Context
During a recent technical discussion within the CyberSphere Community, we examined a growing issue in modern cloud security: Identity Sprawl.
The focus was not on malware.
It was on access.
Not because cloud platforms are insecure by design.
But because the number of identities in modern environments is expanding faster than organizations can manage them.
The session was designed for beginners and cybersecurity learners who want to understand how unmanaged identities create hidden attack surfaces in cloud environments.
Session Objective
The discussion focused on:
Understanding what identity sprawl means in cloud environments Breaking down how unmanaged identities increase security risks Explaining how defenders can control identity growth effectively
What Identity Sprawl Really Means
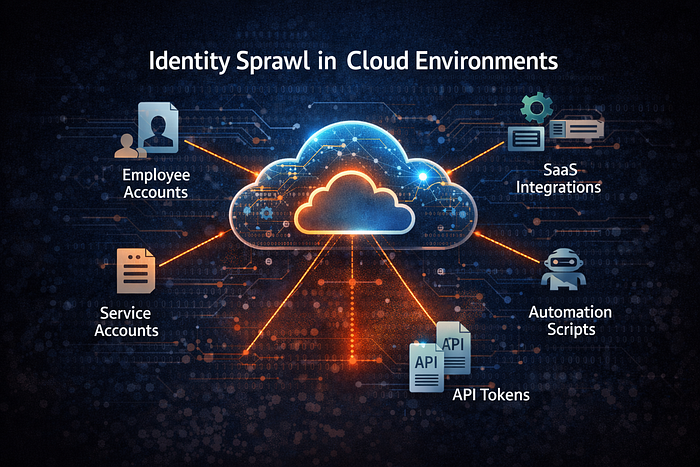
Identity sprawl occurs when the number of identities within an organization grows beyond proper visibility and control.
In modern cloud environments, identities are not limited to employees.
They include:
User accounts Service accounts Application identities API tokens Automation scripts Third-party integrations
Each identity represents a potential entry point into the system.
When these identities are not properly tracked, they create hidden security risks.
Why Identity Sprawl Happens
Cloud environments grow quickly.
New applications, services, and integrations are constantly added.
Common causes of identity sprawl include:
Rapid cloud adoption Temporary accounts that are never removed Service accounts with excessive privileges Unused API tokens Third-party SaaS integrations
Access is often granted quickly to support productivity.
But it is rarely removed once it is no longer needed.
The Four Risks of Identity Sprawl
1. Forgotten Accounts
Inactive user accounts or service accounts may remain active long after they are needed.
Attackers actively search for these forgotten identities because they often have:
Weak monitoring Outdated credentials Unrestricted access
Unused accounts still provide access.
2. Excessive Permissions
When identities accumulate over time, permission reviews become less frequent.
Accounts may end up with:
Broad administrative privileges Access to multiple systems Permissions beyond their original purpose
This increases the risk of privilege escalation.
3. Unmonitored API Tokens
Cloud services rely heavily on API authentication.
Many systems generate:
Access tokens Automation credentials Integration keys
If these tokens are not rotated or revoked regularly, attackers can gain persistent access.
4. Third-Party Integration Risks
Organizations often integrate external services with their cloud infrastructure.
Examples include:
Analytics platforms Automation tools Collaboration services
These integrations create additional identities that may not be regularly reviewed.
Why Identity Sprawl Still Happens in 2025
Despite improved identity management tools, organizations still struggle with:
Poor visibility into identities across platforms Lack of regular access reviews Weak identity lifecycle management Over-reliance on automated account creation Limited monitoring of service accounts
Cloud environments expand rapidly.
Identity governance often struggles to keep up.
What Defenders Should Actually Focus On
Instead of focusing only on infrastructure security, organizations must strengthen identity governance.
Effective strategies include:
Maintaining a complete inventory of identities Regularly reviewing access permissions Enforcing least privilege policies Rotating API tokens frequently Monitoring service accounts and automation identities
Security improves when identities become visible and controlled.
The Beginner Mindset Shift
If you are entering cybersecurity, understand this:
Modern attacks often begin with overlooked identities, not broken systems.
Attackers search for:
Unused accounts Over-permissioned identities Forgotten API keys
Identity governance is becoming one of the most critical areas in cybersecurity.
Key Takeaways
Identity sprawl creates hidden attack surfaces Unused accounts can still provide access API tokens and service identities require monitoring Cloud growth increases identity complexity Strong identity governance improves security visibility
Attackers do not always exploit software vulnerabilities.
Sometimes they simply find an identity that no one is watching.
Acknowledgement
Thanks to Harsh Kanojia, Founder of the CyberSphere Community, for encouraging structured discussions that focus on modern identity risks and practical cybersecurity awareness.
Author
Naman Shah Cybersecurity postgraduate focusing on secure systems, threat modeling, and applied security education.