It's easy to assume that modern web applications are fortified against the classic, low-hanging vulnerabilities of the past. As bug hunters, we often find ourselves digging deep into complex logic flaws, chaining multiple bugs just to get a single pop-up.
But every now and then, the internet reminds us to never forget the basics.
Recently, I stumbled upon both Cross-Site Scripting (XSS) and HTML Injection vulnerabilities in the wildest of places: an AI chatbot sitting directly on a company's Responsible Disclosure page.
Here is how a routine recon session turned into a perfect reminder to test absolutely everything.
The Reconnaissance
Like any standard hunting session, I started by mapping out the target. I landed on the company's Responsible Disclosure page and fired up Wappalyzer to get a feel for the underlying tech stack — checking out the CDN, CMS, and various frameworks in play.
Everything looked pretty standard and well-secured. Then, I noticed an interactive element: an AI-powered support chatbot meant to assist users with documentation and inquiries.
The Assumption vs. The Reality
When you see a modern chat widget, your first instinct is usually, "There's no way simple payloads are going to work here."
Nowadays, frameworks sanitize inputs by default. It's incredibly rare to find a basic, unfiltered text field in a production environment, especially on a page maintained by a security engineering team.
But a core rule of bug bounty hunting is: Never assume.
I decided to throw a few basic HTML and XSS payloads into the chat, just to see how the application would handle the input. I wasn't expecting much, but what happened next caught me off guard.
The Payloads That Triggered
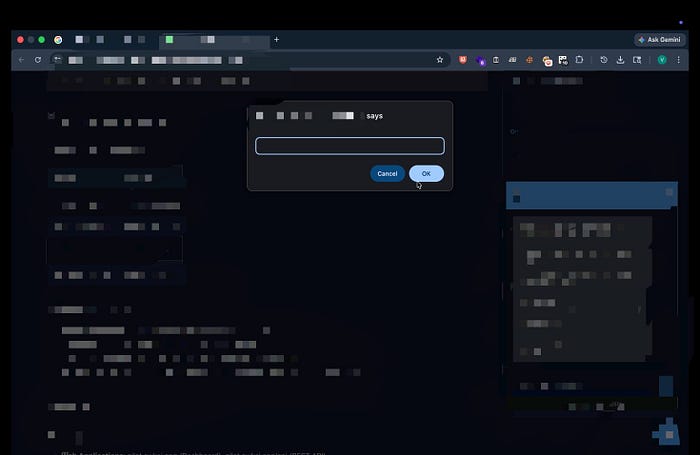
Instead of encoding or sanitizing the input, the chatbot reflected the payloads perfectly. The basic payloads I used didn't just bypass the filter — there was no filter.
Here are the exact payloads that executed successfully:
Basic HTML & XSS Injection
<font color="red">ERROR 1064(42000):You have an error in your SQL Syntax;
<img src/onerror=prompt(document.cookie)>
<button onClick="alert('xss')">Submit</button>
<a href="https://evil.com"> CLICK HERE </a>The chatbot rendered the fake SQL error in bright red text, the XSS prompts fired flawlessly, and the buttons and links became fully interactive elements inside the chat window.


The Takeaway: Test Everything
The irony of finding these vulnerabilities on a page dedicated to reporting vulnerabilities isn't lost on me. But beyond the humor of the situation, there is a vital lesson here for the infosec community.
Test each and every thing you find, whether it seems too simple or highly critical.
We often get so caught up looking for zero-days or complex bypasses that we skip the foundational tests. Developers make mistakes. WAFs get misconfigured. Sanitization libraries get overlooked. Just because an application looks modern doesn't mean the developer remembered to encode user input on every single component.
Don't let assumptions stop you from trying the simple stuff. Drop those basic tags into every input field you see. You might just get a pop-up where you least expect it.
Have you ever found a classic bug in a highly secure environment? Let me know in the comments! Keep hunting, and stay curious. 🛡️💻
