong algorithms cannot protect weak, dictionary-based passwords.
Correct Answer: bleh
Question 5
The target hash string provided was:
279412f945939ba78ce0758d3fd83daa

The string was analyzed using the hash-identifier tool. While the tool initially suggested MD5 as a primary possibility due to the 128-bit (32-character) length, further analysis and verification through multi-algorithm lookup tools confirmed the hash to be MD4.
Algorithm: MD4
Hash Length: 32 Hexadecimal characters (128-bit)
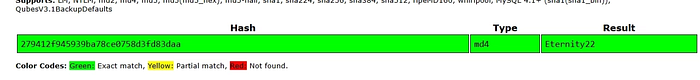
The search returned an "Exact match" (Green status), confirming that this specific hash had been previously computed and stored in common security databases.

The recovery process was near-instantaneous due to the algorithmic weaknesses of MD4 and the simplicity of the original string.
Target Hash: 279412f945939ba78ce0758d3fd83daa
Recovered Plaintext: Eternity22
This task highlights the critical vulnerabilities associated with MD4. Originally designed in 1990, MD4 is now considered cryptographically broken and highly susceptible to collision attacks and rapid cracking. In modern environments, MD4 is largely deprecated (except for legacy protocols like NTLM). The ease with which Eternity22 was recovered underscores why organizations must transition to more robust algorithms like SHA-256 or Argon2 to protect sensitive data.
Correct Answer:Eternity22
Task 2:
This task increases the difficulty. All of the answers will be in the classic rock you(opens in new tab) password list.
You might have to start using hashcat here and not online tools. It might also be handy to look at some example hashes on hashcats page(opens in new tab).
Answer the questions below
Question 1
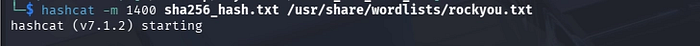
The target hash provided for analysis was: F09EDCB1FCEFC6DFB23DC3505A882655FF77375ED8AA2D1C13F640FCCC2D0C85
We confirm the algorithm, both hashid and hash-identifier utilities were used.

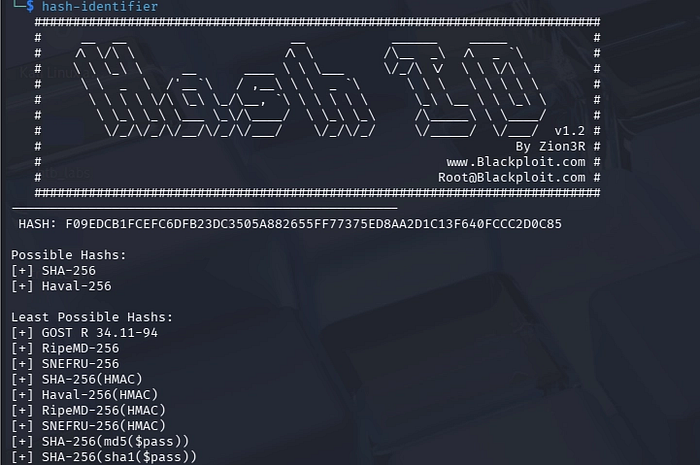
The tools identified several possibilities, but based on the bit-length and common security practices, SHA-256 was selected as the primary target for the attack.
Algorithm identified: SHA-256
Hash Status: Non-salted, standard hex representation.
The recovery process was conducted using Hashcat on a Linux-based environment. A dictionary attack was performed using the standard rockyou.txt wordlist, which contains millions of known passwords.

The recovery process was conducted using Hashcat on a Linux-based environment. A dictionary attack was performed using the standard rockyou.txt wordlist, which contains millions of known passwords.
Tool: Hashcat
Hash Mode: 1400 (Standard SHA-256)
Wordlist Path: /usr/share/wordlists/rockyou.txt
Command Executed: hashcat -m 1400 hashF09.txt /usr/share/wordlists/rockyou.txt
The Hashcat session completed successfully with the status "Cracked." The tool matched the input hash against the wordlist in a very short duration, revealing the original plaintext.
Target Hash: f09edcb1fcefc6dfb23dc3505a882655ff77375ed8aa2d1c13f640fccc2d0c85
Recovered Plaintext: paule
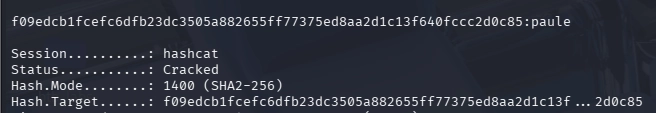
We used some different sources to verify the hash result.
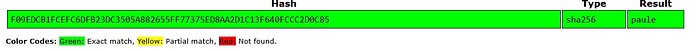
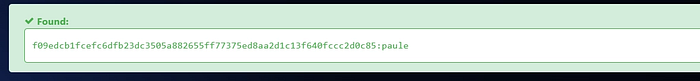
Correct Answer: Paule
Question 2
The target hash provided for analysis was:
1DFECA0C002AE40B8619ECF94819CC1B
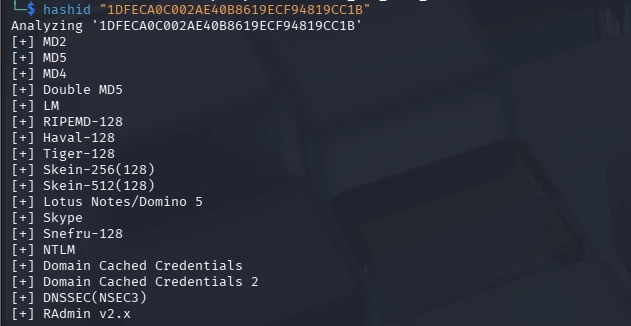
Tools Utilized: hash-identifier and hashid.
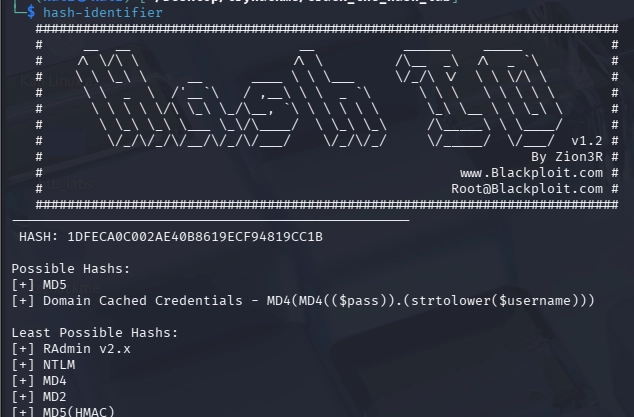
Preliminary analysis suggested several possibilities, including MD5, NTLM, and Domain Cached Credentials. These tools provide a probability-based assessment of the hash structure.
Once the hash was identified as having NTLM characteristics, a dictionary-based attack was formulated using hashcat.
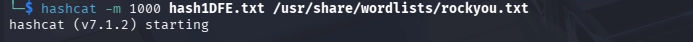
Attack Method: Dictionary Attack.
Wordlist: rockyou.txt (a standard, high-entropy wordlist).
Command: bash hashcat -m 1000 hash1DFE.txt /usr/share/wordlists/rockyou.txt
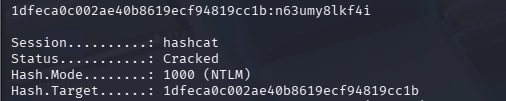
The `-m 1000` flag specifies that the target hash is an NTLM format
The execution of the attack successfully identified the plaintext password within the wordlist.
Status: Cracked.
Hash Mode: 1000 (NTLM).
Recovered Plaintext: n63umy8lkf4i.
Verification: The crack was verified using both the local hashcat output and validated against online hash analysis databases, which returned an exact match.

The hash was submitted to an online lookup service which returned an "Exact Match" (indicated by the green color code). This confirms that the hash is indeed NTLM and the corresponding plaintext is n63umy8lkf4i
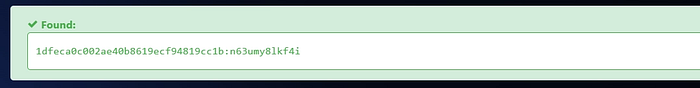
A second independent database was used to verify the results. As shown in the "Found" status, the output remains consistent, providing high confidence in the data integrity of the recovery process.
The hash was verified using reputable online hash repositories such as CrackStation and Hashes.com to ensure the result's consistency across multiple independent databases.
Correct Answer: n63umy8lkf4i
Question 3
The target hash provided for analysis was:
$6$aReallyHardSalt$6WKUTqzq.UQQmrm0p/T7MPpMbGNnzXPMAXi4bJMl9be.cfi3/qxIf.hsGpS41BqMhSrHVXgMpdjS6xeKZAs02.
Salt: aReallyHardSalt
- Algorithm Identification: Based on the prefix
$6$, the hash was identified as SHA-512 (Unix), also known assha512crypt. This is a much more secure and computationally expensive algorithm compared to NTLM or MD5.
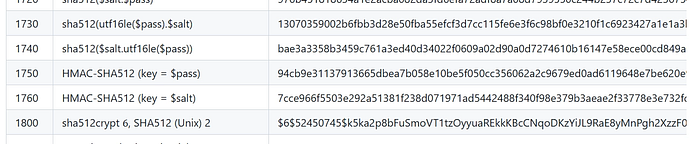
Salt Analysis - The hash explicitly contains a salt value: aReallyHardSalt. Salting is a security measure used to prevent rainbow table attacks.
Referencing the Hashcat mode table, the correct mode for this specific format is identified as 1800 (sha512crypt $6$, SHA512 (Unix)).
Given the complexity of SHA-512, a high-performance cracking tool was required.
Tool: Hashcat
Command Execution
hashcat -a 0 -m 1800 hash6.txt /usr/share/wordlists/rockyou.txt — force

-a 0: Straight attack mode (dictionary).
-m 1800: Specific mode for SHA-512 Unix hashes.
--force: Used to bypass potential hardware warning triggers during the intensive computation process

The hash was successfully cross-referenced with online decryption databases to verify the result.
Recovered Plaintext: waka99
The combination of a strong salt and the SHA-512 algorithm makes this password significantly harder to crack than standard hashes; however, it was successfully recovered using a comprehensive wordlist.
Correct Answer: waka99
Question 4
The target hash provided for analysis was:
Hash: e5d8870e5bdd26602cab8dbe07a942c8669e56d6
Salt: tryhackme
Preliminary analysis indicated the hash structure conforms to SHA1 (or SHA-128), characterized by a 160-bit length and a 40-character hexadecimal string.
Further lab investigation revealed that this is not a standard SHA1 hash, but an HMAC-SHA1 hash, which utilizes a salt (in this case, the string tryhackme) as a key to enhance security.
Unlike standard algorithms, HMAC-SHA1 requires specifying the hash mode that correlates to the specific keyed structure.
Tool: Hashcat (v7.1.2)
Command Execution:
hashcat -m 160 hash_salt.txt /usr/share/wordlists/rockyou.txt

-m 160: This mode specifically targets HMAC-SHA1, treating the provided input as a keyed hash where the salt acts as the secret key.

Status (Image 3): The attack was successful, as confirmed by the hashcat "Cracked" status.
Target: e5d8870e5bdd26602cab8dbe07a942c8669e56d6:tryhackme
Recovered Plaintext: 481616481616
By correctly identifying the hash as an HMAC-SHA1 structure, we were able to successfully bypass the keyed protection using dictionary-based recovery.
Correct Answer: 481616481616
Thank you for taking the time to read this report. If you have any questions or require further clarification regarding the methodologies or tools used in this lab, please feel free to reach out.

