An on-ground investigation into a live mule account operation — with real screenshots, the complete money flow, and students whose bank accounts got frozen.
Cyb3r.Y4sh Note: This article is based on original field research conducted by me inside my college campus. Screenshots of the live app were obtained during the research. Student accounts have been anonymized to protect their privacy. The app described is currently active. This content is published solely for public awareness and cybercrime prevention.
The Numbers First
Stat Detail ₹10,000+ Deposited daily per student ₹300–500 Daily "earnings" shown in app 1 Semester How long students have been doing this PMLA The law they are unknowingly breaking
Walk through any college hostel in India right now.
You might find students hunched over their phones at 2 AM making UPI payments.
They are not paying bills. They are not shopping online.
They are unknowingly processing transactions for a criminal enterprise.
This is not a hypothetical warning. This is happening right now, on real campuses, with real students.
During my investigation, I identified a live application currently operating among students. — which shows users a "Deposit" screen with listings in INR and USDT, rewards called "InCoins," and a "Tool" section for linking payment apps like MobiKwik, Navi, Paytm, and Airtel Payments Bank, etc.
The students processing these payments believe they are earning. What they are actually doing is laundering money for online gambling syndicates, scammers, and cybercriminals — and when police trace the money, they find the students first.
"I thought it was like a business. You buy an order, someone pays you back. I was making ₹400 a day. I didn't know where the money was coming from." — College student, name withheld. Bank account frozen. Currently under inquiry.
@victim(mule account holder)
What the App Actually Looks Like
We obtained screenshots of the live app interface. Here is exactly what students see — and what it actually means:
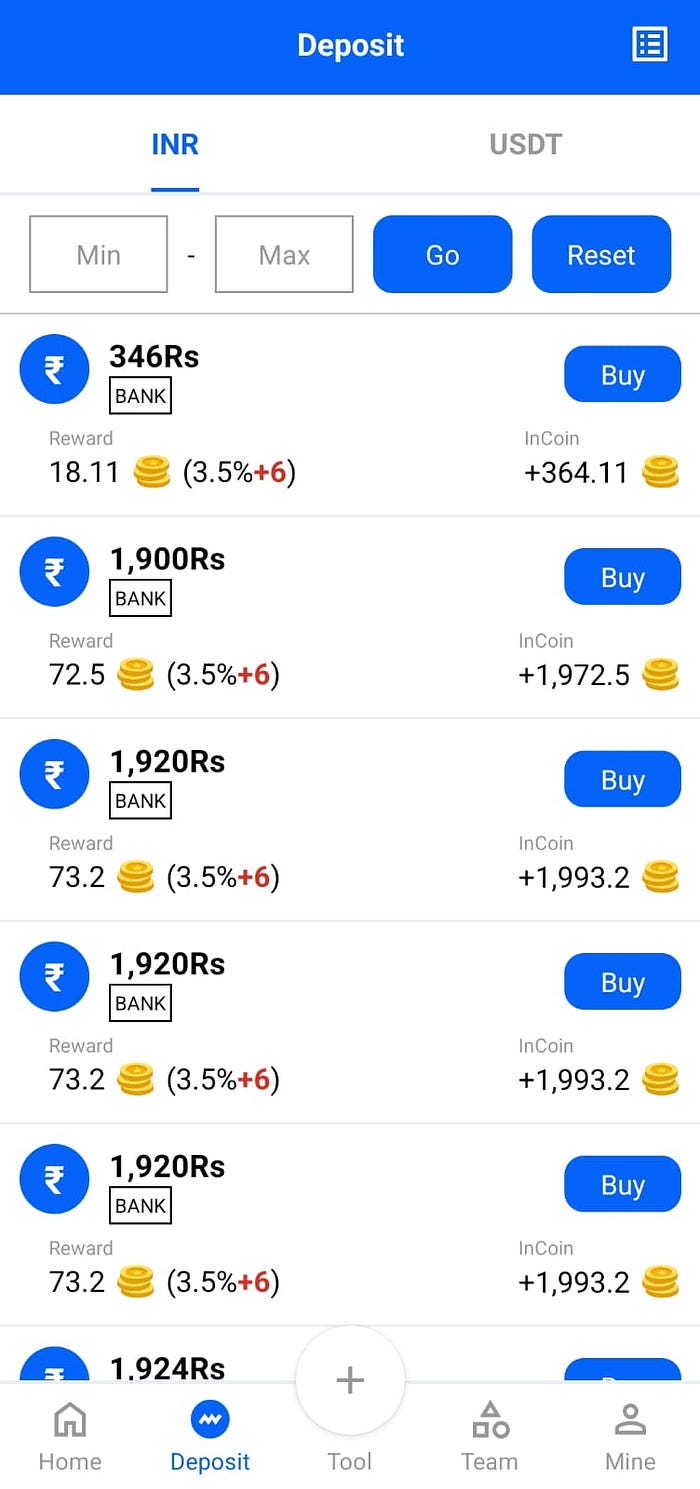
The "Deposit" Screen — Decoded
What the App Shows What It Really Is 346 Rs — BANK — Buy A victim's UPI deposit waiting to be routed through your account Reward: 18.11 🪙 (3.5%+6) Your cut for laundering the money — paid in fake "InCoins" InCoin: +364.11 🪙 A fake wallet balance designed to keep you hooked 1,900 Rs — BANK — Buy Another victim's payment — larger amount, same operation Tool → MobiKwik / Paytm / Airtel The channel to move illegal money through your UPI identity
The app has five sections: Home, Deposit, Tool, Team, and Mine. Every single one serves the criminal operation:
- Home — shows growing InCoin balance and daily "profit" to psychologically trap you
- Deposit — the core screen where laundering actually happens
- Tool — where you link your MobiKwik, Paytm, Airtel; your UPI becomes the crime evidence
- Team — referral system to recruit more students (spreads like MLM through hostels)
- Mine — wallet and withdrawals, almost always blocked or require more deposits to unlock
The Complete Money Flow — Exposed
This is the full chain our investigation mapped. Every layer is designed to put maximum distance between the criminal and the money — while putting students directly in the line of fire.
😰 VICTIM
↓
Gambler or scam victim deposits on betting/fraud app
↓
📲 UPI PAYMENT
↓
Money sent to student's MobiKwik / Paytm / Airtel UPI ID
↓
📱 MULE APP (InCoin)
↓
Student "buys order," copies UPI details, uploads screenshot + UTR ID
↓
🎓 STUDENT MULE
↓
Payment processed through student's account — money moves
↓
🕵️ AGENT / MIDDLE LAYER
↓
Collects from multiple student mules, takes commission
↓
💀 REAL SCAMMER
Clean money received — 4 layers removed from sourceWhat police see when they investigate:
- Victim reports missing ₹346 → UPI trail leads to student's MobiKwik ID → Bank freezes student's account immediately → Criminal is 4 layers away and hard to trace
The student is always the most visible, most traceable link. And the most replaceable.
Step-by-Step: How a Transaction Actually Works
This is the exact process our investigation documented:
Step 1 — Open the Deposit Tab Student sees a list: ₹346, ₹1,900, ₹1,920, ₹1,924… Each has a "Buy" button. These are real UPI deposits from real victims of scam/gambling apps, waiting to be processed.
Step 2 — Tap "Buy" A popup appears with complete UPI payment details — the account that needs to receive the money. Student is shown the exact amount and UPI ID to pay.
Step 3 — Redirected to Tool App App redirects to whichever payment app the student linked (MobiKwik, Paytm, Airtel). Student copy-pastes the UPI details from the popup directly.
Step 4 — Student Makes the UPI Payment Payment goes through. This moves the victim's money through the student's payment app — creating a fresh layer in the laundering chain, with the student's name on it.
Step 5 — Screenshot + UTR Uploaded Student uploads payment confirmation screenshot and the UTR (Unique Transaction Reference) ID back into the app as "proof of completion."
Step 6 — App Marks "Credited" InCoin balance updates. Today's earning increases. Student feels paid and satisfied. They are actually being used as a human money-routing node.
Step 7 — Money Comes Back (The Trap) Another mule somewhere pays the student back their original amount. So the student's account shows normal-looking inflow and outflow. To a casual glance, it looks like regular transactions — until police look closer.
The Calls Nobody Expected
One of the most revealing parts of this investigation: what happens outside the app.
Victims of the original gambling/fraud scam — who lost ₹1,920 or ₹346 or ₹1,900 — can see in their UPI transaction history exactly which UPI ID their money went to. Many of them call that number directly.
Students started receiving calls from strangers saying: "Tune mera paisa kahan bheja? Maine tujhe kuch nahi bheja — yeh transaction kyun hui?"
The students had no answer. They processed the payment because the app told them to. They had no idea the money came from a scam victim. Most ignored the calls, assuming it was a mistake.
Some students received multiple such calls in a week — all from different people, all asking about different transactions. The pattern should have been a warning. For most, it wasn't.
"My friend got his account frozen during exam week. All his money — savings, pocket money, everything — locked. He couldn't even buy food for 3 days while his parents sorted it out." — Fellow student describing the aftermath
What Happens When the Bank Account Gets Frozen
When a victim reports the UPI ID to cybercrime police, the linked bank account is frozen immediately under Section 102 CrPC. This means:
- Every rupee in the account is locked — scholarship money, savings, pocket money, everything
- The freeze can last days to months depending on the investigation
- The student must prove their innocence to unfreeze it
- This process usually requires a lawyer and multiple police visits
- A criminal charge under PMLA is possible even for unknowing participants
Several students on the campus I visited had already experienced account freezes. None of them had reported the app. Even after the freeze was lifted, they continued using it — because they needed the money to get through the month.
Why Smart Students Fall For This
Understanding why this works on intelligent people is essential to stopping it:
It looks exactly like a legitimate app. The interface mimics real fintech platforms. There is no obvious red flag on first use.
Initial payments work flawlessly. Money comes back, InCoin balance grows, trust builds over weeks before any problem appears.
Social proof inside the hostel. When three friends are already doing it and nothing bad has happened yet, the risk feels theoretical.
The "commission" framing. Students think they're being paid a fee for processing payments — not realizing the payments are criminal proceeds.
Small individual amounts. ₹346 or ₹1,920 per transaction doesn't feel like serious money. The scale doesn't register.
Gradual escalation. Students start with one or two transactions. Over a semester, they're doing 10–15 per day.
The math doesn't lie: Processing ₹10,000/day for ₹400 commission is a 4% rate. Legitimate payment processors charge 0.5–2% and they are registered RBI-licensed businesses. Anyone offering you 3–5% to "just process payments" is paying you for the legal liability you are absorbing on their behalf.
The Legal Reality
If police investigate, these are the charges student mules can face:
PMLA Section 3 — Money laundering: 3–7 years imprisonment, fines up to ₹5 lakh
IT Act Section 66C — Identity fraud using someone else's UPI credentials in transactions
BNS Section 318 — Cheating and dishonestly inducing delivery of property
Section 102 CrPC — Bank account seizure, immediate and without prior notice
"I didn't know" is a partial defense — not a complete one. Courts expect you to explain why you were routing money for strangers without understanding why. Proving you were deceived requires evidence, a lawyer, time, and money — none of which most students have readily available.
If You or Someone You Know Is Doing This — Stop Today
Immediate steps:
✅ Stop processing all transactions right now
✅ Unlink all payment apps from the Tool section — remove MobiKwik, Paytm, Airtel
✅ Do NOT delete the app or chats yet — this is evidence you may need
✅ Go to your bank proactively — report that your UPI may have been used for suspicious activity. Self-reporting protects you legally
✅ File a complaint at cybercrime.gov.in — reporting yourself as a victim/unknowing participant is treated very differently than being caught
✅ Consult a criminal lawyer before giving any statement to police
✅ Save everything — app screenshots, transaction IDs, chat records, the name of whoever recruited you
✅ Tell your parents — before police contact them instead
A Note to Every Student Reading This
You are not stupid if you got into this. These apps are engineered by professional criminals who have refined their tactics over years. They use college students deliberately — because you are digitally fluent, financially motivated, and embedded in large social networks through hostels and friend circles.
The people running this operation have never met you. They will not protect you when law enforcement comes. You are the most visible link in the chain — and the most replaceable.
The ₹400 per day is not worth a frozen bank account, a semester disrupted, a criminal record, or your parents receiving a call from the police.
Share this article. Show it to the people you know who are doing this. The best outcome of this research is that one student stops today.
Report It
📞 1930 — National Cyber Helpline (24x7, free)
🌐 cybercrime.gov.in — File online complaint with screenshots
🏦 Your bank's fraud desk — Report UPI misuse directly
🔒 cert-in.org.in — Report the app to India's cybersecurity authority
This investigation was conducted for public awareness and cybercrime prevention. All student identities have been anonymized. App screenshots were obtained ethically during field research. No illegal activity was performed or facilitated during this investigation.
⚠️This research was conducted strictly for awareness and educational purposes. No transactions were performed by the researcher and no financial activity was initiated during this investigation.
Tags: #Cybercrime #MoneyMule #UPIFraud #CollegeStudents #CyberAwareness #InCoinScam #BankFreeze #PMLA #OnlineFraud #IndiaScam #CyberSafety #StudentSafety

