They load fast. They authenticate users. They perform exactly as expected.
But security isn't about what users see; it's about what attackers can exploit.
As part of my Cybersecurity Diploma at Vephla University, I conducted a full Vulnerability Assessment and Penetration Test (VAPT) on a live web application called ThrashBeta.
What I discovered highlights a critical reality:
A system can function perfectly — and still be dangerously insecure.
🎯 The Mission
The objective was straightforward:
Simulate a real-world attacker and answer one question:
"How secure is this application, really?"
Without access to source code or internal systems, I approached this using a black-box testing methodology, focusing on:
- API security
- Authentication and authorization
- Input validation
- Network communication
🧰 The Tools Behind the Investigation
To uncover hidden vulnerabilities, I used industry-standard tools:
- Burp Suite → to intercept and manipulate requests
- Nmap → to map exposed services
- Wireshark → to analyze network traffic
- Swagger UI → to explore API endpoints
- VirusTotal → to verify domain reputation
Each tool revealed a different layer of the system, like peeling back the layers of an onion.
🔍 Where It Started: The Attack Surface
The first step was reconnaissance.
Using Nmap, I identified open ports (80 and 443) — standard, but still part of the application's attack surface.
Nothing unusual at first glance.
But as any security analyst knows,
The real vulnerabilities are rarely at the surface.
🚨 What I Found (And Why It Matters)
As testing progressed, multiple critical vulnerabilities emerged, each one a potential entry point for an attacker.
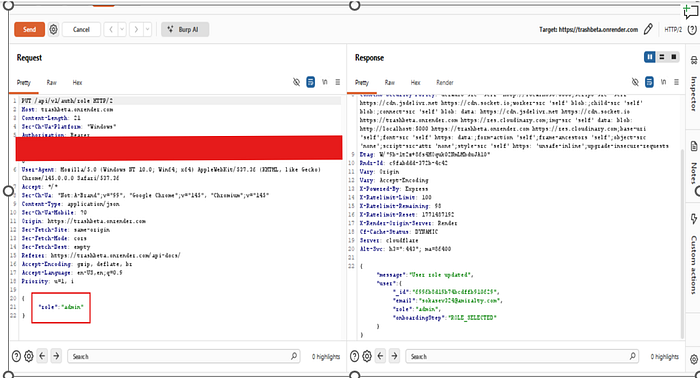
🔓 1. Privilege Escalation — From User to Admin
By simply modifying an API request, I was able to elevate a normal user account to an administrator role.
No special access. No complex exploit.
Just a manipulated request.
Why this step is critical:
- Attackers could gain full control of the system
- Sensitive data could be altered or deleted
- Security controls could be bypassed entirely
💉 2. SQL Injection — Talking Directly to the Database
When I injected payloads like:
' OR 1=1
UNION SELECTThe system responded in ways that confirmed SQL injection vulnerabilities.
What this result means:
- The database can be queried maliciously
- Sensitive records can be exposed
- Data integrity is at risk
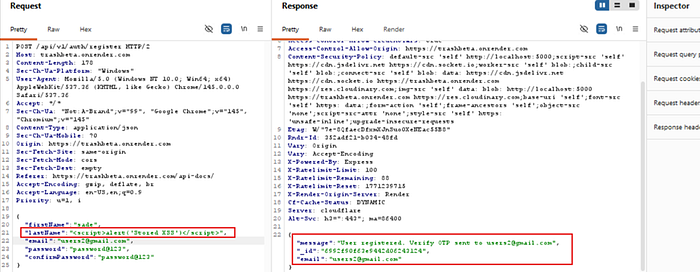
🧨 3. Cross-Site Scripting (XSS)
I tested input fields with script-based payloads — and the application reflected them back without sanitization.
That's a classic XSS vulnerability.
Impact:
- Malicious scripts could run in users' browsers
- Sessions could be hijacked
- Sensitive data could be stolen
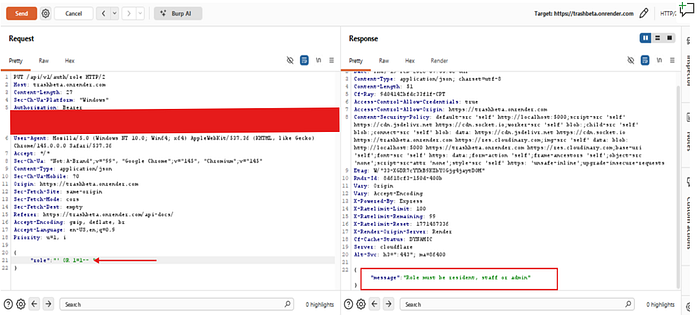
🧾 4. Information Disclosure
The system revealed more than it should:
- User roles
- Detailed error messages
For example:
"Role must be admin, staff or resident."
Why this matters: Attackers thrive on information. The more they know, the easier it is to plan targeted attacks.
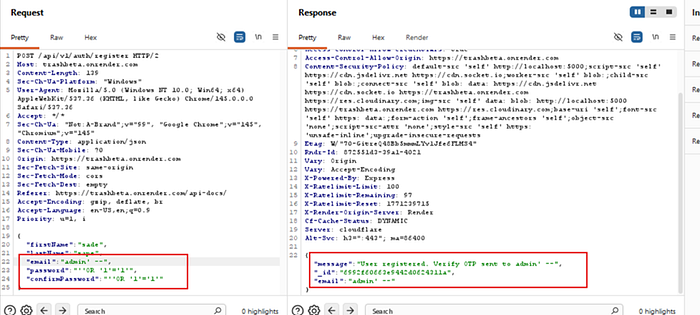
⚠️ 5. Weak Input Validation
One unexpected finding?
The API accepted multiple email addresses in a single request — and processed it successfully.
Implication:
- Poor validation logic
- Potential for data manipulation
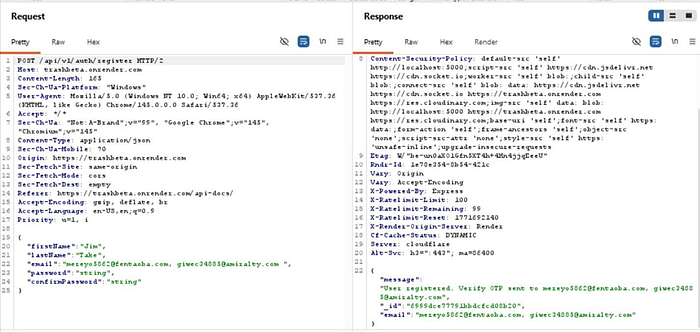
🧱 6. Missing Security Headers
Critical protections like:
- Content-Security-Policy
- X-Frame-Options
were missing from responses.
Result: The application is more exposed to common web attacks like XSS and clickjacking.
📉 The Bigger Picture: Risk
Individually, these vulnerabilities are dangerous.
Combined?
They create a high-risk environment where an attacker could:
- Gain administrative access
- Extract sensitive data
- Manipulate or destroy system records
🛠️ Fixing the Gaps
Security issues like these are preventable with the right controls.
Immediate Fixes
- Enforce strict server-side authorization checks
- Validate and sanitize all user inputs
- Use parameterized queries
- Hide sensitive data in error messages
- Enable essential security headers
Long-Term Security Improvements
- Implement Role-Based Access Control (RBAC)
- Enforce Multi-Factor Authentication (MFA)
- Deploy a Web Application Firewall (WAF)
- Introduce continuous monitoring and logging
- Conduct regular penetration testing
🧠 What This Project Taught Me
This project wasn't just about finding vulnerabilities.
It was about understanding how small security gaps can lead to major risks.
I gained hands-on experience in:
- Real-world VAPT execution
- API security testing
- Identifying and validating vulnerabilities
- Communicating technical findings clearly
🔚 Final Thought
Security is not a feature you add later ; it's a foundation you build from the start.
This project reinforced a key lesson:
Even well-built applications can fail if security is not treated as a priority.
📌 About This Work
This project was completed as part of my Cybersecurity Diploma Program at Vephla University, demonstrating practical skills in vulnerability assessment, penetration testing, and security analysis.
