In early 2026, a severe vulnerability rocked the cybersecurity world: CVE-2026–1731, affecting BeyondTrust's Remote Support (RS) and Privileged Remote Access (PRA) products.
This pre-authentication remote code execution (RCE) flaw allows attackers to run arbitrary commands on affected systems without logging in, potentially leading to full compromise. Discovered in late January 2026 and patched shortly after, it quickly saw in-the-wild exploitation. With a CVSS v3.1 score of 9.9 (Critical: Attack Vector: Network; Attack Complexity: Low; Privileges Required: None; User Interaction: None; Scope: Unchanged; Confidentiality: High; Integrity: High; Availability: High), it's a prime example of how command injection bugs in enterprise tools can expose sensitive environments. This post breaks down the vuln, its mechanics, a POC, impacts, and fixes.
Vulnerbility
CVE-2026–1731 is an OS command injection vulnerability (CWE-78) in the "thin-scc-wrapper" component of BeyondTrust RS and PRA. It stems from unsafe handling of user input in a Bash script accessible via a WebSocket endpoint. Attackers can craft malicious requests to inject and execute commands as the site user, bypassing authentication entirely. Affected versions include RS up to 25.3.1 and PRA up to 24.3.4.
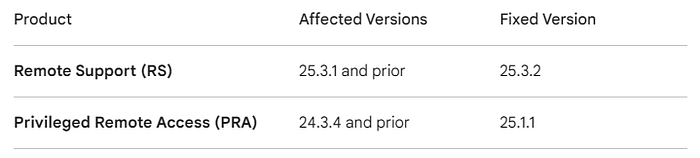
Impacted Versions & Fixes
BeyondTrust patched their SaaS instances automatically in early February, but on-premise setups are high-risk targets.
Technical Analysis
The root cause lies in a Bash script that performs an arithmetic comparison on the "remoteVersion" field sent during a WebSocket handshake. Bash treats operands in expressions like [ "$remoteVersion" -eq 0 ] as arithmetic, not strings, leading to evaluation of embedded commands.
For instance, if an attacker sends "hax[$(id)]0" as remoteVersion, Bash evaluates $(id) first running the "id" command before the comparison. This allows arbitrary command substitution via $(cmd). Importantly, this is a blind command injection: the server executes the injected command but does not return or reflect any output in the WebSocket response. Attackers must confirm success via out-of-band techniques (e.g., reverse shells, HTTP/DNS beacons, or filesystem changes), which is why real-world exploits often drop webshells or malware droppers without immediate visible feedback.

Effect of the Vulnerability
This flaw enables unauthenticated attackers to gain control over BeyondTrust appliances, leading to data theft, lateral movement in networks, or deployment of malware like VShell and SparkRAT (observed in exploits). Impacts include unauthorized access to privileged sessions, exfiltration of sensitive info, and service denial. Self-hosted, internet-facing instances were hit hardest, with exploitation starting February 10, 2026, risking breaches in enterprises relying on these tools for remote access.
Fix
BeyondTrust released patches on February 2, 2026: Apply BT26–02-RS for RS (upgrade to 25.3.2+) and BT26–02-PRA for PRA (upgrade to 25.1.1+). SaaS users are auto-patched; self-hosted admins should update via /appliance and enable automatic updates. For older versions, full upgrades are required. Monitor for compromise and contact support if exposed pre-patch. Always restrict internet exposure and use network segmentation.