A Case Study in Professional Vulnerability Disclosure
Severity: High (CVSS 8.6) Affected Platform: www[.]myroms[.]org Users Protected: 2,400+ researchers including federal agencies (NOAA, USGS) Status: ✅ MITIGATED (February 12, 2026) Disclosure Type: Coordinated responsible disclosure
TL;DR
I discovered a high-severity SQL injection vulnerability in Rutgers University's ROMS (Regional Ocean Modeling System) platform that could have provided complete unauthorized database access. Through professional collaboration with Rutgers security team, the vulnerability was successfully mitigated within 50 days. This disclosure demonstrates how responsible vulnerability research should work when both parties engage professionally.
Background: What is ROMS?
The Regional Ocean Modeling System (ROMS) is a widely-used ocean modeling platform serving the oceanographic research community. The platform at www.myroms.org provides:
- Software, Documentation and research tools
- Community forums and discussions
- Technical support
- Collaboration infrastructure
User Base:
- ~2,400 registered researchers
- NOAA scientists
- USGS researchers
- International university programs
- Marine science community
This platform is critical infrastructure for oceanographic research and climate modeling.
Discovery
On December 21, 2025, during security research on academic platforms, I identified a time-based blind SQL injection vulnerability in the ROMS login functionality.
Technical Details
Vulnerability Type: Time-based Blind SQL Injection Location: Login authentication Attack Vector: Network (remote) Authentication Required: None
Proof of Concept
Time-based payload confirmed the vulnerability:
POST /main.php?page=login HTTP/1.1
Host: target.com
Content-Type: application/x-www-form-urlencoded
username='XOR(SELECT(0)FROM(SELECT(SLEEP(8)))a)XOR'Z&password=test&but=LOGINExpected Response: <1 second Actual Response: 8+ second delay (vulnerability confirmed)
Database Access Confirmed
Automated testing revealed access to four databases:
ghauri -u "https://target.com/main.php?page=login" \
--data="username=*&password=&but=LOGIN" \
--technique=T --dbsResult:
information_schema- MySQL metadataforum- phpBB installation (74 tables)wiki- MediaWiki (2,418 user accounts)roms- Research data
Sensitive Data at Risk
The vulnerability could have exposed:
- User credentials (2,418 accounts with PBKDF2-hashed passwords)*
- OAuth authentication tokens
- Session identifiers
- Private forum messages
- Email addresses
- Access control lists
Note: Passwords were properly hashed using PBKDF2-SHA512 with 30,000 iterations — excellent security practice by the ROMS team.
Impact Assessment
CVSS 3.1 Score: 8.6 (High) Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:L
Affected Community:
- Federal agency researchers (NOAA, USGS)
- International oceanographic community
- Climate research programs
- ~2,400 registered users
Attack Requirements:
- No authentication needed
- Standard HTTP client
- Automated exploitation possible (<5 minutes)
Responsible Disclosure Process
Timeline:
Dec 21, 2025: Vulnerability discovered and reported to Rutgers
Dec 23, 2025: Vendor acknowledged (Ticket #1183986 assigned)
Jan 6, 2026: Initial mitigation deployed
Jan 7, 2026: Follow-up communication on defense layers
Jan 15, 2026: Vendor update on remediation progress
Feb 12, 2026: Final verification — Vulnerability mitigated
Feb 20, 2026: Formal acknowledgment received
Total Time: ~50 days from report to verified fix
Vendor Response (Rutgers/David Robertson):
- Acknowledged within 48 hours
- Created incident ticket immediately
- Assigned dedicated security resource
- Maintained open communication
- Implemented effective mitigations
- Coordinated verification testing
- Provided professional acknowledgment
Key Takeaways
What I learned:
- Professional communication works — Respectful engagement gets results
- Patience pays off — Vendors need time to fix properly
- Documentation matters — Keep detailed records
- Collaboration > confrontation — Working together achieves better outcomes
- Give credit generously — Acknowledge good vendor response
Special thanks to:
David Robertson, for professional engagement, effective remediation, and demonstrating how vulnerability disclosure should work.
Official Acknowledgment Letter from Rutgers University:
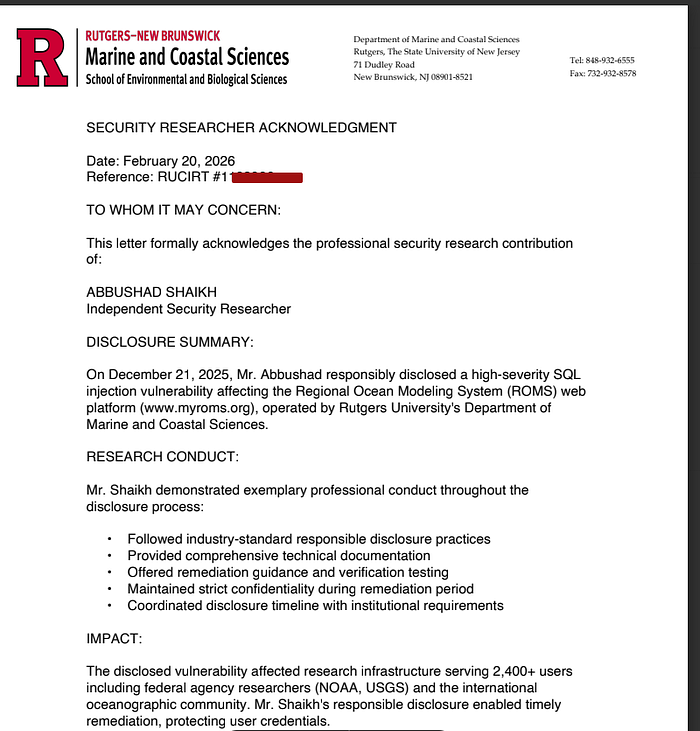

Thank you to David Robertson and Rutgers University for demonstrating excellent security practices and professional collaboration.
Disclaimer:
This research was conducted ethically following responsible disclosure practices. The vendor was given adequate time to remediate (50+ days). No user data was extracted, stored, or shared during research. All testing was conducted with minimal impact to the production system.
This disclosure is published with coordination from Rutgers University as a positive example of how vulnerability disclosure should work.
Abbushad Shaikh,
Security Researcher
