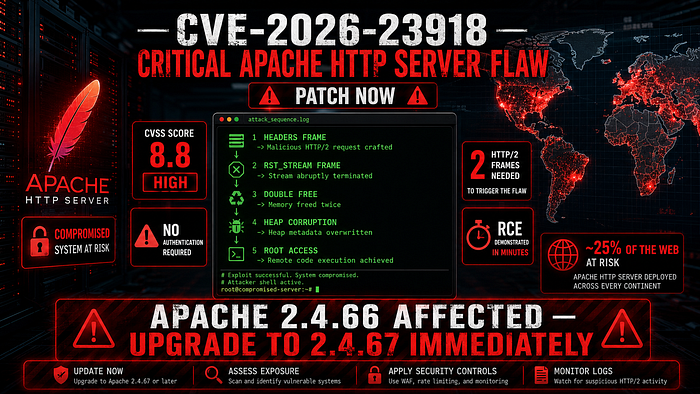
CVSS 8.8. One TCP connection. Two crafted HTTP/2 frames. No authentication. Worker process crashed. And in the right conditions — full remote code execution. If you run Apache 2.4.66, stop reading and patch first.
Apache HTTP Server powers roughly a quarter of the active web. It is the default web server on Debian, Ubuntu, Red Hat, and virtually every major Linux distribution. It runs in enterprise data centres, cloud environments, containerised deployments, and millions of small business servers. When a critical vulnerability lands in Apache, the attack surface is not large — it is enormous.
On May 4, 2026, the Apache Software Foundation released version 2.4.67, patching eleven vulnerabilities across the HTTP Server. The most severe is CVE-2026–23918 — a double-free memory corruption flaw in the HTTP/2 handling module that enables denial-of-service with trivial effort and remote code execution under conditions that researchers demonstrated successfully in a lab environment within minutes.
The vulnerability was discovered by Bartłomiej Dmitruk, co-founder of Striga.ai, and Stanisław Strzałkowski, a researcher at ISEC.pl. If you are running Apache HTTP Server 2.4.66 with HTTP/2 enabled in a multi-threaded configuration — you are exposed right now.
What CVE-2026–23918 Actually Is
CVE-2026–23918 is a double-free vulnerability in Apache's mod_http2 module — specifically in the stream cleanup path of h2_mplx.c. A double-free occurs when a program attempts to free the same memory region twice. In languages like C, this corrupts the heap allocator's internal state and can produce unpredictable behaviour ranging from a crash to arbitrary code execution.
The trigger sequence is deceptively simple. An attacker sends a HEADERS frame immediately followed by a RST_STREAM frame on the same HTTP/2 stream — before the server has fully registered that stream internally. This causes the server to perform duplicated cleanup operations on the same stream, freeing the same pointer twice. The result is heap corruption.
What makes this particularly dangerous is the attack surface. The mod_http2 module ships in default Apache builds. HTTP/2 is widely enabled in production deployments for performance reasons. And the exploit requires no authentication, no special configuration, and no prior access to the target system.
The Two Exploitation Paths
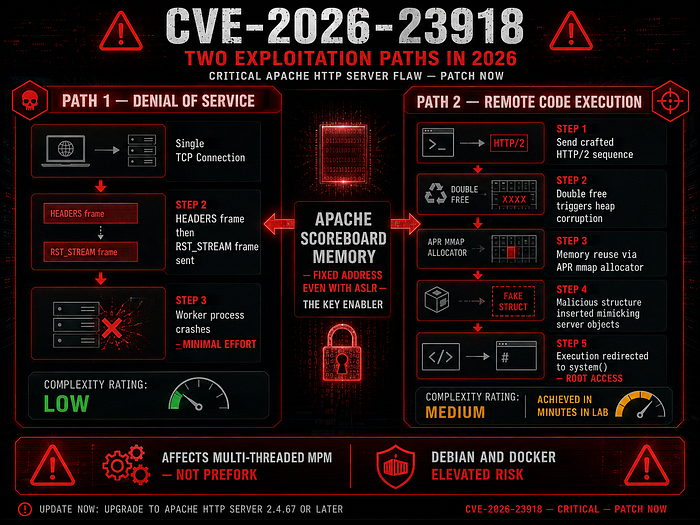
Path 1 — Denial of Service (Low Barrier) The DoS scenario requires a single TCP connection and two specially ordered HTTP/2 frames. No authentication. No special configuration. No dependencies. The crafted sequence crashes a worker process in Apache's multi-threaded configurations. While Apache automatically respawns crashed workers, repeated exploitation creates sustained service disruption. In high-traffic environments, automated exploitation at scale can effectively take a server offline.
Path 2 — Remote Code Execution (Higher Complexity) The RCE path is more complex but researchers demonstrated successful exploitation in lab conditions within minutes. The attack chain leverages memory reuse via the Apache Portable Runtime — particularly when configured with an mmap-based allocator, which is common in Debian-based systems and official Docker images.
The attack works by manipulating memory allocation patterns to reuse freed memory regions, inserting a malicious structure that mimics internal server objects, and redirecting execution flow to system-level functions such as system(). The critical enabler is Apache's scoreboard memory — a persistent shared memory region that maintains a stable address throughout the server's lifetime, even with ASLR enabled.
Dmitruk explained: "The scoreboard sits at a fixed address for the lifetime of the server, even with ASLR, which is what makes the RCE path practical. The usual caveats apply: practical exploitation requires an info leak for system() and the scoreboard offsets, and the heap spray is probabilistic, but in lab conditions execution lands in minutes."
Which Configurations Are Affected
Not every Apache deployment is equally exposed. The MPM prefork configuration is NOT affected — the vulnerability only impacts multi-threaded configurations. However, multi-threaded configurations are standard in high-performance environments and the majority of modern Apache deployments. Prefork is increasingly rare in production infrastructure due to its performance limitations.
The affected configuration profile is: Apache HTTP Server version 2.4.66, with mod_http2 loaded, running in a multi-threaded MPM configuration — worker or event MPM. This describes the majority of production Apache deployments running modern HTTP/2-enabled infrastructure. Systems using mmap-based allocators — Debian-based systems and official Docker images specifically — face elevated RCE risk due to the memory layout characteristics the exploit relies on.
The Other Four Vulnerabilities Patched
CVE-2026–23918 is the most severe but not the only vulnerability addressed in 2.4.67. Four additional flaws were patched simultaneously — and security researchers note that attackers frequently chain lower-severity vulnerabilities with high-severity ones to increase exploitation reliability.
CVE-2026–28780 — A heap-based buffer overflow in mod_proxy_ajp via ajp_msg_check_header(). If mod_proxy_ajp connects to a malicious AJP backend server, that server can send a crafted AJP message causing the module to write four attacker-controlled bytes beyond the end of a heap buffer. Reported independently by four researchers between February and March 2026.
CVE-2026–29168 — Resource exhaustion in mod_md through oversized OCSP responses. Attackers can exhaust server resources via oversized OCSP response data. Affects versions 2.4.30 through 2.4.66.
CVE-2026–29169 — A NULL pointer dereference in mod_dav_lock enabling server crashes via crafted requests. mod_dav_lock is not used internally by mod_dav or mod_dav_fs — its only known use case is with mod_dav_svn from Apache Subversion versions prior to 1.2.0. Most modern deployments do not need this module at all.
CVE-2026–24072 — A moderate privilege escalation in mod_rewrite. Allows local .htaccess authors to read arbitrary files with the full privileges of the httpd user — effectively breaking out of their restricted environment. Affects Apache HTTP Server 2.4.66 and earlier.
Immediate Actions — In Priority Order
Action 1 — Upgrade to Apache HTTP Server 2.4.67 immediately. This is the only complete fix for all eleven vulnerabilities. There is no partial mitigation that addresses all risks simultaneously. The upgrade is the only correct response.
Check your current version:
httpd -v # or apache2 -v
Action 2 — Disable HTTP/2 temporarily if immediate upgrade is not feasible. This blocks the primary RCE and DoS vector for CVE-2026–23918 while you plan the upgrade. In your Apache configuration:
Protocols http/1.1 # Remove or comment out: # Protocols h2 http/1.1
Important: Disabling HTTP/2 does not protect against CVE-2026–28780, CVE-2026–29168, CVE-2026–29169, or CVE-2026–24072. You still need to upgrade.
Action 3 — Remove mod_dav_lock if not in active use. If you are not running legacy Apache Subversion with mod_dav_svn versions prior to 1.2.0, this module serves no purpose in your deployment and removing it eliminates CVE-2026–29169 exposure entirely.
Action 4 — Audit .htaccess permissions. Tighten permissions to block the CVE-2026–24072 privilege escalation. Review which users can write .htaccess files and restrict to the minimum required.
Action 5 — Prioritise Debian-based and Docker deployments. The mmap-based allocator common in these environments elevates RCE risk. These systems should be patched first in any staged rollout.
Detection and Monitoring
While patches are being applied, monitor Apache access logs for unusual HTTP/2 connection patterns — specifically connections that send RST_STREAM frames immediately after HEADERS frames at high frequency. This pattern is not typical of legitimate client behaviour and may indicate active exploitation attempts.
Apache worker process crashes — visible in error logs as segfaults or abnormal process terminations — should be treated as potential exploitation indicators given the current vulnerability disclosure. Any pattern of repeated worker restarts warrants immediate investigation.
Apache runs on roughly a quarter of the active web. These are not obscure edge-case bugs. The window to patch before attackers start scanning is shorter than most admins would like. — The CyberSec Guru, May 2026
CVE-2026–23918 is a serious vulnerability in one of the most widely deployed pieces of software on the internet. The DoS path is trivially simple. The RCE path is demonstrated. The patch is available. The action required is unambiguous: upgrade to Apache HTTP Server 2.4.67 immediately, prioritise Debian-based and Docker environments, and treat any worker process crashes as potential indicators of active exploitation until patching is confirmed complete across your infrastructure.