Overview
During further security testing of the SourceCodester Resort Reservation System (PHP + SQLite), an additional stored cross-site scripting (XSS) vulnerability was identified within the Reservation Management module.
The application fails to sanitize or properly encode user-supplied input in reservation-related fields. As a result, malicious JavaScript injected into reservation data is stored in the database and executed when rendered in administrative interfaces.
This vulnerability allows authenticated users to execute arbitrary JavaScript in the context of other users, including administrators.
Affected Application
- Product: Resort Reservation System
- Vendor: SourceCodester
- Technology Stack: PHP, SQLite
- Affected Module: Reservation Management
- Affected Parameters: Fullname
Vulnerability Details
The application provides functionality to create and update reservation records through:
?page=manage_reservation&id=<reservation_id>Input fields such as Fullname and Remarks accept arbitrary user input. These values are stored directly in the database and later displayed in reservation listings and management pages without output encoding.
Because the application renders stored values directly into the HTML context, injected <script> tags are interpreted and executed by the browser.
This results in a persistent (stored) XSS vulnerability.
Proof of Concept
Step 1 — Inject Payload
Navigate to:
Reservation List → Add/Edit ReservationInsert the following payload into the Fullname field:
<script>alert('XSS Test2')</script>Alternatively, the same payload may be inserted into the Remarks field.
Save the reservation.
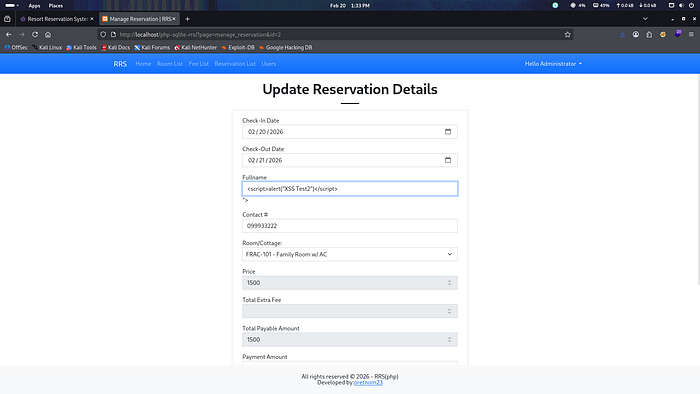
Step 2 — Trigger Execution
When accessing:
Reservation Listor when opening the reservation for editing, the injected script executes automatically.
The alert dialog confirms successful JavaScript execution within the application context.

Root Cause Analysis
The vulnerability is caused by:
- Direct storage of unsanitized user input
- Rendering database content without
htmlspecialchars()or equivalent encoding - Lack of contextual output escaping in PHP templates
The application prints user-controlled data directly into HTML without neutralizing script tags.
Impact
This vulnerability enables persistent JavaScript execution against any user viewing affected reservation records.
Potential consequences include:
- Administrative session hijacking
- Privilege escalation
- Unauthorized modification of reservations
- Data exfiltration
- Account takeover
- Persistent UI manipulation
If a lower-privileged user can submit reservation data that administrators later review, the risk increases significantly.
CVSS v3.1 Assessment
Base Score: 6.5 (Medium)
Vector: CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:L/A:N
Severity may increase depending on role-based access control and deployment exposure.
Remediation
To properly mitigate this issue, the following controls should be implemented:
1. Output Encoding (Primary Fix)
All user-controlled data must be encoded before rendering:
echo htmlspecialchars($fullname, ENT_QUOTES, 'UTF-8');Apply consistently to:
- Fullname
- Any database-rendered reservation fields
2. Input Validation
Restrict HTML input where not required:
$fullname = strip_tags($_POST['fullname']);3. Content Security Policy (CSP)
Implement a restrictive CSP header:
Content-Security-Policy: default-src 'self';4. Secure Session Configuration
Set session cookies with:
- HttpOnly
- Secure
- SameSite=Strict
Detection Guidance
Developers should review all PHP templates where database values are echoed directly:
<?= $variable ?>Replace with:
<?= htmlspecialchars($variable, ENT_QUOTES, 'UTF-8') ?>A systematic review of all output contexts is recommended.
Conclusion
This finding, together with the previously identified XSS in the Room Management module, indicates a broader pattern of insufficient output encoding across the application.
Because the vulnerability is persistent and affects administrative workflows, it poses a meaningful risk in real-world deployments. Proper output encoding and input validation practices should be implemented consistently throughout the codebase to prevent further injection vulnerabilities.
