This one I found on a website which has profile photos of accounts, and where the photo you upload does not strip the EXIF metadata and had geoloaction data gettable from the photo.
So the thing that happened is I was checking out the application, i setup my account there and added a photo for my profile, and I got to know that the profile picture URL looks like:
https://subdomain.redacted.com/Accounts/somedirectory/testuser@mail.com/ProfileImages/imgfile.jpgThis was the point I thought, what would happen if this were publicly accessible, and I copied the link and pasted it in a private window, and it was publicly accessible.
So I confirmed that I can check for EXIF data not stripped, so I went to the website to check for EXIF data from the img :
https://exifinfo.org/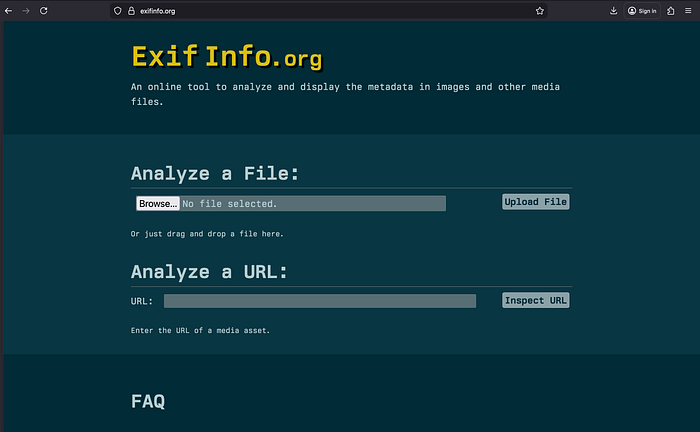
I put the URL in here and got the EXIF data as it was getting stripped from the server side:
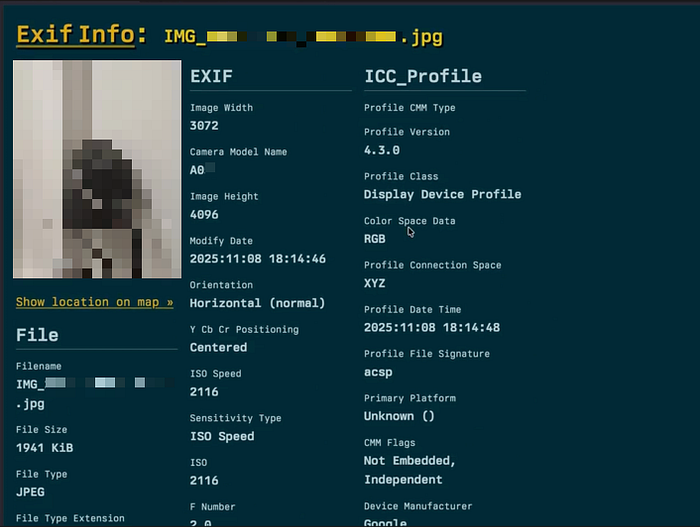
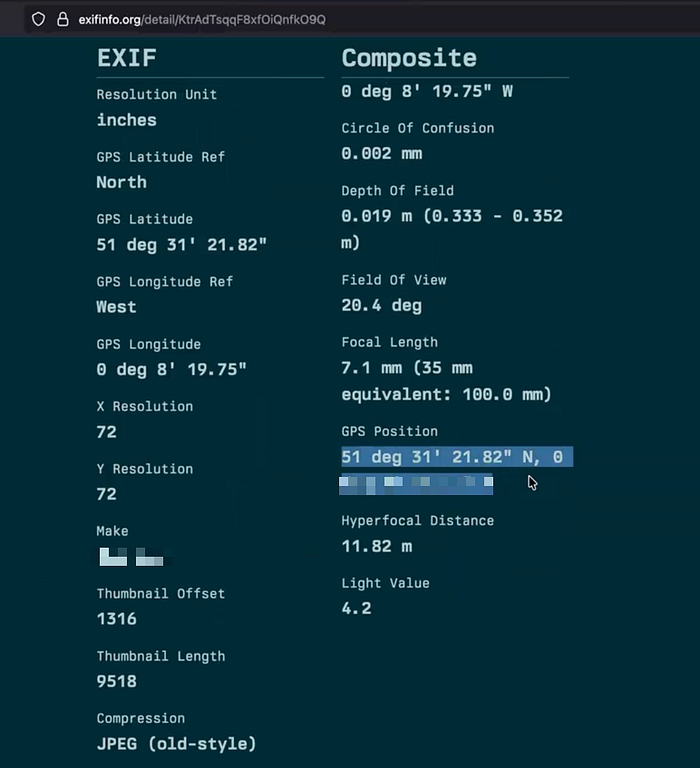
So you can see here I got the GPS position Maker of the phone, and the camera model name as well. Also, I checked that using this GPS data i can find the exact position if I put that into Google Maps. You can check that for yourself using your data. I am not gonna show that.
After I got these, I started with the POC, so the steps were:
- Log in to the student portal and navigate to: https://subdomain.redacted.com/somedirectory/myprofile.aspx
- Copy the direct image URL, e.g.: https://subdomain.redacted.com/Accounts/somedirectory/testuser@mail.com/ProfileImages/imgfile.jpg
- Log out or open an incognito/private window.
- Paste the same URL into the browser —> the image loads successfully without authentication.
- Use the same URL on any Exif image extractor website, and you can see the GPS coordinates and the phone manufacturer and model as well.
So I reported straight away.
This is a simple bug you can find and report. Comment if you already found this bug in a program.
You can check out my other blogs and follow me for more bug bounty and cybersecurity content.
Stay curious. Stay dangerous. 💻🕶