Introduction
In this lab from the PortSwigger Web Security Academy, we explore a classic Insecure Direct Object Reference (IDOR) vulnerability.
The application stores chat transcripts directly on the server and allows users to access them via predictable URLs. This creates a serious security flaw where attackers can access sensitive data simply by modifying file names.
Lab Overview
Lab Title: Insecure Direct Object References Difficulty: Apprentice
Vulnerability Type
- IDOR (Insecure Direct Object Reference)
- Sensitive Data Exposure
The application uses static, incrementing filenames (e.g., 2.txt, 3.txt) to store chat logs, without proper authorization checks.
Steps to Exploit
1. Access Live Chat
- Navigate to the Live chat feature.
- Send any message.
2. View Transcript
- Click on "View transcript" after sending the message.
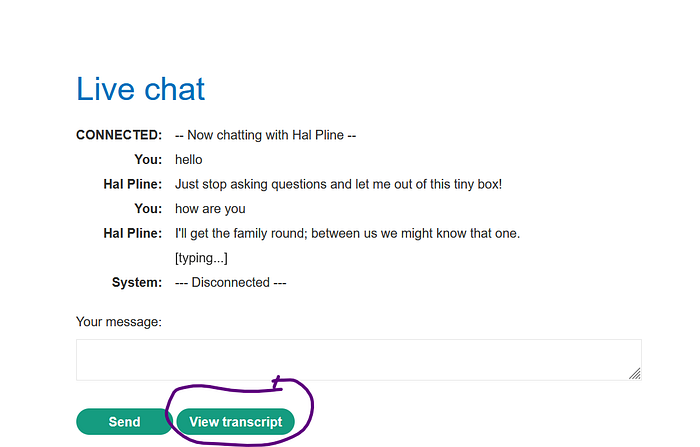
- Observe the URL: /download-transcript/2.txt
3. Identify the Pattern
- The transcript files follow a simple numeric pattern:
1.txt, 2.txt, 3.txt ...👉 This is a major red flag — predictable object references.
4. Exploit the IDOR
- Modify the URL manually:
/download-transcript/1.txt- Access the file.
5. Extract Credentials
- Inside the transcript, you will find sensitive data:
- Username: carlos
- Password: (exposed in chat log)
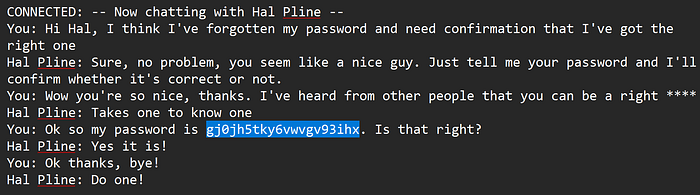
6. Login as Carlos
- Go back to the login page.
- Use the stolen credentials.
- ✅ Lab solved.
Key Takeaways
Why This Is Dangerous
- No authorization checks on file access
- Predictable file naming system
- Sensitive data stored in plain text
- Direct access to internal resources
Conclusion
This lab highlights how small design mistakes — like predictable file names — can lead to full account compromise.
IDOR vulnerabilities are simple but extremely powerful. As a penetration tester, always check:
- URL parameters
- File paths
- Object references
Because sometimes, just changing a number is enough to break the system.
