SQL Injection (SQLi) is one of the oldest web application vulnerabilities in cybersecurity history. It has been documented for over two decades, appears consistently in the OWASP Top 10, and is widely understood in both academic and professional circles. With modern frameworks, ORMs, DevSecOps pipelines, and AI-assisted coding tools, one might assume SQL injection would be obsolete by 2026.
However, this is not the case. Despite advancements in secure coding practices and security tooling, SQL injection continues to contribute to data breaches, compliance violations, and operational disruptions. The reason is a combination of legacy systems, human error, rapid development cycles, and evolving attack techniques despite intensive knowledge over the years.
A Brief History of SQL Injection
SQL injection emerged prominently in the early 2000s when dynamic web applications began directly embedding user input into database queries. Attackers discovered that by manipulating input fields, they could alter backend SQL queries, bypass authentication mechanisms, extract sensitive data, or even modify entire databases.
Over time, defensive techniques matured. Parameterized queries, prepared statements, stored procedures, and ORM frameworks were introduced to eliminate unsafe string concatenation. Web Application Firewalls (WAFs) became standard. Static and dynamic testing tools were integrated into development pipelines.
Assessing from a technical standpoint, one might assume SQL injection is patched. However…
Why SQL Injection Still Exists in 2026
1. Legacy Systems and Technical Debt: As opposed to always building from the ground up, many enterprises still operate applications developed 10 to 20 years ago. These systems may use outdated frameworks, unsupported libraries, or insecure coding practices that were common at the time.
Refactoring legacy codebases is expensive and risky. As a result, vulnerable query patterns often remain buried deep within business critical applications. Even when patches are applied, incomplete remediation leaves residual exposure.
Technical debt accumulates, and SQL injection vulnerabilities quietly persist.
2. Developer Mistakes and Misuse of Modern Tools:
Modern frameworks try and address this issue. but they do not eliminate risk entirely. Developers can still:
· Use raw SQL queries instead of parameterized methods
· Misconfigure ORMs
· Concatenate user input into dynamic queries
· Fail to validate input properly
In fast paced environments, security is sometimes treated as a secondary concern. Junior developers or teams without formal secure coding training may unknowingly introduce injection flaws.
3. Rapid Development and AI-Assisted Coding
In 2026, AI powered coding assistants are widely used. They accelerate development and reduce boilerplate effort. However, AI generated code is only as secure as the patterns it has learned.
If developers blindly trust generated code without review, insecure query construction can slip into production. The pressure to ship features quickly often reduces time allocated for security testing.
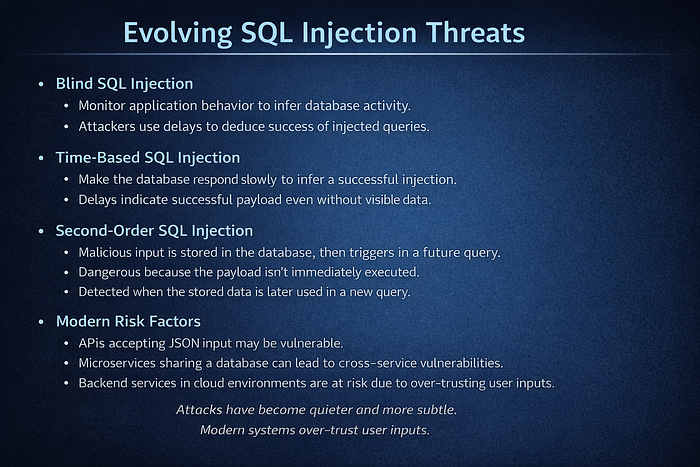
Evolving SQL Injection Threats
Real-World Impact in 2026
The consequences of SQL injection remain severe. Successful exploitation can lead to:
· Exposure of customer data
· Credential harvesting
· Manipulation of financial records
· Deletion or corruption of critical databases
Beyond immediate technical damage, organizations face regulatory penalties under data protection laws, reputational harm, and loss of customer trust.
In many cases, SQL injection serves as the initial breach that enables further compromise. Once database access is achieved, attackers can pivot, escalate privileges, or prepare environments for further malicious activity.
How Organizations Should Respond
The continued relevance of SQL injection highlights the need for foundational security discipline first, and then reliance on reactive controls later
Organizations should prioritize:
· Strict use of parameterized queries and prepared statements
· Secure coding standards embedded into development workflows
· Regular code reviews and secure development training
· Integration of SAST and DAST tools in CI/CD pipelines
· Database activity monitoring and anomaly detection
· DevSecOps practices that treat security as a shared responsibility
Conclusion
SQL injection may not be very sophisticated, yet it persists in 2026 because it exploits gaps in discipline, oversight, and organizational maturity. The tools to prevent it have existed for years. The knowledge is widespread. The documentation is clear.
What remains inconsistent is execution.
As long as legacy systems remain unchanged, development prioritizes speed over security, and secure coding practices are not rigorously enforced, SQL injection will continue to appear in breach reports. It reflects how seriously organizations treat secure software development.