Let me ruin your Monday with a fun statistic: 43% of cyberattacks target small businesses. And by "fun," I mean the kind of fun where you realize you left your front door wide open in a neighborhood full of people who really, really like your stuff.
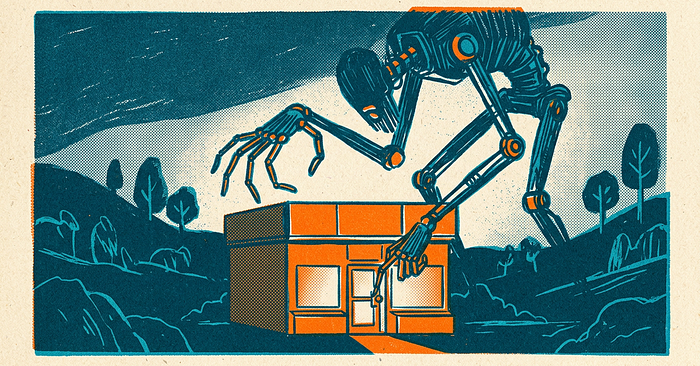
Here's the thing — if you're running a small business and you've ever thought "we're too small for hackers to care about," I get it. That logic feels right. Why would some shadowy figure in a hoodie bother with your 15-person company when Fortune 500 companies are right there?
Because Fortune 500 companies have entire teams of people whose sole job is to stop that hoodie-wearing individual. You probably don't. And hackers know this.
You're Not the Target — You're the Opportunity
Most cyberattacks against small businesses aren't some mastermind personally selecting your company from a list. They're automated. Bots scan the internet looking for unpatched software, weak passwords, and misconfigured servers the way a burglar walks down a street checking door handles.
Your business doesn't need to be interesting. It just needs to be unlocked.
The Greatest Hits of Small Business Attacks
Let's talk about what actually happens out there. These aren't hypothetical — they're the attacks I see hitting small businesses over and over again.
Phishing (Still the GOAT)
Someone on your team gets an email that looks like it's from Microsoft, their bank, or even you. They click a link, enter their credentials, and now an attacker has the keys to your kingdom. Phishing accounts for over 80% of reported security incidents, and it works because humans are trusting creatures. Bless our hearts.
What to do: Train your team to spot phishing. Not once — regularly. Make it part of the culture. And please, for the love of all that is holy, turn on multi-factor authentication (MFA) everywhere you can.
Ransomware
An attacker encrypts all your files and demands payment to give them back. For a large enterprise, that's a bad quarter. For a small business, that can be a closing-the-doors event. The average ransomware payment for small businesses is north of $100,000 — and paying doesn't even guarantee you'll get your data back.
What to do: Back up your data. Then back up your backups. Use the 3–2–1 rule: three copies, two different media types, one offsite. And test your restores, because a backup you've never tested is just a hope and a prayer with a hard drive attached.
Business Email Compromise (BEC)
This one's elegant in a way that's infuriating. An attacker compromises or spoofs a business email account — usually someone in leadership — and sends a convincing message to an employee: "Hey, can you wire $47,000 to this vendor? It's urgent." The employee, wanting to be helpful, does it. The money vanishes.
What to do: Establish verification procedures for any financial transaction. If the CEO emails asking for a wire transfer, pick up the phone and call them. Every. Single. Time.
The Basics That Actually Work
I know "the basics" sounds boring. Nobody got into business to configure firewalls. But here's the irony — the basics stop the vast majority of attacks. We're not talking about building a digital fortress. We're talking about locking the door and turning on the porch light.
- Keep software updated. Those annoying update notifications? They're patching security holes. Stop hitting "remind me later."
- Use strong, unique passwords. Get a password manager. Yes, for the whole team. No, "Company123!" is not acceptable.
- Enable MFA on everything. Email, banking, cloud services — all of it. MFA stops 99.9% of automated attacks according to Microsoft. That's not a typo.
- Limit access. Not everyone needs admin rights. Give people access to what they need and nothing more. It's called the principle of least privilege, and it's your best friend.
- Have an incident response plan. Know what you'll do before something happens. Who do you call? What do you shut down? Where are your backups? Figuring this out during an attack is like reading the fire extinguisher instructions while the kitchen is on fire.
You Don't Have to Do This Alone
Look, I'm not going to pretend this is simple. You're already wearing twelve hats running your business — adding "cybersecurity expert" to the stack isn't realistic for most people. But ignoring it isn't an option either, because the attackers aren't going to ignore you.
If you're feeling overwhelmed, that's normal. Start with the basics above. Pick one thing from this list and do it this week. Then pick another one next week. Progress beats perfection.
And if you want someone to handle small business cybersecurity so you can get back to actually running your business, that's a completely valid move too. The important thing is that something gets done — because the cost of doing nothing is the one price no small business can afford.
Stay safe out there. And maybe go change that password you've been reusing since 2017. You know the one.